Introduction
Boards and CEOs regularly misfire on which technology leader they actually need—hiring a CTO when they need a CIO, or skipping the CISO entirely until a breach forces the issue. All three titles touch "technology," but each carries a fundamentally different mandate.
This post defines each role, clarifies how they interact, and helps boards and executive teams determine which leadership structure their organization actually needs — and what's missing if they get it wrong.
TL;DR
- CTO drives innovation, product development, and engineering, typically at organizations that build technology as their core offering
- CIO oversees enterprise IT strategy, operational efficiency, and digital transformation, typically at organizations that run technology to deliver their product
- CISO owns cybersecurity risk posture, compliance obligations, and incident response; reporting lines now often run directly to the CEO, General Counsel, or board committee
- All three roles are distinct but interdependent. Gaps between them create measurable governance and operational risk
- Every organization needs accountable leadership across innovation, IT operations, and cybersecurity — full-time, fractional, or defined ownership all count
| Role | Primary Focus | Core Mandate | Typical Reporting Line | How Success Is Measured |
|---|---|---|---|---|
| CTO | Outward-facing innovation | Product development, engineering, competitive differentiation | CEO or Board | Product innovation, time-to-market, customer adoption, revenue growth |
| CIO | Inward-facing operations | Enterprise IT strategy, operational efficiency, digital transformation | CEO or COO | Systems uptime, IT project delivery, cost efficiency, business operations alignment |
| CISO | Protective security posture | Cybersecurity risk management, compliance, incident response | CEO, General Counsel, or Board Committee | Risk reduction, incident response time, compliance status, breach cost avoidance |
What Is a CTO?
The CTO is the organization's technologist responsible for innovation, product development, and engineering—primarily in technology-creator organizations such as SaaS companies, fintech platforms, and digital product businesses. Unlike the CIO's internal orientation toward enterprise systems, the CTO focuses on building technology that customers purchase or use directly.
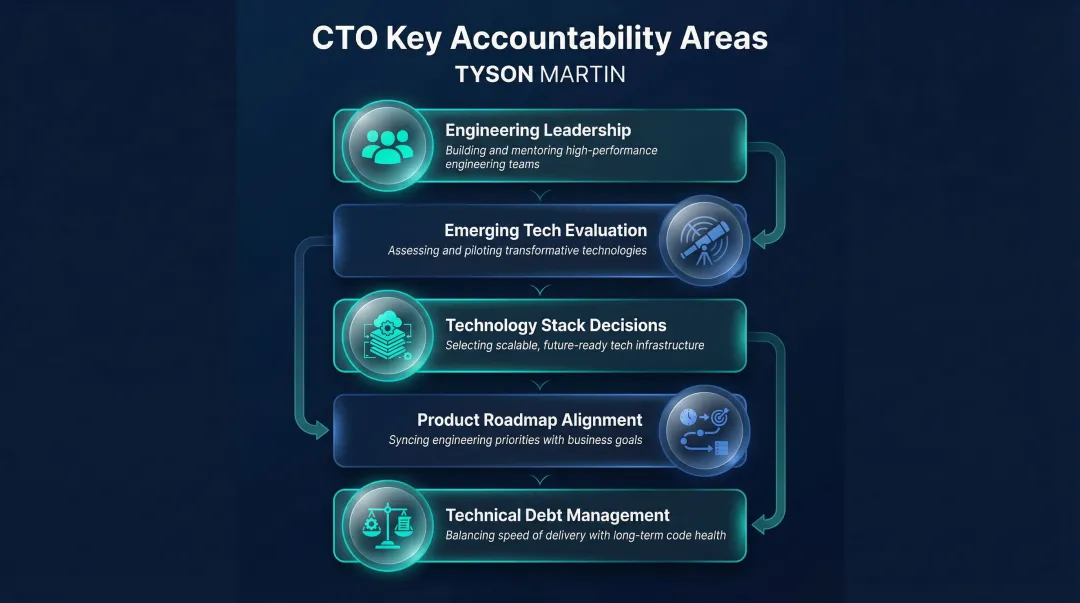
Core Responsibilities
The CTO tracks emerging technology trends and determines which ones to act on: cloud-native architecture, AI integration, edge computing. This role leads engineering and product teams, evaluates build-versus-buy decisions, and keeps the technology roadmap tied to market position and revenue growth.
