Introduction
Boards are now legally and reputationally accountable for cyber risk—not just IT departments. The SEC's cybersecurity disclosure rules, effective since December 2023, require public companies to report material cyber incidents within four business days and disclose board-level oversight practices annually. High-profile breaches like MGM's estimated $100 million impact and Clorox's $24 million in incremental expenses demonstrate what's at stake when governance fails.
Yet most boards want to provide meaningful oversight but lack a clear framework for what "good" looks like. This guide gives board members, CEOs, General Counsel, and risk leaders a practical strategy for governing cybersecurity without drowning in technical noise.
TLDR:
- Boards face legal liability under SEC rules: four-day incident reporting and annual oversight disclosure
- 88% of S&P 500 boards lack cybersecurity expertise, creating dangerous blind spots in risk assessment
- Effective oversight means stable metrics, clear escalation thresholds, and decision rights set before incidents hit
- M&A, leadership transitions, and active breaches each demand immediate, independent cyber clarity
- The right advisor translates technical risk into business decisions without creating adversarial dynamics
Why Cyber Risk Is Now a Board Governance Responsibility
Cybersecurity has evolved from an IT problem to a business and governance imperative. Incidents now trigger financial losses, regulatory scrutiny, reputational damage, and director liability. Cybersecurity Ventures projects global cybercrime costs will reach $10.5 trillion annually by 2025. At that scale, cyber risk belongs on the same agenda as financial and legal exposure.
Regulatory Pressure Has Accelerated Board Accountability
The SEC's final rules on cybersecurity risk management, adopted July 26, 2023, fundamentally changed board responsibilities:
- Form 8-K (Item 1.05): Public companies must disclose material cybersecurity incidents within four business days of determining materiality
- Form 10-K (Regulation S-K Item 106): Annual disclosure of the board's oversight of cyber threats and management's role in risk assessment is mandatory
These aren't suggestions—they're legal requirements backed by enforcement authority.
Growth Decisions Introduce Cyber Risk That Boards Must Evaluate First
Strategic decisions around M&A, cloud migration, remote work expansion, and AI adoption introduce new cyber risks that boards must evaluate before committing capital, not after. A 2022 study found 62% of organizations face significant cybersecurity risks when acquiring companies, and 53% discovered unaccounted-for devices after integration.
Boards that treat cyber as separate from strategy absorb risk they never agreed to take on. Governing it requires the same discipline applied to financial, legal, and operational decisions—not a delegation to technical teams and a quarterly status update.
The Board-CISO Communication Gap and Why It Creates Blind Spots
A fundamental tension exists: CISOs operate in technical language and operational urgency; boards think in business risk, financial exposure, and strategic trade-offs. Without a bridge, boards receive either raw technical data they can't act on or sanitized summaries that hide real risk.
The Expertise Deficit Is Staggering
The 2023 NightDragon and Diligent Institute study revealed that 88% of S&P 500 boards lack a director with specialized cybersecurity experience, and only 1.4% have a current or former CISO. Meanwhile, a 2025 Gartner survey found 90% of non-executive directors lack confidence in cybersecurity value, yet 84% of CISOs believe they're aligned with their boards.
