
Introduction
Boards and executive teams are increasingly held accountable for cyber risk — not just IT departments. The SEC's 2023 disclosure rules (Release No. 33-11216) now require public companies to describe their board's oversight of cybersecurity threats, identify responsible committees, and disclose how management assesses and manages cyber risk.
Directors can no longer delegate oversight to technical teams and assume they've fulfilled their duties. The real question is whether having a dedicated advisor in the room produces different outcomes.
Here's the tension: advisory services are a line-item expense. When nothing goes wrong, it's easy to question the value. But the cost of not having clear oversight only becomes visible when something does go wrong — during an incident, a regulatory review, or a leadership transition when accountability structures are tested under real conditions.
This article examines the concrete, operational advantages that cybersecurity advisory services deliver — specific outcomes boards and executives can track, not abstract assurances.
TL;DR
- Cybersecurity advisory services give boards and executive teams strategic oversight to make better, defensible risk decisions — not technical IT work
- The payoff comes through governance clarity, access to senior-level expertise, and proactive risk reduction that keeps pace with the business
- Organizations without advisory oversight operate reactively: costs escalate, compliance gaps widen, and accountability breaks down when incidents hit
- Strong advisory engagements produce inspectable results: stable risk dashboards, clear escalation thresholds, and executable 90-day priorities
- ROI shows up in board confidence, regulatory defensibility, and faster decisions — not just breach avoidance
What Are Cybersecurity Advisory Services?
Cybersecurity advisory services are strategic guidance that helps leadership teams understand, govern, and act on technology and cyber risk. This is distinct from technical security operations or managed IT services. An advisory engagement doesn't configure firewalls or manage helpdesks — it operates at the board and executive level, translating complex risk into clear decisions.
Where Advisory Fits in the Organization
Advisory sits above operational execution. While internal security teams handle vulnerability remediation, incident response implementation, and day-to-day tool management, advisory services establish the governance structures that connect those activities to executive decision-making.
EY's 2025 analysis of Fortune 100 companies found that 96% disclosed at least one board-level committee charged with cybersecurity oversight, and 89% identified at least one management role — such as CISO or CIO — providing cybersecurity insights to the board.
That governance gap is exactly where advisory operates. Rather than producing reports no one acts on, effective advisory delivers:
- A ranked list of risks tied to business outcomes — not raw vulnerability counts
- Clear owners and timelines leadership can inspect and hold accountable
- Governance structures that hold up under regulatory scrutiny or during a real incident
- Fewer surprises between the CISO and the board when it matters most

Key Advantages of Cybersecurity Advisory Services
The advantages below are grounded in what organizations actually track: board confidence, incident response speed, compliance posture, cost of risk, and executive decision quality rather than theoretical security improvements.
Advantage 1: Governance Clarity That Enables Defensible Decisions
Advisory services establish clear decision rights : who is responsible for what, what gets escalated to the board versus managed by leadership, and how cyber risk gets reported in terms that drive action rather than confusion.
Advisory structures board reporting around a stable risk posture dashboard showing trend over time, not technical noise. It defines escalation thresholds and ensures security metrics reflect business risk, not just system health:
- Decision rights documented and tested
- A dashboard that shows trend over time rather than point-in-time snapshots
- Clear escalation pathways for material incidents
- Named owners for top risks
Boards facing regulatory scrutiny or post-incident reviews are evaluated on whether they had adequate oversight processes in place — not just whether a breach occurred. That's the difference between a defensible position and a liability exposure.
The NACD Director's Handbook on Cyber-Risk Oversight emphasizes that cyber risk is a strategic, enterprise-wide risk requiring financial quantification and organization-wide collaboration, not just an IT operational metric. The SEC has already charged companies for materially misleading disclosures: in 2024, the SEC charged Unisys, Avaya, Check Point, and Mimecast for downplaying the extent of material breaches related to the SolarWinds compromise.
KPIs Impacted:
- Board confidence in cyber reporting
- Time-to-decision on cyber risk investments
- Clarity of escalation pathways
- Reduction in "surprise" incidents that weren't flagged upward in time
When This Advantage Matters Most:
Governance clarity is most critical during periods of organizational transition : new leadership, M&A activity, regulatory change, any period when accountability structures are undefined or untested under real conditions.
