Introduction
CISOs today face extraordinary pressure from every direction. Security teams are leaner than ever, attack surfaces are expanding faster than headcount, and boards are demanding clearer answers about cyber risk — all while the business expects to keep accelerating. Buying another tool or checking another compliance box won't fix it. This is a strategy problem first.
Many CISOs find themselves caught between reactive firefighting and aspirational roadmaps that never quite materialize. The underlying issue is often the absence of a coherent information security strategy that connects risk posture, governance, and execution to actual business objectives.
This article outlines a practical approach to strengthening information security strategy — covering risk clarity, governance, board communication, and execution metrics. Whether you're a sitting CISO or an executive evaluating your security program, what follows is a roadmap you can actually defend.
TLDR:
- Information security strategy connects risk posture, governance, and execution to business objectives — not a compliance checklist
- Start by identifying which assets and processes create serious harm if compromised — then apply risk appetite and threat modeling
- Align with the board through plain-English reporting that shows trend, not trivia
- Build governance with stable metrics, tested controls, and clear accountability across security, legal, and finance
- Prioritize high-leverage controls (MFA, patching, privileged access) that reduce the majority of attack paths
What Is an Information Security Strategy (And What It Isn't)
An information security strategy is the documented plan that identifies what an organization is protecting, from what threats, under what risk tolerance, with what resources — and how all of it maps to business objectives. A tool list or compliance checklist is not a strategy. A strategy answers a harder question: how does security enable the business to operate with confidence as threats evolve?
The Three Layers of a Mature Strategy
A mature information security strategy operates on three interconnected layers:
Risk Posture (What You Know):
- Inventory of critical assets, data, and business processes
- Understanding of threat landscape and attack vectors
- Documented risk appetite and tolerance thresholds
Governance (Who Decides What):
- Clear decision rights between board, executive leadership, and security teams
- Defined escalation thresholds and accountability structures
- Cross-functional ownership across security, legal, compliance, and operations
Execution (What Is Being Done and Inspected):
- Documented, tested, and owned controls
- Stable metrics that track trend over time
- Regular audits and assessments to verify controls work as designed
Many organizations have execution without governance, or governance without a clear risk posture. The result is reactive security spending, unclear accountability, and boards that can't oversee what they can't understand.

Why CISOs Are Revisiting Their Strategies Now
Those structural gaps are getting harder to ignore. Three external forces are pushing CISOs to close them now:
- Regulatory pressure: NIS2, SEC disclosure rules, and CIRCIA are raising the stakes for board-level accountability and incident transparency
- Generative AI: AI adoption is expanding the threat surface, introducing new data exposure risks and unfamiliar attack vectors
- Post-pandemic operational models: Remote work and cloud migration have pushed security perimeters outward, making traditional network-based defenses insufficient
The urgency is grounded in real risk. According to the 2025 Verizon Data Breach Investigations Report, vulnerability exploitation as an initial access vector surged to 20% of all breaches — a 34% increase from the previous year. That jump reflects what happens when organizations have controls but no clear framework for deciding which vulnerabilities get prioritized — and which get deferred until they become breaches.
Start with Risk Clarity: Know What You're Actually Protecting
Most security strategies fail not because of poor technology, but because they lack a clear, prioritized inventory of what matters most. Before building controls, a CISO must answer: What data, systems, and processes, if compromised, would cause serious business harm?
Build a Risk-Based Asset Inventory
A risk-based asset inventory goes beyond technical assets. It includes:
- Business-critical functions and processes
- Data flows (where sensitive data originates, travels, and resides)
- Third-party dependencies (vendors, cloud providers, SaaS platforms)
- Infrastructure that supports revenue-generating operations
When organizations conduct this exercise rigorously, they often discover a significant percentage of unknown or unmanaged assets. Shadow IT, orphaned cloud instances, and untracked vendor integrations create exposure that never appears on traditional asset lists.
Define Risk Appetite
The CISO's job is not to eliminate all risk but to ensure the organization's risk tolerance is explicit, documented, and reviewed by leadership. Undefined risk appetite leads to reactive security spending — overfunding low-impact areas while underfunding critical controls.
What effective risk appetite looks like:
- Documented thresholds for acceptable risk across asset categories
- Executive sign-off on risk trade-offs (e.g., speed vs. control)
- Clear criteria for escalating unacceptable risks to the board
- Regular review cycles tied to business changes
Apply Threat Modeling
Threat modeling separates strategy from a list of security controls. It maps likely adversaries, probable attack vectors, and realistic impact on the business.