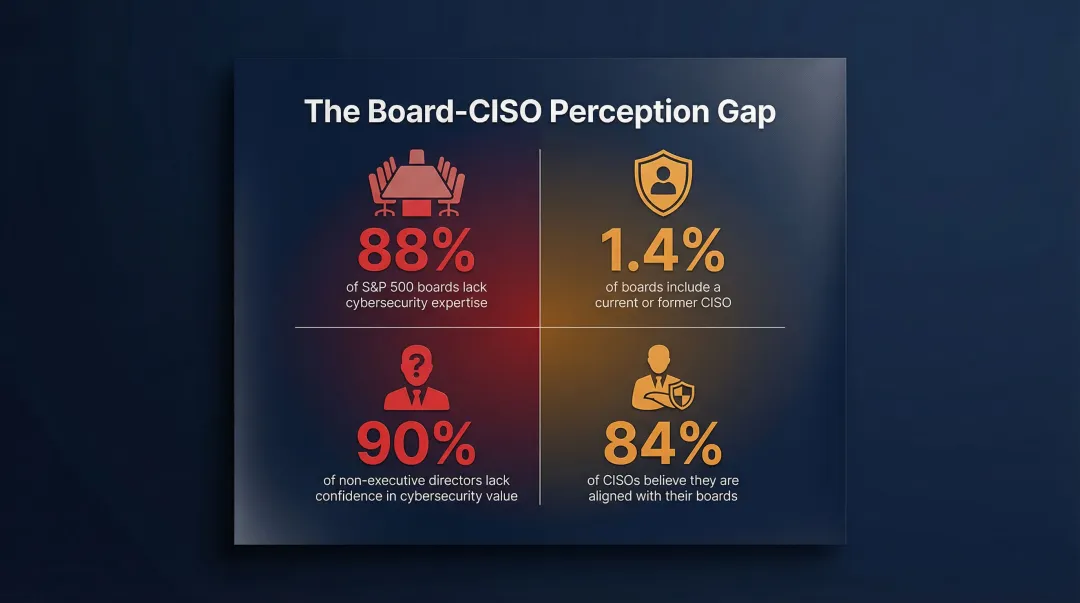
This perception gap is dangerous. Boards think they understand, CISOs think they're communicating clearly, yet neither can articulate what the organization is actually funding or where residual risk remains. Closing that gap starts with changing what boards actually ask for in security briefings.
What Boards Actually Need From Security Briefings
Effective board reporting isn't about volume—it's about clarity. Boards need:
- Current risk posture in plain English: Not "we patched 847 vulnerabilities," but "our exposure to ransomware decreased because we eliminated privileged access gaps in financial systems"
- Trend direction since the last briefing: Is risk moving up or down — and why?
- Clear flags on decisions requiring board input: Which risks need board approval to accept?
The Discipline of "Inspect What You Expect"
Boards that only receive presentations from management cannot verify accuracy or identify omissions. Effective governance includes independent channels for validating what management reports—not distrust, but discipline.
This doesn't mean every board member becomes a cybersecurity expert. It means having access to someone who can translate across both worlds and hold management accountable for meaningful reporting — evidence-based validation rather than trust-based acceptance.
What Effective Board-Level Cybersecurity Oversight Looks Like
Assign Oversight Responsibility Explicitly
A 2024 Deloitte/CAQ survey found 58% of audit committees hold primary oversight for cybersecurity risk, compared to 25% relying on the full board and 9% using dedicated risk committees. The structure matters less than clarity: oversight responsibility must be explicitly assigned and documented in board charters.
Dedicated tech/cyber committees improve oversight depth compared to folding it under audit, which already carries heavy compliance workloads. Either structure can work—what fails is ambiguity about who owns the responsibility.
Build a Stable Dashboard, Not Noise-Filled Briefings
Boards need trend data—risk posture over time, incident velocity, remediation progress—not point-in-time trivia. Recommended approach:
- Select 3-5 stable metrics reviewed consistently every meeting
- Track whether risk is moving up or down quarter over quarter
- Use ranges and plain targets (e.g., "above 95% for critical patch compliance") instead of false precision
- Ensure every metric can drive a decision—if it can't, it doesn't belong in the packet
A well-scoped dashboard like this typically stabilizes within two to three board cycles once owners and thresholds are defined.
