Introduction
Every software vendor has a moment when a promising enterprise deal stalls at the security review stage. A procurement team sends a 100-question questionnaire, or legal demands a SOC 2 Type 2 report before signing. Without that report, the deal slows by weeks—or dies entirely. 46% of companies report that lacking compliance certification has actively delayed their sales cycles.
SOC 2 appears in vendor contracts and RFPs constantly, but most software companies treat it as a checkbox rather than a structured security program with accountable leadership. The result: rushed implementations, bloated audit scopes, and qualified opinions that create more problems than they solve.
Getting SOC 2 right requires the same strategic oversight as any other enterprise risk program — and that's exactly what this guide addresses. You'll find a practical breakdown of how compliance works, what trips vendors up, and where a fractional CISO makes the difference between a clean report and a delayed deal.
TL;DR
- SOC 2 is an AICPA auditing standard that evaluates whether a software vendor's security controls meet Trust Services Criteria
- Enterprise and regulated customers increasingly require SOC 2 to approve vendors—77% cite it as a top procurement requirement
- Expect 6–12 months of work: scoping, control implementation, evidence collection, and a third-party audit
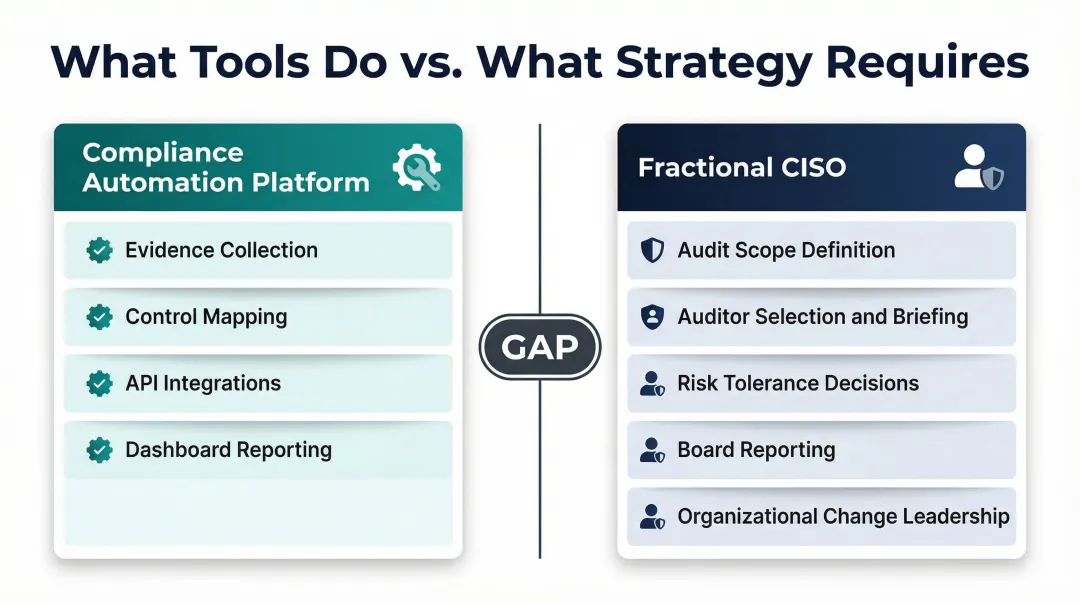
- Compliance platforms automate evidence collection—they don't replace the strategic decisions that determine whether the audit succeeds
- A fractional CISO provides the strategic leadership growth-stage vendors need without full-time executive cost
What Is SOC 2 Compliance?
SOC 2 is a voluntary auditing standard developed by the American Institute of Certified Public Accountants (AICPA) that evaluates whether a service organization's controls adequately protect customer data. The framework assesses five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
Security is mandatory for every SOC 2 audit. The remaining four are optional — selected based on what your customers actually require.
The practical outcome is a third-party attestation — issued by a licensed CPA firm — that tells enterprise customers a software vendor has security controls in place to be trusted with their data. This isn't a certification like ISO 27001; it's an audit report that documents control design and effectiveness.