Key accountabilities include:
- Directing product engineering teams and technical architecture
- Evaluating emerging technologies for commercial application
- Making strategic decisions about technology stack and infrastructure
- Ensuring product roadmaps align with market demands and revenue targets
- Managing technical debt while maintaining development velocity
What Boards Should Look For
Boards need a CTO who bridges long-range technical thinking with commercial outcomes. The right candidate explains technology strategy in business terms—specifically how product investments tie to revenue growth, market positioning, and customer retention. Ask candidates to walk through a past decision where they changed direction on a technology bet—how they recognized the shift, how they communicated it, and what it cost. That answer tells you more than any roadmap presentation.
What Is a CIO?
The CIO owns enterprise IT strategy — the systems, infrastructure, and governance that keep the business running. This role exists primarily in organizations that consume rather than build technology, using IT to deliver products and services internally and externally.
That scope is narrowing. 64% of organizations now allow technology spend to be managed by the business outside of IT, which means the modern CIO's value is less about controlling budgets and more about aligning technology decisions with business outcomes.
Core Responsibilities
Primary accountabilities:
- Managing enterprise IT operations and service delivery
- Leading digital transformation programs and technology modernization
- Overseeing vendor relationships, contracts, and SaaS portfolio management
- Ensuring data governance, analytics infrastructure, and business intelligence capabilities
- Maintaining systems uptime, disaster recovery, and business continuity
The data on CIO effectiveness is clear: 45% of CIOs now co-lead digital delivery with CxO peers, and when they adopt this shared-ownership model, 63% of digital initiatives meet or exceed outcome targets — compared to only 43% under traditional operator models.
What Boards Should Look For