Define Decision Rights and Escalation Thresholds in Advance
Boards should define which decisions require board involvement versus management delegation, including:
- What makes a cyber incident "material" for disclosure purposes
- Who makes the materiality call and under what timeline
- Which risk acceptance decisions escalate to the board versus stay with management
- Clear severity levels with documented approval authority
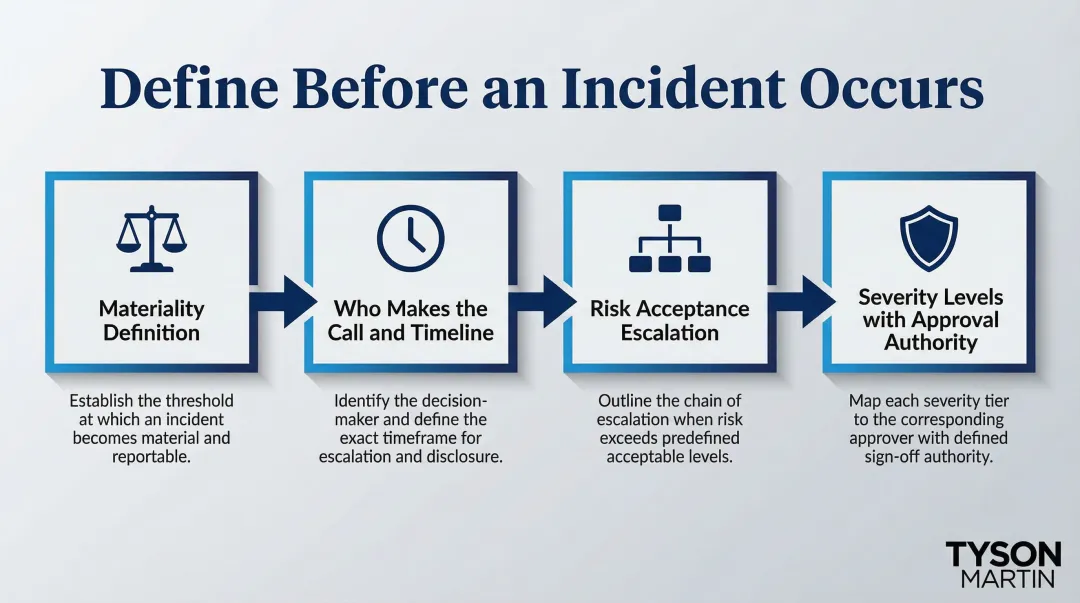
These aren't theoretical exercises—they must be tested through tabletop scenarios before a real incident occurs.
Demand 90-Day Executable Plans With Named Owners
Moving from presentations that disappear after the meeting to plans the board can inspect requires:
- Named owners for each initiative with clear accountability
- Defined milestones with completion dates
- Measurable outcomes the board can validate (e.g., "MFA coverage for privileged accounts reaches 100%" not "improve access security")
The standard is a clear definition of "done"—something teams can prove and boards can inspect, not a status update that resets next quarter.
Validate Incident Preparedness, Don't Assume It
Boards should confirm:
- Tabletop exercises have occurred with documented lessons learned
- Response plans are accessible during an outage, not just stored on systems that go down
- Communication responsibilities are assigned before a breach happens
- Backup restoration has been tested for at least one critical system
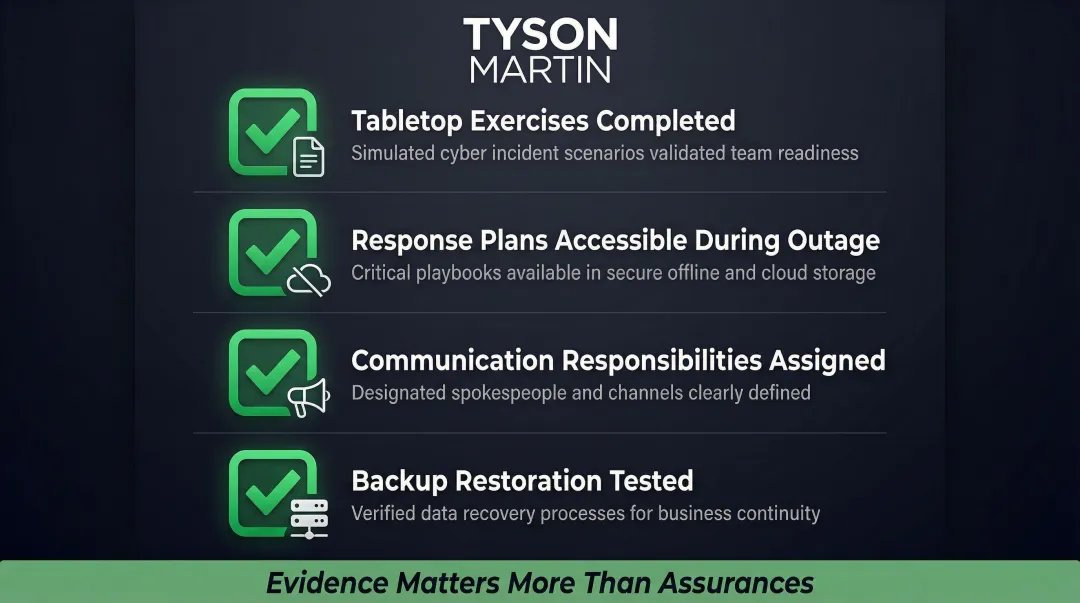
Evidence matters more than assurances.