Practical threat modeling includes:
- Identifying crown jewel assets (what attackers want most)
- Mapping attack paths adversaries would likely use
- Estimating business impact (financial, operational, reputational)
- Prioritizing controls based on actual threat scenarios, not theoretical vulnerabilities
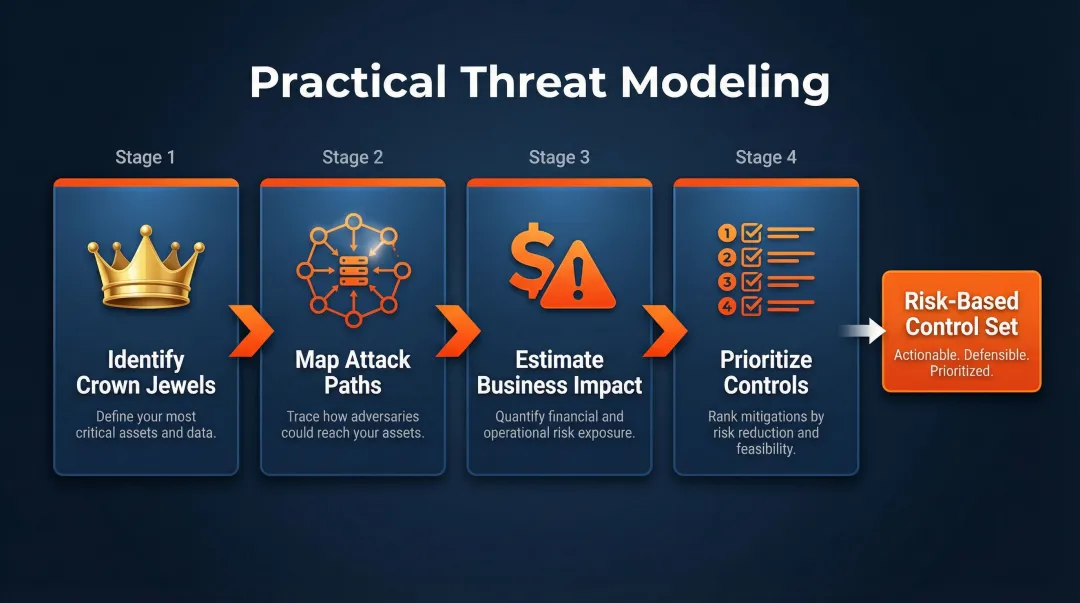
The output is a prioritized control set tied to real scenarios — not a compliance checklist or vendor-driven wish list. That prioritization also reveals a critical dependency: the asset picture must stay current for the model to hold.
Implement Continuous Attack Surface Monitoring
Cloud environments change daily. Third-party integrations appear without formal procurement review. Shadow IT accumulates faster than quarterly audits can capture it. Continuous attack surface monitoring keeps the asset picture accurate so threat models don't drift from reality. It ensures organizations can:
- Inventory assets in real time, including cloud instances and SaaS applications
- Detect new exposures as they emerge (open ports, misconfigured storage, unpatched services)
- Validate that security controls remain effective as the environment changes
Reactive metrics like mean time to respond (MTTR) have limited value without an accurate, current asset inventory. Risk clarity starts here — and everything built on top of it, from control selection to board reporting, depends on getting this foundation right.
Align Your Security Strategy with the Board and Business Objectives
CISO strategy often fails at the board level because CISOs report in technical terms that don't translate to business risk. Boards need to understand trend, not trivia — what changed, what it means, and what decision is needed.
What Effective Board Reporting Looks Like
Board-ready reporting includes:
- A plain-English risk posture summary showing where security stands against business objectives
- What shifted since the last briefing — threat landscape changes, control gaps, or new exposure
- Top open risks with active mitigation actions and what's still pending
- Decisions requiring board input: risk acceptance, budget allocation, or policy changes
Contrast this with dashboards that overwhelm with data but provide no actionable direction. Boards don't need to know how many vulnerabilities were scanned last month — they need to know if critical systems remain vulnerable to active exploits.
Establish Clear Governance Structures
Effective board communication requires governance structures that define:
- Decision rights: What the board decides vs. what management delegates
- Escalation thresholds: What triggers board notification vs. executive management handling
- Documented accountability: Who owns each risk, control, and decision
Without this clarity, CISOs manage upward without authority and downward without direction.
Build Cross-Functional Alignment
Those governance structures only hold when the right stakeholders are inside them. Security strategy should be co-owned with legal, compliance, finance, and operations — because regulatory requirements increasingly demand board-level accountability that no CISO can establish alone.