Boards need a CIO who measures success in operational metrics: cost efficiency, systems uptime, on-time IT project delivery. The best CIOs directly connect technology investment decisions to business outcomes rather than infrastructure alone. The right question to ask: can this person explain a $5M IT investment in terms a CFO finds credible?
What Is a CISO?
The CISO is the custodian of organizational cybersecurity: responsible for protecting data, systems, and networks against threats ranging from cybercrime and insider risk to regulatory violations and third-party exposure. Cyber risk is now universally treated as business risk at the board level, elevating this role beyond a technical function into core governance.
Core Responsibilities
Primary accountabilities include:
- Developing and maintaining a cybersecurity strategy aligned with business risk tolerance
- Conducting ongoing risk assessments, penetration testing, and vulnerability management
- Managing incident response protocols and crisis communication
- Overseeing security awareness programs and employee training
- Ensuring compliance with applicable frameworks and regulations—NIST, ISO 27001, GDPR, HIPAA, PCI-DSS
- Coordinating third-party risk management and vendor security oversight
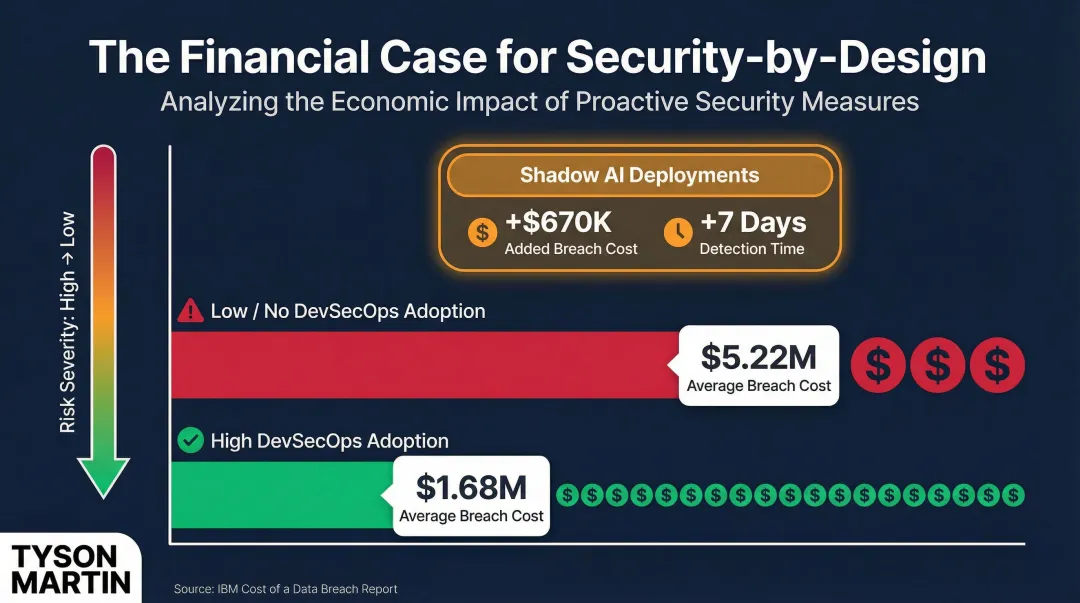
Organizations with high DevSecOps adoption save an average of $1.68 million per data breach compared to those with low or no adoption—proving that the CISO's influence on secure development practices delivers measurable financial impact.
The Reporting Line Debate
The CISO reporting structure is shifting rapidly away from IT and toward the CEO to reflect enterprise-wide strategic priorities:
| Reporting Line | 2023 | 2024 | 2025 |
|---|---|---|---|
| Direct to CEO | 5% | 14% | 42% |
| CIO/CTO/Tech Executive | 54% | 48% | 30% |
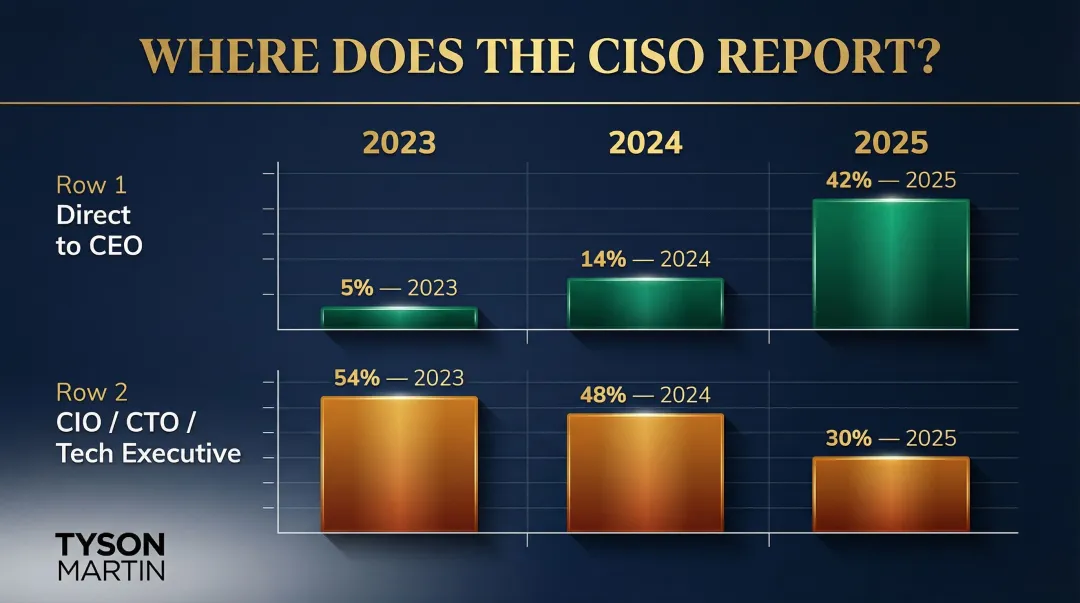
Where the CISO sits determines what they can say and to whom. The National Association of Corporate Directors notes that reporting to the CIO can create a conflict of interest between IT service delivery pressures, cost, customer experience, and security—making independent oversight harder to sustain.
