Introduction
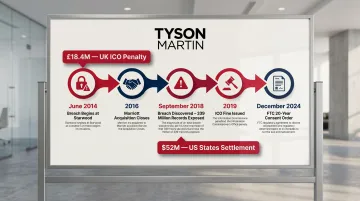
For decades, M&A due diligence followed a predictable playbook: audit the financials, validate the IP, review key contracts, and move to close. But this framework now misses the source of some of the most expensive post-close surprises—regulatory and privacy exposure embedded in how the target company handles data. The problem isn't theoretical. The UK's Information Commissioner's Office fined Marriott £18.4 million for a breach that began at Starwood two years before Marriott acquired it, explicitly citing the buyer's failure to conduct sufficient due diligence. The FTC finalized a consent order in December 2024 requiring Marriott to implement a comprehensive security program with 20 years of annual certifications—inherited exposure that now defines a generation of compliance obligations.
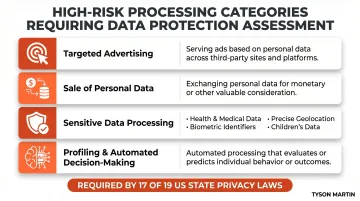
Nineteen US states now impose comprehensive privacy laws, most requiring data protection assessments for high-risk processing activities including targeted advertising, sale of personal data, and automated decision-making. GDPR adds cross-border complexity for any target processing EU data. Virtually any company handling consumer or employee data carries regulatory exposure that must be examined before signing.
The scale of that exposure shows up in deal outcomes. According to a 2019 Forescout study of 2,700 global decision-makers, 53% encountered critical cybersecurity issues or incidents that jeopardized M&A deals, and 46% discovered data breaches at target companies after acquisition was completed. The result: 65% experienced buyer's remorse specifically due to cybersecurity concerns surfacing post-close.
Acquirers who skip or superficially conduct regulatory and privacy exposure assessments don't avoid the liability—they inherit it blind.
TL;DR
- A regulatory and privacy exposure assessment evaluates how a target collects, uses, and shares personal data—and whether that activity creates legal or financial risk for the acquirer
- Regulators don't pause enforcement because a deal is underway; inherited liability transfers at close
- High-risk categories include undisclosed breaches, privacy gaps, vendor exposure, and unmet state assessment obligations
- Assessment covers scope, documentation, technical review, vendor exposure, risk quantification, and deal term translation
- Boards that treat this as a checkbox exercise rather than decision input pay for it later
What Is a Regulatory and Privacy Exposure Assessment in M&A?
A regulatory and privacy exposure assessment in M&A is a targeted evaluation of whether a target company's data practices, privacy governance, and regulatory compliance posture create material risk for the acquirer. Conducted before deal close, findings can directly influence valuation, deal structure, or renegotiation.
Unlike standard IT due diligence—which verifies whether systems are patched and secure—a regulatory and privacy exposure assessment examines the legal and operational standing of the target's data practices: what regulatory obligations exist, whether those obligations have been met, and what enforcement exposure the acquirer would inherit.
The distinction matters because technical security and legal compliance are not synonymous. A target can have strong network security but fail to document required data protection assessments, creating compliance gaps that trigger enforcement risk post-close.
Types of Assessments in M&A Context
The right combination depends on the target's industry, data types, and geographic footprint:
- Privacy Impact Assessments (PIAs): Examine how personal data collection and processing affects individual privacy rights under applicable law
- Data Protection Assessments (DPAs): Mandated by most US state privacy laws for high-risk processing; absence signals governance gaps
- Regulatory Risk Assessments: Map the delta between current practices and legal obligations across all applicable frameworks
- Vendor Risk Assessments: Surface third-party data sharing relationships, processor agreements, and inherited liability
Skipping any category leaves blind spots that surface as enforcement actions, indemnification disputes, or R&W insurance exclusions after close.
Why Regulatory and Privacy Exposure Can Sink or Reshape a Deal
Liability Transfer Principle
When a deal closes, the acquirer takes on the target's full regulatory history: open investigations, unresolved privacy obligations, and penalties already accrued or likely to be imposed. A consent decree with a regulator doesn't disappear in a merger.
The Department of Justice settled an $8.4 million False Claims Act case in 2025 against a defense contractor and its successor company for pre-acquisition cybersecurity failures, explicitly naming the acquirer as the "successor in liability" for violations that occurred years before the transaction. The FTC holds the same authority — enforcement actions against acquirers based on the target's pre-close conduct are an established tool.