Cross-functional alignment ensures:
- Legal counsel reviews breach notification protocols
- Finance understands cyber insurance coverage and risk transfer strategies
- Compliance tracks regulatory obligations and audit timelines
- Operations integrates security into business continuity planning

Organizations navigating transitions — new leadership, mergers and acquisitions, or post-incident recovery — often need external expertise to establish governance quickly. This is where a fractional or interim CISO can step in: clarifying decision rights, building credible board reporting, and delivering a 90-day plan with named owners and measurable outcomes.
Build Governance That Holds Under Pressure: Controls, Metrics, and Accountability
Good governance means the security program can be inspected — not just described. Controls should be documented, tested, and owned. Policies should be enforced, not aspirational.
Establish a Stable Metrics Framework
A stable metrics framework uses a small number of indicators that show trend over time — not a rotating set of numbers that changes with each briefing.
Key metrics worth tracking:
- Crown jewel systems covered by MFA, EDR, and current patching (percentage)
- Mean time from initial compromise to containment
- Critical vulnerabilities patched within SLA (percentage on schedule)
- Phishing simulation results and training completion rates
- Critical vendors assessed and confirmed compliant (percentage)
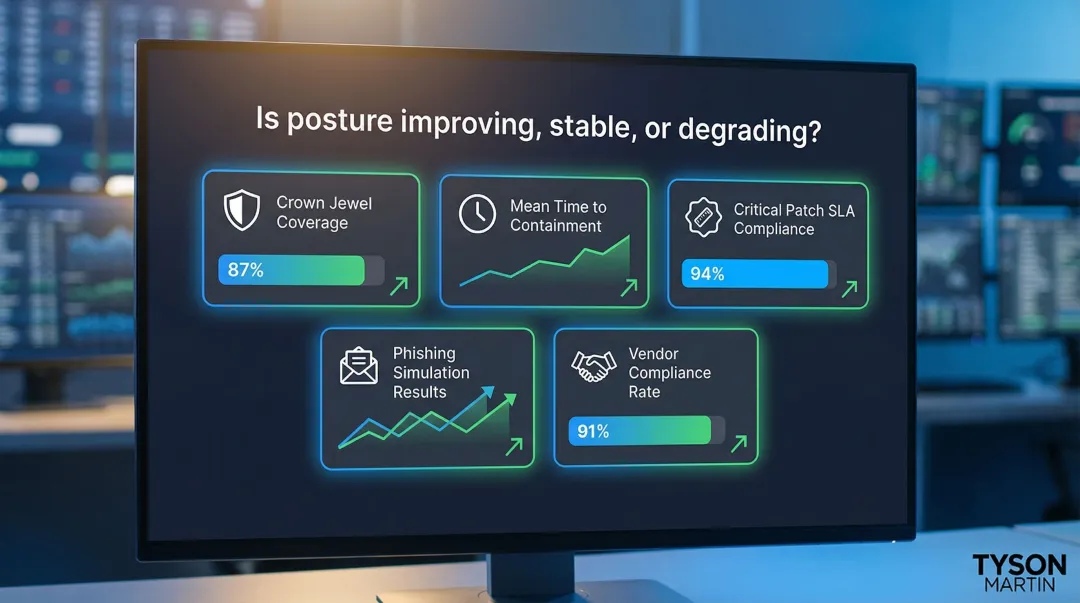
These metrics answer the board's core question: Is our security posture improving, stable, or degrading?
Conduct Regular Security Audits and Penetration Testing
Internal assessments confirm controls are working as designed. Third-party assessments surface blind spots that internal teams have normalized over time — treat both as recurring governance instruments, not annual compliance checkboxes.
Effective audit and testing programs include:
- Annual third-party penetration testing of critical systems
- Quarterly internal control audits with documented findings and remediation
- Regular tabletop exercises to test incident response plans
- Continuous validation of security configurations in cloud environments
Apply Zero Trust as a Governance Model
Zero Trust is a governance model as much as a technical architecture. Every access decision is treated as unverified until proven otherwise — which means clear ownership, enforced policies, and cross-team accountability. Implementing it requires:
- MFA on all accounts, least-privilege access, and regular access reviews
- Network micro-segmentation to limit lateral movement after a breach
- Context-aware access decisions that evaluate user, device, and location continuously
Zero Trust requires organizational discipline and cross-team ownership to maintain. Each control needs a named owner, a documented standard, and a review cycle — or it drifts.
Strengthen Security Culture and Incident Response Readiness
Human error remains one of the most common causes of security breaches. Microsoft's research shows that MFA blocks over 99% of unauthorized access attempts — most of those breaches trace back to preventable credential misuse. A security strategy is only as strong as the behaviors it produces.