The Board-CISO Relationship
99% of highly resilient organizations report board involvement in cybersecurity, with 48% of board members actively engaged with the security function. That engagement only works when the CISO communicates in terms the board can act on:
- Plain-English risk posture updates that show what changed and why it matters
- Trend-based dashboards—not one-off technical snapshots
- Clear escalation thresholds before and during an incident
Boards should be able to interrogate the CISO on material risk without needing a translator. That means understanding the business impact of vulnerabilities, the organization's detection and response capabilities, and readiness to meet regulatory disclosure obligations—including the SEC's requirement to report material cybersecurity incidents within four business days of determining materiality.
What Separates a Strategic CISO from a Purely Technical One
A strategic CISO does more than prevent threats. They translate risk posture into business impact, advise executives on decision rights and accountability, and speak credibly to regulators, auditors, and the board when incidents occur—not just after them.
The measure isn't how loudly they communicate risk. It's whether leadership can make decisions faster and operations hold steadier because of what the CISO made visible.
How CTO, CIO, and CISO Work Together—And When They Don't
The Innovation-Stability-Security Triangle
The CTO pushes capability forward, the CIO ensures operational infrastructure can absorb and scale it, and the CISO keeps it defensible. When all three are aligned and communicating, organizations can move fast without creating unacceptable or unacknowledged risk. When they're not aligned, the cracks show quickly.
CTO + CIO Collaboration in Practice
When the CTO identifies a new AI or cloud-native capability, the CIO must evaluate whether existing infrastructure, staffing, and budget can support it. Misalignment here leads to technical debt, integration failures, or shadow IT deployments that bypass governance controls entirely. The macroeconomic cost of poor software quality in the United States reached $2.41 trillion annually—much of it traceable to disconnected product and infrastructure planning.
CIO + CISO Collaboration in Practice
Digital transformation and cloud migration are the most common friction points. The CIO accelerates change while the CISO must ensure new environments aren't introduced with open vulnerabilities or poorly scoped access controls.
The data makes this tension concrete:
- Misconfiguration accounted for 21% of error-related breaches
- Through 2025, 99% of cloud security failures will be the customer's fault, primarily due to misconfigurations
- Breaches involving data stored across multiple environments (public cloud, private cloud, on-premises) cost an average of $5.05 million and took 276 days to identify and contain
CTO + CISO Collaboration in Practice
Security-by-design versus security-as-afterthought is where collaboration matters most. When the CTO builds customer-facing platforms without CISO involvement from the outset, retrofitting security controls post-launch is significantly more costly and creates window-of-exposure risk.
The cost differential is measurable:
- High DevSecOps adoption saved $1.68 million per breach versus $5.22 million for organizations with low or no adoption
- Security system complexity adds $830,000 to the average cost of a data breach
- Unsanctioned "Shadow AI" deployments added $670,000 to breach costs and extended detection and containment time by approximately one week
Warning Signs for Boards
Boards should recognize symptoms that indicate these three roles aren't effectively aligned:
- No shared risk register across technology and security
- CISO excluded from product development decisions
- Conflicting or inconsistent board reports from the same technology initiative
- Unclear escalation paths during incidents
- No joint accountability metrics across technology leaders
- Untested escalation protocols
Org chart proximity isn't alignment. The right question is whether these leaders have faced a real incident together—and whether the outcome was coordinated or chaotic.