SOC 2 Type 1 vs. Type 2:
- Type 1: Snapshot of control design at a single point in time — faster and cheaper to obtain, but limited in what it proves
- Type 2: Evaluates whether controls operated consistently over 6–12 months — the standard enterprise procurement teams expect
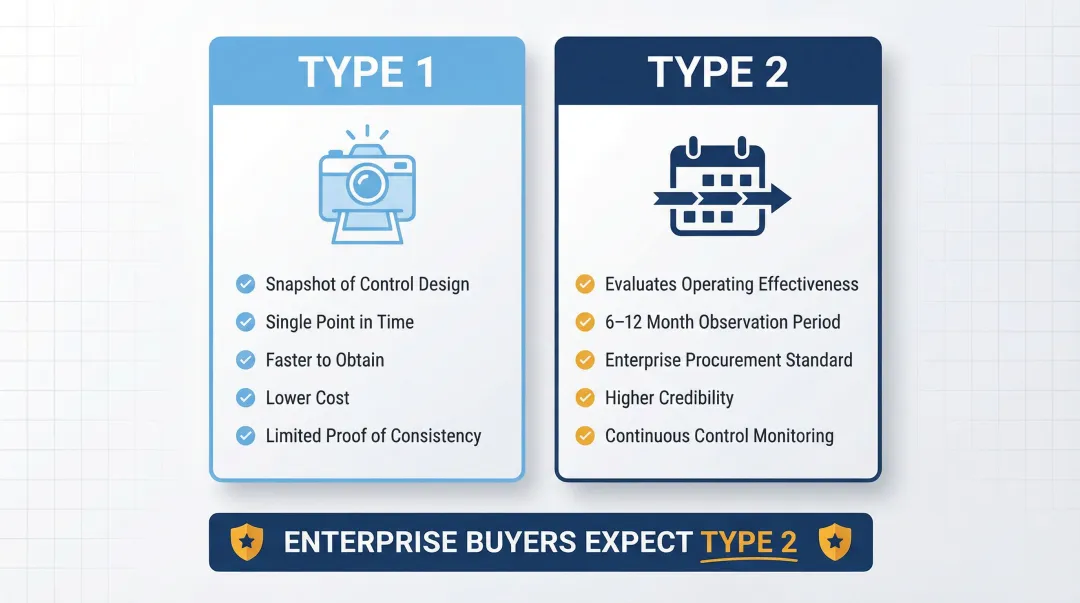
Enterprise buyers strongly prefer Type 2 reports because they prove controls operated consistently over time, not just on the day an auditor walked through.
SOC 2 vs. Other Standards:
- SOC 1 covers financial reporting controls, not security — a different audit for a different purpose
- ISO 27001 is an international certification with annual surveillance audits; rigorous, but less common in U.S. enterprise vendor reviews than SOC 2
Why Software Vendors Need SOC 2
Enterprise procurement teams and security reviewers consistently require SOC 2 Type 2 reports before approving new software vendors. 77% of organizations cite compliance with standards like SOC 2 as their top requirement for third-party vendors.
Deal-Stage Dynamics
SOC 2 is often raised during security review or legal contract negotiations, not at the start of a sales cycle. This timing creates deal risk: without a report, vendors face lengthy security questionnaires that delay closures by 4 to 8 weeks. Providing a SOC 2 report reduces questionnaire response time by 80% — a meaningful advantage at the contract finish line.
Regulated Industry Demands
Regulated industries pass their compliance burdens down to software vendors:
- Banks operating under OCC and Federal Reserve guidance are expected to review SOC reports when assessing third-party operational risk and internal controls
- Healthcare covered entities require SOC 2 alongside Business Associate Agreements as independent assurance of vendor security posture
- FedRAMP has proposed accepting SOC 2 Type II assessments as an approved external framework to meet Validated Level 1 requirements
These sectors treat SOC 2 as the minimum baseline for consideration, not a competitive differentiator.
Compounding Business Risk Without SOC 2
Beyond lost deals, vendors without SOC 2 face:
- Increased security questionnaire burden (100+ questions per prospect)
- Longer procurement cycles (4–8 weeks of additional delay)
- Potential removal from enterprise vendor registries
- Contractual exclusion from regulated industry deals
Operational vs. Risk-Driven Adoption
Many vendors pursue SOC 2 because enterprise customers demand it (operationally driven). Others genuinely need the security controls SOC 2 enforces (risk-driven). Both are valid reasons.
Treating it purely as a sales tool leads to "paper compliance" — documented policies that aren't actually implemented. That gap creates legal and reputational exposure when auditors test control effectiveness.
How the SOC 2 Compliance Process Works
SOC 2 is a three-phase program requiring real organizational change—policy, process, and accountability across the business. First-time efforts typically run 6–12 months.
Scope and Readiness Assessment
Scoping is the most consequential early decision. Which systems, services, and data flows are included in the audit boundary directly determines complexity, cost, and duration. A poorly scoped audit results in either an unachievable controls program or an attestation that doesn't satisfy customer requirements.
Common scoping mistake: Software vendors often include their entire technology environment to appear more credible. This inflates costs and extends timelines. A tighter, well-defined scope—focused on systems that directly handle customer data—produces a faster, more achievable attestation that still satisfies enterprise buyers.
Key scoping questions:
- Which systems process, store, or transmit customer data?
- Which Trust Services Criteria do your customers require?