Build Continuous Security Awareness
Security awareness training should be continuous, scenario-based, and measurable — not annual checkbox compliance.
Effective programs include:
- Monthly phishing simulations with personalized coaching
- Role-specific training (e.g., finance teams on payment fraud, developers on secure coding)
- Metrics tracking completion rates, simulation outcomes, and trend improvements
- Integration of security awareness into onboarding and performance reviews
Test Your Incident Response Plan
A tested incident response plan covers detection, containment, eradication, recovery, and post-incident review — each stage with named owners and clear communication protocols. Plans that have never been simulated will fail under real pressure. Essential elements include:
- Tabletop exercises simulating ransomware, data breach, and denial-of-service scenarios
- Clear escalation paths to legal counsel, executive leadership, and the board
- Pre-approved communication templates for internal, customer, and regulatory notifications
- Post-incident review processes that capture lessons learned and update controls
Address Legal and Regulatory Dimensions
Incident response is now also a legal and regulatory matter. CISOs should work with legal counsel on:
- Breach notification timelines (state laws, GDPR, SEC disclosure requirements)
- Indemnification agreements and cyber insurance coverage
- Accuracy of public statements about security posture to avoid personal liability
Inaccurate disclosures or delayed notifications can trigger regulatory penalties and shareholder lawsuits — and increasingly, personal liability for the CISO. Getting this right is as much a leadership obligation as a legal one.
Apply the 80/20 Rule to Prioritize Maximum Impact
A small number of controls account for the majority of defensive value. CISOs who try to do everything — driven by compliance checklists or vendor pressure — spread resources thin rather than hardening what matters most.
Identify High-Leverage Priorities
The CISA Known Exploited Vulnerabilities (KEV) catalog tracks 1,566 vulnerabilities explicitly known to be exploited in the wild as of April 2026. Prioritizing these vulnerabilities over generic CVSS scores delivers outsized risk reduction.
Foundational controls that consistently deliver value:
- Enforce MFA across all access points — it blocks over 99% of credential-based attacks and remains the single highest-ROI control available
- Patch from the CISA KEV catalog first, not every theoretical flaw flagged by CVSS scores
- Restrict privileged accounts and enforce just-in-time access to limit blast radius
- Run continuous, scenario-based phishing training — not annual checkbox exercises
- Test incident response plans with clear owners and communication protocols before an incident forces the issue

Use Risk Scoring to Tailor the 80/20 Approach
Not all organizations face the same threat profile. CISOs should use risk scoring and prioritization frameworks to align the 80/20 approach with their specific environment.
Factors to consider:
- Industry-specific threats, such as ransomware targeting healthcare or IP theft in manufacturing
- Adversary motivations, such as financial gain, espionage, or operational disruption
- Regulatory obligations including PCI DSS, HIPAA, and GDPR
- Business model vulnerabilities, such as e-commerce downtime or SaaS data exposure
The goal is deliberate concentration — directing budget and attention toward the threats most likely to materialize in your specific environment, not the longest list of theoretical risks.
Frequently Asked Questions
What is an information security strategy?
An information security strategy is the documented plan connecting an organization's risk posture, governance model, and security execution to its business objectives. It defines what you're protecting, from what threats, under what risk tolerance — and is distinct from a tools list or compliance program.
What is the 80/20 rule in cyber security?
The 80/20 rule (Pareto Principle) in cybersecurity suggests that roughly 20% of security controls address roughly 80% of risk. This encourages CISOs to prioritize high-impact, foundational controls like MFA, vulnerability patching, and privileged access management over comprehensive but diluted coverage.
How often should a CISO review and update their security strategy?
At minimum, conduct an annual formal review. Trigger ongoing adjustments for significant changes: major incidents, regulatory updates, business acquisitions, or material shifts in the threat landscape. Strategy must remain aligned with evolving business objectives and risk.
How should a CISO communicate cybersecurity risk to the board?
Use plain-English risk summaries and trend-based dashboards showing what changed, what decisions are needed, and what escalations require board input — not technical metrics. Keep the focus on open risks, active responses, and the specific decisions you need from leadership. Skip operational detail that belongs with management, not the board.
What metrics should a CISO track to measure security strategy effectiveness?
Track trend-based categories: asset coverage across critical systems, detection and containment times, high-risk finding remediation rates, phishing simulation results, and third-party risk assessment completions. Point-in-time counts tell you where you stand; trend data tells you whether your strategy is working.