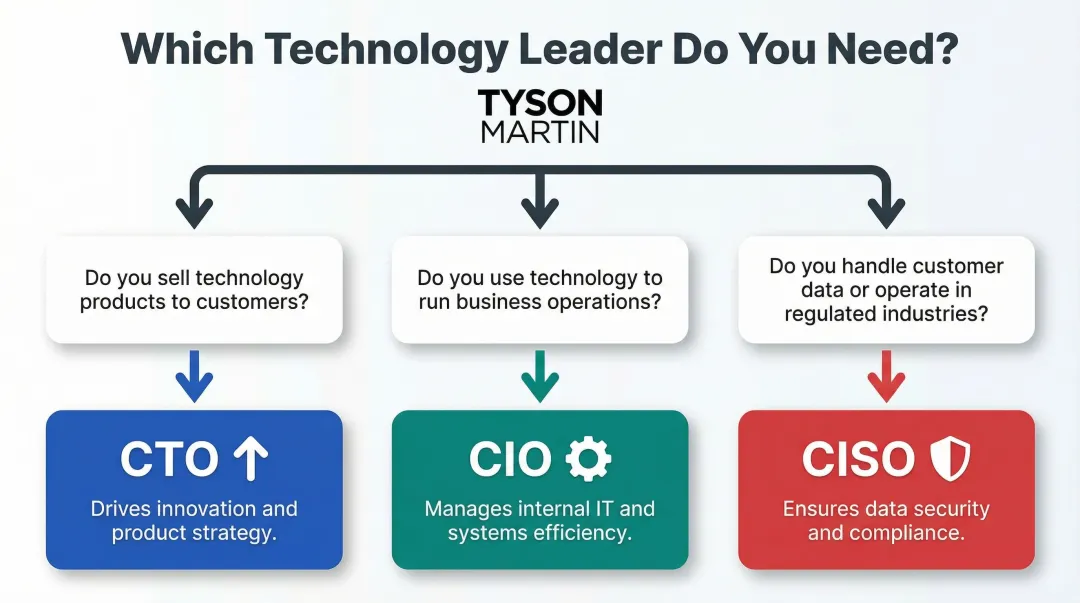
Which Technology Leader Does Your Organization Actually Need?
Technology Consumer vs. Technology Creator Diagnostic
Organizations that primarily use technology to deliver their product or service need a CIO. Organizations that build and sell technology products need a CTO. Many organizations need both, but at different budget and seniority levels depending on their stage, complexity, and transformation agenda.
Quick diagnostic framework:
- Do you sell technology products to customers? → CTO priority
- Do you use technology to run your business operations? → CIO priority
- Do you handle customer data, operate in regulated industries, or face cyber threats? → CISO mandatory
Every Organization at Meaningful Scale Needs a CISO
Dedicated cybersecurity leadership is no longer optional regardless of company type—especially in regulated industries, organizations handling customer data at scale, and those undergoing M&A activity or accelerated digital transformation.
The cost of not having dedicated security leadership is measurable:
- 45% of companies do not employ a CISO, with over 60% of those respondents from mid-sized organizations (100–5,000 employees)
- Appointing a CISO reduces the average cost of a data breach by $113,840
- Organizations with high security skills shortages experienced breach costs of $5.22 million, compared to $3.65 million for those with adequate staffing
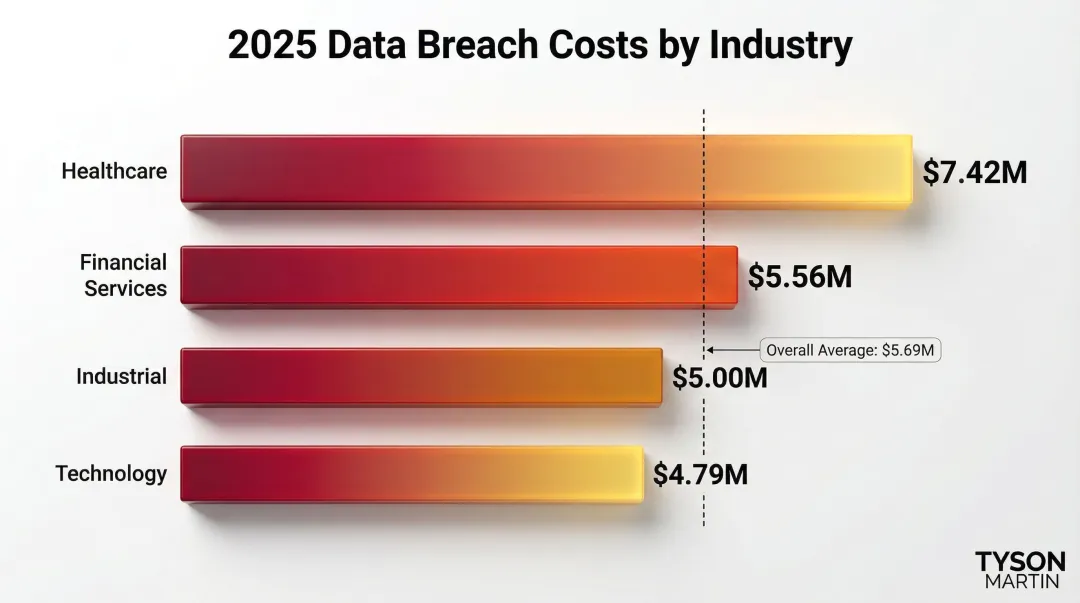
Regulated industries face particularly elevated breach costs, underscoring the need for dedicated security oversight:
| Industry | 2025 Average Breach Cost |
|---|---|
| Healthcare | $7.42 Million |
| Financial Services | $5.56 Million |
| Industrial | $5.00 Million |
| Technology | $4.79 Million |
The Fractional and Interim Option for Organizations in Transition
When a leadership gap exists—new CEO or board, post-incident recovery, M&A integration, or a digital transformation program without a clear security owner—a fractional or interim CISO or CIO can provide immediate governance structure, credible reporting, and executable priorities without the 6-to-12-month full-time hiring cycle.
For organizations that need stability fast, this model delivers clear decision rights, measurable 90-day outcomes, and board-ready communication from the start.
Tyson Martin works with boards and executive teams navigating exactly these transitions. His background spans enterprise security and technology leadership at AWS, Home Depot, and Best Buy, and he contributes actively to the National Retail Federation CISO Executive Committee and the World Economic Forum's Centre for Cybersecurity.
Decision Checklist for Boards and Executives
Use these questions to surface gaps before an incident or audit forces the issue:
- Are we a technology creator or consumer—and do we have the right leadership structure for that model?
- Do we have accountable leadership across IT operations, innovation, and cybersecurity?
- Does our CISO have a direct line to the board, independent from IT operations management?
- Are our technology leaders operating with shared escalation thresholds and a unified risk posture?
- Have we tested our incident response protocols with all three roles participating?
- Can each leader explain how their function contributes to measurable business outcomes?
Frequently Asked Questions
Can one person serve as both CIO and CISO?
Possible in small organizations, but most governance frameworks discourage it as the business grows. ISO/IEC 27001:2022 requires separation of conflicting duties, and the FFIEC IT Examination Handbook specifies the CISO should report to senior management or the board, not to IT operations leadership.
Does every company need all three roles—CTO, CIO, and CISO?
Not necessarily as full-time hires, but every organization needs accountable leadership covering innovation, IT operations, and cybersecurity. That coverage can come through full-time executives, fractional appointments, or distributed ownership. No function should go unowned.
Who does the CISO typically report to?
While CISOs historically reported to the CIO, the trend is toward direct or dotted-line reporting to the CEO, General Counsel, or the board's audit or risk committee. By 2025, 42% of CISOs report directly to the CEO, driven by regulatory pressure and the recognition that security accountability must be independent from the IT function it partly oversees.
What is the difference between a CTO and a CIO?
The CTO focuses on outward-facing technology—product innovation, engineering, and customer-facing capabilities that drive revenue and competitive differentiation. The CIO focuses on inward-facing technology—enterprise systems, operational efficiency, and IT strategy aligned to business operations and cost management.
Which role is most critical for board-level cybersecurity oversight?
The CISO carries primary accountability, but the structure matters as much as the title. Boards must ensure the CISO reports directly to them on material risk, regulatory exposure, and active incidents, not through the CIO or CTO. Independent access preserves unfiltered risk reporting.
When should a company consider a fractional CISO or CIO instead of a full-time hire?
Fractional and interim executives fit well in leadership transitions, post-incident stabilization, and M&A integration. They deliver credible oversight, clear decision rights, and measurable outcomes within 90 days, making them the right choice when boards need stability before committing to a permanent hire.