Advantage 2: Senior-Level Expertise Without the Full-Time Cost
Fractional and interim advisory arrangements give organizations access to CISO-level thinking and board-ready communication on a flexible basis without the overhead of a full-time executive hire.
A fractional advisor steps in quickly, brings structured frameworks from cross-industry experience, and delivers a 90-day plan with named owners and measurable outcomes. No months lost to a hiring and onboarding cycle.
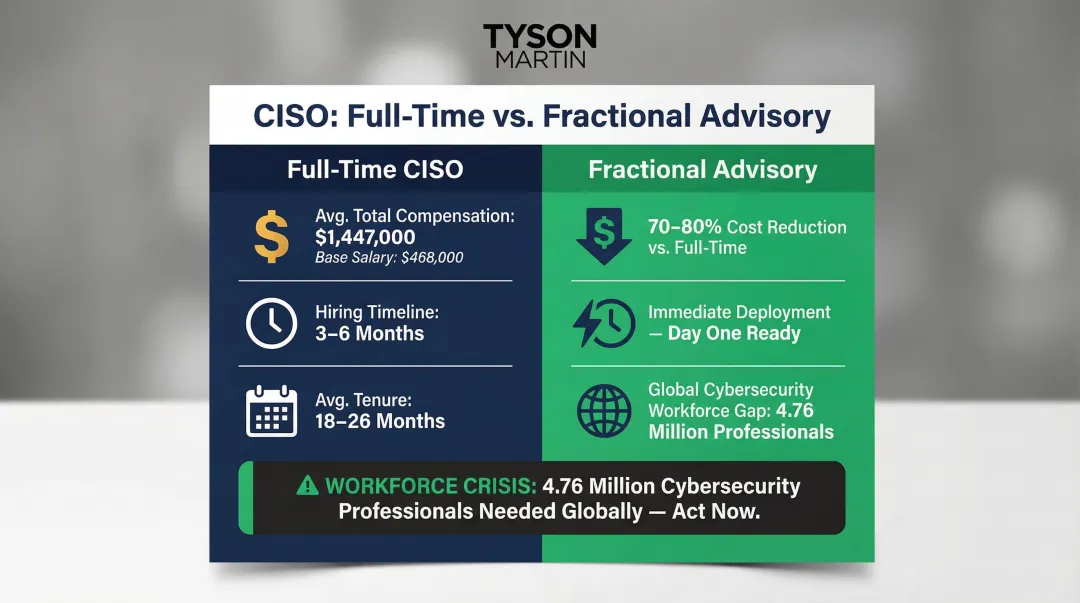
The cost gap is significant. Heidrick & Struggles' 2025 CISO compensation survey found average total CISO compensation (base + bonus + equity) at $1,447,000, with a cash base of $468,000.
For mid-market organizations or those in transition, fractional arrangements cost 70-80% less than a full-time hire while delivering senior expertise immediately. An experienced advisor with a replicable governance framework reaches operational clarity faster than an internal hire starting from scratch.
The Leadership Capacity Problem:
The ISC2 Cybersecurity Workforce Study estimates a global workforce gap of 4,762,963 professionals, a 19.1% increase from 2023. Industry estimates indicate average CISO tenure hovers between 18 and 26 months , significantly lower than the general C-suite average of 4.9 years. Organizations can't afford to wait six months to fill a vacancy when cyber risk doesn't pause for hiring cycles.
KPIs Impacted:
- Time-to-productive security leadership
- Cost of cyber risk oversight
- Speed of board reporting readiness
- Reduction in leadership vacuum during transitions
When This Advantage Matters Most:
This advantage is highest-impact when organizations are between CISOs, managing rapid growth, integrating an acquisition, or in a regulated industry where board-level cyber oversight is a compliance requirement.
Advantage 3: Proactive Risk Reduction Without Slowing the Business
Effective advisory doesn't create friction. It builds the governance structures, risk thresholds, and communication frameworks that let the business move fast with confidence, knowing that cyber risk decisions have clear ownership.