The Enforcement Timing Problem
Regulatory investigations move on their own timelines. An acquirer that closes a deal while a state attorney general investigation into the target's data practices is ongoing becomes the subject of that investigation. The Marriott-Starwood case illustrates the scale of this risk: a cyber-attack on Starwood's reservation database began in June 2014, went undetected through the 2016 acquisition, and wasn't discovered until September 2018—affecting 339 million guest records worldwide. The ICO's final penalty notice explicitly stated that Marriott "failed to undertake sufficient due diligence when it bought Starwood and should also have done more to secure its systems." The cost: £18.4 million from the ICO, $52 million in settlements with 49 US states and DC, and a 20-year FTC consent order.
State Privacy Law Patchwork Complexity
19 US states now impose comprehensive privacy laws, most requiring data protection assessments for specific activities. A target operating across multiple states may have unfulfilled obligations tied to:
- Targeted advertising and sale of personal data
- Processing sensitive data (health, biometric, precise geolocation, children's data)
- AI-based profiling and automated decision-making
These aren't operational gaps — they're statutory violations. The acquirer inherits the compliance shortfall and enforcement exposure even if its own operations were previously clean.
Deal Structure and Insurance Implications
Findings from a privacy and regulatory exposure assessment directly affect representations and warranties insurance coverage. According to McGriff and Thomson Reuters, inadequate cyber diligence now leads to broad exclusions, lower sub-limits, or total carve-outs from R&W policies. Undisclosed or unassessed exposure can void coverage entirely or create indemnification gaps that leave boards exposed. R&W insurers increasingly require evidence of specific security controls—MFA, incident response plans, penetration testing, vendor risk assessments—before providing coverage for cyber-related representations.
Verizon reduced its acquisition price for Yahoo by $350 million (from $4.83 billion to $4.48 billion) following disclosure of breaches affecting over 3 billion user accounts. According to a 2019 (ISC)² study, 96% of M&A executives take cybersecurity readiness into account when determining the target's value, and 86% say a publicly reported breach detracts from the acquisition price.
Fiduciary Governance Angle
For boards and audit committees approving an acquisition, failing to commission a regulatory and privacy exposure assessment is a governance gap, not just an operational oversight. Directors authorizing a deal should be asking:
- Was this assessment conducted before close?
- What did it find, and what remains unresolved?
- What specific risk is the board accepting?
The Marriott case established that regulators treat insufficient diligence as the acquirer's failure — and the board's approval record becomes part of that story. Asking these questions before the vote is the difference between defensible governance and an explanation you make after enforcement begins.
Key Risk Categories to Evaluate in a Target Company
Undisclosed or Unresolved Security Incidents
Acquirers should examine whether the target has experienced breaches, ransomware events, or unauthorized access that were not fully disclosed, reported to regulators, or remediated. Many state breach notification laws and SEC rules require timely disclosure—if the target didn't comply, the acquirer inherits the enforcement risk.
According to the 2019 (ISC)² M&A study, 57% of M&A executives were surprised to learn of an unreported breach during the audit process, and 49% reported deals canceled or derailed after previously undisclosed breaches surfaced.

Key due diligence questions for breach history:
- Complete incident and breach logs for the past 5 years
- Regulatory notifications submitted (state AGs, FTC, SEC, international DPAs)
- Forensic investigation reports and remediation evidence
- Pending or threatened litigation related to incidents
- Cyber insurance claims history and current coverage terms
Privacy Program Maturity and Regulatory Compliance Status
Assess whether the target has a functioning privacy program—data mapping, privacy notices, consent mechanisms, documented policies, and compliance with applicable frameworks (GDPR, CCPA/CPRA, HIPAA, GLBA). A program that exists on paper but isn't operational is a red flag.
Key evaluation areas include:
- Records of processing activities or data flow maps
- Privacy policies aligned with actual data practices
- Consent and opt-out mechanisms that function as described
- Data subject rights request handling (access, deletion, portability)
- Cross-border transfer mechanisms for international data flows
Gaps between stated policy and operational reality create direct regulatory exposure—findings of this type routinely reshape deal terms or pricing.