The Questions Every Board Should Be Asking
Effective oversight starts with asking business questions, not technical ones. The NACD's 2023 Director's Handbook on Cyber-Risk Oversight and the World Economic Forum's Principles for Board Governance of Cyber Risk offer the most widely adopted frameworks for structuring that inquiry.
Strategy and Alignment
- Does our cybersecurity program align with our business model, growth plans, and risk tolerance?
- Are security investments prioritized by business impact or technical preference?
- How does our security roadmap support our digital transformation initiatives?
- What trade-offs are we making between speed to market and security controls?
Risk Visibility
- Do we have a complete view of our attack surface, including third-party vendors, cloud environments, and AI tools?
- What risks has management accepted, and have those been explicitly documented?
- Which vendors have access to our most sensitive data, and how do we validate their security posture?
- What happens if our largest technology partner experiences a breach?
Incident Readiness
- When was our last tabletop exercise, and were board representatives involved?
- If a breach occurred tonight, who makes the first call—and who makes the call about public disclosure?
- Can we restore critical systems from backup within our acceptable downtime window?
- Do we have legal counsel and forensics vendors on retainer with clear engagement protocols?
Metrics and Accountability
- Are the metrics we receive showing trends over time or just snapshots?
- How do we know if our investments are reducing risk exposure, not just generating activity?
- Who owns each metric, and what decision does it drive?
- What changed since our last meeting—better or worse?
The most effective boards build these questions into the quarterly briefing agenda — not as a one-time review, but as a standing structure that management prepares for. When leadership knows these questions are coming, the quality of what they bring to the table improves.
High-Risk Moments When Boards Need Immediate Cyber Clarity
The Transition Scenarios Where Governance Gaps Become Most Dangerous
Four scenarios concentrate governance risk the most:
- Mergers and Acquisitions: Cyber due diligence gets compressed under deal pressure. Marriott's 2016 Starwood acquisition inherited a breach that had been running since 2014 — a direct consequence of inadequate review.
- Leadership Transitions: When a CISO, CIO, or CEO departs, the security baseline becomes uncertain. 41% of companies lack CISO succession plans, leaving real gaps during the handoff period.
- Active Incidents: Without pre-defined escalation processes, organizations make expensive decisions under pressure. Speed and clarity matter most exactly when they're hardest to achieve.
- Technology Modernization: Cloud migration and AI adoption bring unfamiliar risk profiles. The WEF's 2025 Global Cybersecurity Outlook reports 66% of organizations expect AI to significantly impact cybersecurity. Only 37% have processes to assess AI tool security before deployment.

When Boards Cannot Afford to Wait
In these moments, boards cannot wait six months for an executive search or hand the problem to internal teams already managing active priorities. An experienced, independent perspective needs to be operational within days: a fractional CISO, interim executive, or board advisor who can walk in and start reducing uncertainty immediately.
In practice, that means four things:
- Clarified decision rights preventing both silence and overreaction
- A credible risk posture baseline boards can articulate to regulators
- An escalation process that works under pressure with named roles
- Communication the board can defend to stakeholders
Tyson Martin works with organizations in exactly these moments—stepping in as an interim or fractional CISO, CIO, or board advisor when continuity cannot wait. Within the first 30 days, he establishes clear severity levels and defines what gets locked down first and why. Boards receive daily executive updates with specific metrics covering speed, scope, containment, and impact.