The output is a ranked list of risks tied to business outcomes, with owners and timelines that leadership can inspect. In practice:
- Risk-adjusted decision quality improves
- Security investment efficiency increases
- Mean time to detect and escalate decreases
- Reactive firefighting by the executive team drops
Organizations without this structure tend to over-invest in the wrong controls and under-invest in the ones that matter most, often because risk reporting isn't connected to business decisions. The WEF Global Cybersecurity Outlook 2024 found that 73% of leaders stressed the importance of cybersecurity fundamentals and addressing existing gaps, yet many organizations still struggle to prioritize effectively.
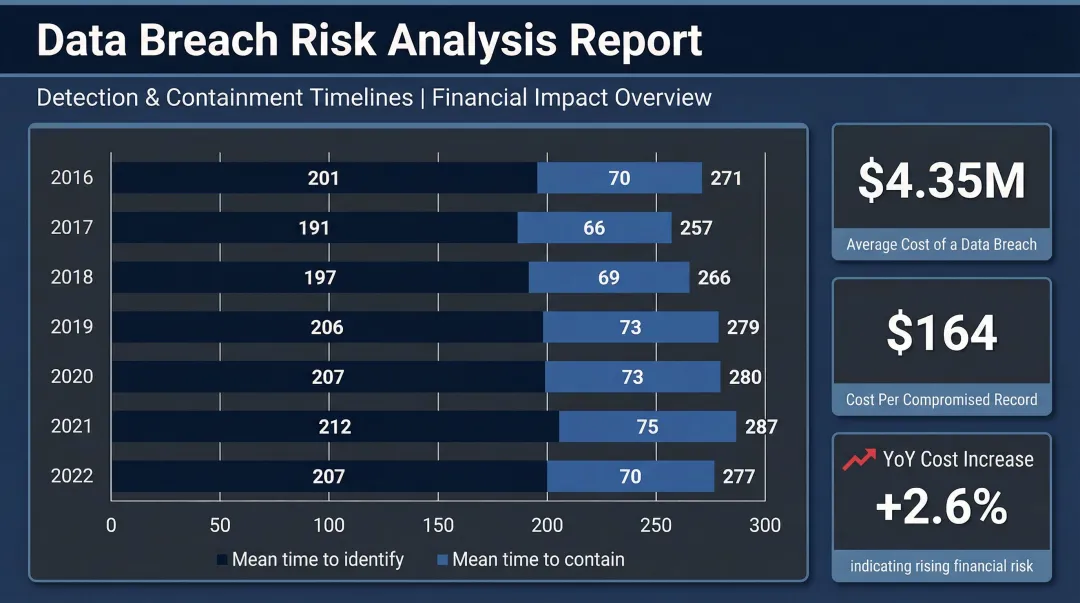
IBM's Cost of a Data Breach Report 2025 found the U.S. average breach cost reached a record high of $10.22 million, driven by regulatory fines and detection costs. The global average time to identify and contain a breach was 241 days, but organizations using AI and automation in security realized $1.9 million in cost savings compared to those that did not.
The goal of cyber advisory isn't to make the organization more cautious. When governance structures are clear and risk thresholds are defined, the business moves faster because cyber decisions stop being bottlenecks.
KPIs Impacted:
- Risk-adjusted decision quality
- Security investment efficiency
- Mean time to detect and escalate
- Reduction in reactive firefighting by the executive team
When This Advantage Matters Most:
This is most valuable in digital-native businesses, regulated industries, and enterprises managing complex technology environments where the cost of slowing down to manage security reactively is high.
What Happens When Cybersecurity Advisory Is Missing or Ignored
When board-level advisory oversight is absent, a pattern emerges: inconsistent risk reporting where the board receives either too little information or overwhelming technical detail, neither of which supports clear decisions.
Escalation and Accountability Failures:
- Incidents that were visible in the data for weeks before they reached leadership — because escalation thresholds weren't defined
- Compliance gaps discovered during audits rather than managed proactively, resulting in higher remediation costs and mandatory public disclosure
- Executive teams making reactive, expensive security investments after incidents rather than proactive, prioritized ones aligned to actual risk
The Equifax breach (2017) shows what these failures cost. A GAO audit (GAO-18-559) and House Oversight Committee report cited severe IT management and governance failures: siloed security and IT organizations, and over 300 expired security certificates — including 79 monitoring business-critical domains — that went undetected for 19 months.
The financial consequence was proportional. Equifax reported $221.5 million in breach-related costs through just the first nine months of 2018. Its annual security budget before the incident was $38 million.