- What is the minimum boundary that satisfies contractual obligations?
Controls Implementation and Evidence Collection
This phase maps existing practices to SOC 2 Trust Services Criteria, closes gaps, and builds the evidence trail auditors will test.
Core controls required:
- Access management (user provisioning, de-provisioning, role-based access)
- Vulnerability management (patching, scanning, remediation tracking)
- Incident response (detection, escalation, communication procedures)
- Change management (code deployment, infrastructure changes, approval workflows)
- Vendor risk management (third-party assessments, contracts, monitoring)
Compliance automation platforms (Vanta, Drata, Secureframe) accelerate evidence collection through API integrations. They require expert judgment to configure correctly, though.
More importantly, no tool replaces organizational change. New access controls, vendor oversight procedures, incident response workflows, and employee training must be implemented and sustained—not just documented.
Audit and Attestation
A licensed CPA firm conducts the audit by testing control design (Type 1) or operating effectiveness over the review period (Type 2). Auditors request evidence, issue findings, and produce the final SOC 2 report.
Audit process breakdown:
- Pre-audit preparation: Scoping conversations with the auditor, evidence readiness review (4–8 weeks)
- Observation period: Continuous evidence collection over 3–12 months (Type 2 only)
- Fieldwork: Auditor testing, gap identification, management responses (4–6 weeks)
- Report issuance: Final SOC 2 attestation or qualified opinion if material gaps exist

Three variables drive timeline and outcome more than anything else:
- Auditor selection (Big Four firms charge $60,000–$450,000; regional firms charge $20,000–$60,000)
- Evidence readiness (poorly documented controls extend fieldwork)
- Control failures during the observation period (each creates exceptions requiring remediation)
Where the Fractional CISO Fits in the SOC 2 Process
Compliance software tools handle evidence collection and control mapping well, but they cannot make scoping decisions, set risk tolerance, communicate audit status to the board, or drive organizational change. That gap is where most SOC 2 programs stall — not in the tooling, but in the governance.
Strategic Responsibilities a Fractional CISO Owns
A fractional CISO provides the governance function that automation platforms explicitly cannot deliver:
- Defining audit scope and system boundaries based on customer requirements and business risk, not just technical coverage
- Selecting and briefing the auditor, ensuring the engagement is structured for achievable outcomes
- Prioritizing Trust Services Criteria based on contractual obligations and industry expectations
- Establishing escalation thresholds for control failures and audit findings
- Ensuring the security program reflects actual risk posture rather than minimum audit requirements
Board and Executive Reporting
Enterprise customers and boards expect security programs to be reported in measurable, trend-based terms. A fractional CISO translates SOC 2 audit progress, control gaps, and residual risk into plain-English briefings that enable defensible decisions at the leadership level.
Typical reporting includes:
- Monthly one-page summaries covering top risks, trend analysis, and decisions needed
- Audit progress visualization showing milestone completion and evidence readiness
- Control gap assessments framed around business impact, not technical audit language
- Risk posture updates that show what changed since the last briefing
This communication layer keeps boards informed without requiring them to interpret technical audit terminology or CPA firm testing methodologies.
Cost and Commitment Advantage
Most growth-stage and mid-market software companies cannot justify or afford a full-time CISO. Median U.S. CISO total compensation reaches $971,000, pricing out smaller vendors entirely. A fractional CISO provides strategic security leadership at $3,000–$15,000 per month—delivering a 90-day plan with owners and measurable outcomes without permanent overhead.
Tyson Martin's fractional CISO engagements follow this structure: audit oversight, scope definition aligned to customer contracts, auditor relationship management, and board-level reporting. The model works for a first SOC 2 and stays relevant through ongoing annual cycles.
Ongoing Governance After Initial Attestation
That ongoing engagement model matters because SOC 2 Type 2 doesn't end at attestation. Annual renewal, continuous evidence collection, and a living security program are ongoing requirements. A fractional CISO provides continuous oversight that keeps the program inspection-ready and aligned with business changes, rather than scrambling for evidence 60 days before each audit cycle.
Post-attestation responsibilities include:
- Maintaining evidence collection workflows
- Monitoring control effectiveness throughout the year
- Coordinating with auditors for annual renewal
- Updating scope and controls as the business evolves
- Reporting compliance status and residual risk to leadership
Common Mistakes and Misconceptions About SOC 2 for Software Vendors
Over-Scoping the Audit Boundary
Software vendors often attempt to include their entire technology environment in the audit boundary to appear more credible. This backfires. Including systems that don't directly impact customer data security—such as internal HR systems, marketing websites, or development sandboxes—inflates costs and extends timelines unnecessarily.