Third-Party and Vendor Exposure
The target's vendors, processors, and data-sharing partners create inherited exposure. If a target shares consumer data with an analytics or advertising vendor without a compliant data processing agreement, the acquirer assumes that risk. This exposure is especially acute when vendor contracts haven't been reviewed against current regulatory standards.
Vendor risk evaluation should cover:
- Complete inventory of vendors receiving personal data
- Data processing agreements (DPAs) compliant with applicable law
- Vendor security assessments and audit evidence
- Vendor breach or enforcement history
- High-risk vendors: advertising networks, analytics platforms, AI/ML processors, offshore processors
Tyson Martin's due diligence process explicitly surfaces vendor contract gaps that create regulatory exposure—identifying third-party relationships where data sharing occurred without documented authorization or compliant agreements.
Active or Pending Regulatory Enforcement Actions
Conduct a targeted search for whether the target has received regulatory inquiries, civil investigative demands, FTC or state AG actions, or consent orders related to data practices. Targets rarely disclose these voluntarily.
Standard sources for surfacing enforcement actions:
- FTC Consent Order Database (ftc.gov/enforcement/cases-proceedings)
- SEC EDGAR filings for public companies (litigation risk factors)
- Federal court PACER records for pending cases
- State AG enforcement databases (varies by state)
- International regulatory databases (ICO, EDPB for GDPR enforcement)
High-Risk Data Processing Activities Requiring Documented Assessments
Under applicable state privacy laws, certain processing activities require documented data protection assessments:
- Targeted advertising and cross-contextual behavioral advertising
- Sale of personal data for monetary or other valuable consideration
- Processing sensitive data (health, biometric, genetic, precise geolocation, children's data)
- Profiling and automated decision-making that creates risk of unfair treatment or disparate impact
If the target conducts these activities without documented assessments, the acquirer assumes both the compliance gap and enforcement exposure. Most of the 19 states with comprehensive privacy laws require DPAs for these activities—notable exceptions are Utah and Iowa. Absent documentation, each activity becomes a quantifiable liability that due diligence must surface before close.
How to Conduct a Regulatory and Privacy Exposure Assessment — Step by Step
This section walks through the practical stages of a regulatory and privacy exposure assessment in an M&A context. The order matters: each stage builds on the last, and skipping steps—particularly documentation review or vendor scoping—creates blind spots that surface after close.
Step 1 – Define Scope and Regulatory Footprint
Identify the target's geographic presence, industries, customer types, and data categories handled. This determines which regulatory frameworks apply and sets the assessment perimeter.
Key scoping questions:
- Where does the target operate and where is data processed?
- What types of data are collected (consumer, employee, health, financial, children's)?
- Which regulatory frameworks apply (GDPR, CCPA/CPRA, state laws, HIPAA, GLBA)?
- What high-risk processing activities occur (advertising, sale, profiling, AI)?
Step 2 – Request and Review Documentation
Build a structured documentation request and treat gaps as findings. A mature privacy program has these documents readily available; missing records signal program immaturity before a single interview is conducted.
Based on guidance from WilmerHale and the Association of Corporate Counsel, an M&A privacy diligence checklist should request:
- Current and historical privacy policies
- Data controller vs. processor status documentation
- All breach incident records and regulatory notifications
- Complete regulatory correspondence (FTC, state AGs, DPAs)
- Incident response and business continuity plans
- Data flow documentation and cross-border transfer mechanisms
- Third-party data processing agreements
- Consent and opt-out mechanism records
Step 3 – Conduct Technical and Process Assessment
Move beyond documents to evaluate whether stated practices match operational reality. Key areas to assess:
- How data is actually collected, stored, and deleted
- Whether consent mechanisms function as described
- Whether access controls and data minimization are enforced
- Whether privacy obligations are embedded in product and engineering workflows
Kroll's cybersecurity due diligence framework adds three additional activities to this phase: management interviews with IT and security leadership; review of prior third-party audit and penetration testing reports; and a compromise assessment scanning for indicators of active or historical breach.
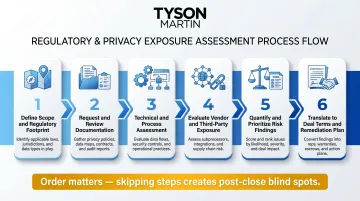
Step 4 – Evaluate Vendor and Third-Party Exposure
Map all vendors and third parties receiving personal data from the target. For each, assess whether a compliant data processing agreement is in place, whether the vendor's security and privacy posture was evaluated, and whether vendors have had their own incidents or enforcement actions. Flag advertising, analytics, or AI vendors receiving sensitive data without documented authorization.