Equifax isn't an outlier — it's a pattern. Incidents, audits, and leadership transitions all expose the same underlying gap: no one defined who was accountable, or when to escalate. Each quarter that passes without governance clarity raises the cost of reaching a defensible posture, and narrows the window to act before the next one arrives.
How to Get the Most Value from Cybersecurity Advisory Services
Advisory services deliver lasting value when treated as ongoing governance — not a one-time assessment. Boards and executives should expect consistent, inspectable outputs: a risk posture that's updated regularly, not just after incidents.
What "Working Well" Looks Like in Practice
- Clear decision rights documented and tested
- A dashboard that shows trend over time rather than point-in-time snapshots
- A 90-day plan that's reviewed and refreshed with named owners and measurable outcomes
This is the model applied in board advisory and fractional CISO engagements. Progress is visible, governance is testable, and the structure holds under real conditions. The first 90 days follow a defined sequence:
- Week One: Clear 30-day plan, fast risk triage, and board-ready communication
- Days 10-30: Risk posture baseline, top 10 risks identified, one-page plan delivered
- Days 31-90: Tabletop exercise testing incident response, finalized board packet with metrics and thresholds, budget and roadmap alignment tied to business goals

When to Engage — and How to Stay Current
Once that foundation is in place, timing determines how much value you get from it. Organizations that see the highest return engage advisors during proactive windows — before a crisis, before a leadership transition, or before a regulatory review — rather than as incident response.
Staying current requires two review rhythms: monthly reviews that track actions, costs, and blocked decisions; and quarterly reviews that assess whether the portfolio is actually getting simpler, safer, and easier to explain.
Conclusion
Cybersecurity advisory services are worth the investment when the measure is what organizations actually need from their cyber oversight: control, clarity, and the confidence to make defensible decisions — not just a security audit or a checklist.
Governance clarity, cost-effective senior expertise, and proactive risk management compound over time when advisory is treated as a standing governance practice rather than a reactive engagement. The cost of absence consistently exceeds the cost of the advisory itself.
A 2023 Deloitte survey found that 70% of respondents reported cyber was on their board's agenda on a regular basis (monthly or quarterly). Regularity alone doesn't equal effectiveness. What matters is whether that oversight translates into defensible decisions, faster escalation, and fewer surprises.
When organizations invest in advisory services that produce inspectable deliverables and sustainable governance, they reduce incident likelihood and cost while enabling the business to move faster with confidence.
Frequently Asked Questions
What is the difference between cybersecurity advisory services and a cybersecurity consulting firm?
Advisory services focus on governance, board-level oversight, and strategic decision-making — helping executives understand and act on risk. Consulting firms typically focus on technical implementation, security operations, or compliance projects. Different scopes, different audiences.
When does an organization need a fractional CISO instead of hiring a full-time one?
Common triggers include leadership transition, budget constraints, M&A activity, or the need for board-ready cyber governance quickly. A fractional arrangement delivers senior expertise without the full-time cost (which can exceed $1 million annually) or the 3-6 month hiring timeline.
How do cybersecurity advisory services help boards meet their oversight responsibilities?
Advisors translate risk into board-ready reporting, define escalation thresholds, and help establish governance structures that hold up to regulatory and legal scrutiny. SEC rules and NACD guidance now require boards to demonstrate active oversight, and advisory services provide the frameworks that satisfy those requirements.
What should an organization expect in the first 90 days of a cybersecurity advisory engagement?
Expect a risk posture baseline, prioritized recommendations with business context, and a 90-day plan with named owners. Deliverables should include a tabletop exercise testing incident response and a finalized board packet with metrics and escalation thresholds.
How do you measure the ROI of cybersecurity advisory services?
ROI covers breach avoidance (the average U.S. breach costs $10.22 million), reduced reactive security spend, compliance defensibility, and faster board decision-making. The return compounds with sustained advisory — not from a single engagement.
Is cybersecurity advisory worth it for organizations that already have an internal IT or security team?
Advisory and internal teams serve different functions. Internal teams handle execution — remediation, monitoring, tool management — while advisors provide board-level governance, independent perspective, and the structured reporting frameworks that connect security operations to executive decision-making. They complement each other, not duplicate effort.