A tight, well-scoped boundary—covering only systems that process, store, or transmit customer data—produces a faster attestation that still satisfies enterprise buyers. Keep in mind that audit scope and actual security program coverage are separate things: you can (and should) secure systems outside the boundary without subjecting them to annual CPA testing.
Scoping discipline also makes the next mistake easier to avoid.
Compliance Software ≠ Compliance
Automated tools reduce time and cost, but they don't implement your controls—your organization does. Access controls, vendor oversight, incident response, and employee training are operational commitments, not documentation exercises.
When documented policies aren't followed consistently, auditors note testing exceptions. Enough exceptions—particularly improperly designed controls or multiple failures within a single Trust Services Criterion—produce a qualified opinion. That outcome signals material compliance gaps to the enterprise buyers you're trying to close.
Leadership Ownership Gap
Many software vendors assign SOC 2 to a CTO or engineering lead who lacks security governance expertise and bandwidth to drive the program. When the compliance effort lacks a dedicated security owner with decision rights, the program breaks down in consistent ways:
- Controls are documented but not implemented
- Evidence collection becomes a last-minute scramble
- Audit findings are misinterpreted or ignored
- Board communication is reactive, not strategic
- The program stalls between annual audit cycles
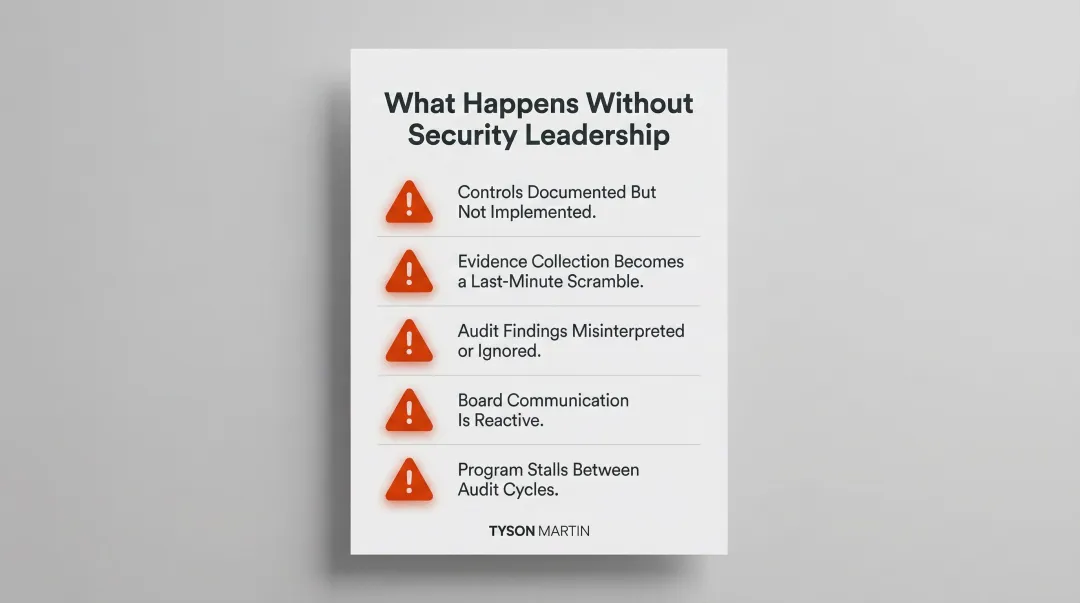
An interim or fractional CISO is built for this situation: focused ownership, security governance experience, and the ability to drive execution without the overhead of a permanent hire.
Frequently Asked Questions
What is a fractional CISO?
A fractional CISO is an experienced security executive who works with an organization on a part-time or engagement basis, providing strategic security leadership(compliance program oversight, board reporting, and risk governance) without the cost of a full-time hire.
How hard is it to get SOC 2 compliance?
SOC 2 compliance typically takes 6–12 months for a first-time effort and requires significant organizational change, including new controls, policies, and procedures. Difficulty scales with audit scope and security maturity — organizations without experienced security leadership guiding the process almost always take longer and remediate more findings.
Is SOC 2 legally required?
SOC 2 is voluntary, not a legal mandate, but it is increasingly required contractually by enterprise customers. For software vendors selling into regulated industries, financial services, healthcare, or large enterprise accounts, it is a market requirement.
How often does SOC 2 need to be updated?
SOC 2 Type 2 reports cover a defined review period (typically 12 months) and must be renewed annually to maintain credibility. The underlying security program requires continuous evidence collection throughout the year — not a sprint in the weeks before the audit.
Is the CISO responsible for the SOC?
SOC 2 is a cross-functional effort involving IT, legal, HR, and operations, but the CISO (or fractional CISO) typically owns the security program it attests to. That means audit scoping, controls oversight, auditor relationships, and executive reporting on compliance status.