How to Choose a Board-Level Cybersecurity Advisor
The Qualities That Actually Matter
Board-level cybersecurity advisors differ from technical consultants in one critical way — what they do with what they know:
- Understand governance and how boards actually operate
- Speak in business terms without defaulting to jargon
- Operate inside enterprise environments where politics and processes matter
- Work with boards—not just present to them, but challenge respectfully and hold management accountable
Certifications like CISSP matter less than the ability to translate risk into decisions.
The Value of Operating Experience
Someone who has led security transformation at scale — in enterprise environments, regulated industries, and high-stakes transitions — can pressure-test management's plans in ways pure consultants cannot. That kind of credibility comes from having actually owned the risk, not just advised on it. Boards should look for advisors who have operated at scale across multiple enterprise contexts, not just consulted around the edges.

Practical Evaluation Criteria
When selecting a board-level advisor, ask three questions:
- Do they know your regulatory context? An advisor should be fluent in the rules specific to your industry — SEC disclosure requirements, GDPR, HIPAA, or sector-specific frameworks — not just familiar with cybersecurity in general.
- Can they stay independent? The best advisors run reviews without getting captured by management's framing. They work constructively with internal teams while maintaining enough distance to surface what leadership may not want to hear.
- Do they have real-time intelligence? Advisors connected to peer networks and national bodies — such as NACD or the World Economic Forum's Centre for Cybersecurity — bring current threat patterns and governance benchmarks that no internal team can replicate on its own. For example, Tyson Martin's active roles with NACD, the NRF CISO Executive Committee, and the WEF Centre for Cybersecurity directly inform the board briefings and governance recommendations he brings to engagements.
Frequently Asked Questions
What does a board-level cybersecurity consultant actually do?
A board-level cybersecurity consultant helps boards understand, govern, and oversee cyber risk in business terms—not technical terms. They translate CISO reports, structure board reporting cadence, define escalation thresholds, and ensure the board can make defensible decisions that withstand regulatory scrutiny.
How often should boards receive cybersecurity briefings?
Most governance frameworks recommend cybersecurity be a standing agenda item at every board or committee meeting, with formal risk posture updates quarterly. 73% of audit committees discuss cybersecurity at least quarterly. The cadence should increase during major business transitions or elevated threat periods.
Does a board need a cybersecurity expert among its directors?
A director with cybersecurity experience is valuable, but the real need is board-wide access to independent cyber expertise—through an advisor, external reviewer, or designated committee. One expert director is not enough if the rest of the board cannot engage meaningfully with cyber risk.
What is the difference between a board advisor and a fractional CISO?
A board advisor supports governance and oversight—helping the board ask the right questions and interpret risk. A fractional CISO works inside management's structure to build and run the security program. Some advisors, like Tyson Martin, can serve in either or both roles depending on what the organization needs.
What questions should a board ask about its cybersecurity program?
The strongest questions address risk visibility, incident readiness, decision rights, and whether metrics show trends or just activity. The "Questions Every Board Should Be Asking" section of this guide covers each of these areas with a full framework.
How should boards handle cybersecurity oversight during a merger or acquisition?
Cyber due diligence should be embedded in M&A from the start—covering the target's security posture, technology debt, and third-party risk. An independent cyber review belongs in deal evaluation, not as a post-close discovery. PwC's cyber-in-deals framework covers governance, vulnerability management, and external threat research.
About Tyson Martin
Tyson Martin helps boards and executive teams reduce technology and cyber risk without slowing the business by clarifying decision rights, tightening governance, and building execution you can inspect. He serves as a board advisor or director candidate, and steps in as an interim or fractional CISO, CIO, or Chief Digital Officer when organizations need stability fast.
His background includes leading security and technology transformation at AWS, Home Depot, and Best Buy. He is an active contributor to the National Association of Corporate Directors, serves on the National Retail Federation CISO Executive Committee, contributes to the World Economic Forum's Centre for Cybersecurity, and served as ISC2 Richmond Board President.
Contact: tyson.martin@gmail.com | +1 (802) 430-9200 | LinkedIn