Step 5 – Quantify and Prioritize Risk Findings
Vendor findings feed directly into risk quantification. Translate everything into a risk register structured for deal teams — each entry should include the applicable regulation, the nature of the gap, estimated enforcement or remediation cost, and a likelihood rating.
Prioritize findings that could affect deal structure, pricing, or close conditions separately from those addressable through a post-close remediation plan.
Step 6 – Translate to Deal Terms and a Post-Close Remediation Plan
Work with legal counsel and deal leadership to incorporate material findings into reps and warranties language, escrow or holdback structures, or specific closing conditions. For findings that are manageable but real, develop a 90-day post-close plan with owners, timelines, and measurable remediation milestones—not a vague list of recommendations.
Recommended deal structures for cyber risk include:
- Purchase price adjustments sized to quantified remediation costs
- Cyber-specific escrows with release tied to security milestones
- Conditions precedent requiring minimum security deliverables before close
- Longer survival periods for cyber reps with separate liability caps
How Tyson Martin Can Help
Tyson Martin serves as a strategic partner for M&A deal teams who need senior cybersecurity and privacy governance expertise — not a compliance vendor running a checkbox audit. His background spans enterprise-scale organizations including AWS, Home Depot, and Best Buy.
Active roles at the National Association of Corporate Directors, the World Economic Forum's Centre for Cybersecurity, and the NRF CISO Executive Committee mean he brings a board-caliber perspective to what is, at its core, a governance and risk decision.
The Specific Value Tyson Provides in M&A
Tyson steps in as a fractional or interim CISO to lead or direct the regulatory and privacy exposure assessment, converting technical and legal findings into risk summaries boards and general counsel can act on. Findings are structured to influence deal terms directly — not buried in a technical appendix that no one reads before close.
His approach addresses the core problem with traditional M&A cyber diligence: technical audits produce long lists of vulnerabilities that don't map to decision points. Tyson's model starts with the question: what risk are we inheriting, what does it cost to remediate, and how does that change the deal?
What Acquirers and Boards Receive
- Risk posture summary covering top regulatory and privacy exposures, categorized by enforcement likelihood and estimated financial impact
- Finding register tied to deal decisions — each item includes the applicable regulation, gap description, cost estimate, and recommended response (price adjustment, escrow, closing condition, or post-close remediation)
- 90-day post-close remediation plan with defined owners, measurable outcomes, and scheduled work — built for execution, not a shelf report

This isn't a report that sits on a shelf. It's decision infrastructure that protects the deal and clarifies accountability from day one post-close.
Frequently Asked Questions
What risks does a privacy impact assessment identify and manage?
A privacy impact assessment maps how personal data is collected, used, stored, and shared, then flags risks such as regulatory non-compliance, unauthorized data sharing, and consent failures. It also identifies exposure from high-risk activities like profiling or processing sensitive data categories.
What is a regulatory risk assessment?
A regulatory risk assessment evaluates whether an organization's operations and data practices comply with applicable laws, identifies gaps and enforcement exposure, and prioritizes findings by the likelihood and magnitude of regulatory action.
How do technology tools compare to a proper regulatory and privacy assessment in M&A diligence?
Technology tools can help acquirers quickly understand a target's technical risk posture by aggregating and prioritizing vulnerability data. They are useful inputs, but they address cyber exposure only—not the legal, compliance, and governance dimensions that a regulatory and privacy assessment must cover.
How can organizations assess compliance with privacy and security standards?
Core methods include structured documentation review, data mapping, gap analysis against applicable frameworks (GDPR, CCPA/CPRA, NIST, ISO), controls assessment, and third-party vendor review. Effective assessments require both technical depth and regulatory fluency—rarely found in a single workstream without experienced oversight.
What privacy and regulatory risks should acquirers specifically look for in M&A diligence?
Top categories include undisclosed breach history, unfulfilled state privacy law assessment obligations, non-compliant vendor agreements, active regulatory investigations, and gaps between stated privacy policies and actual data practices.
How does undisclosed regulatory exposure affect deal valuation or post-close outcomes?
Undisclosed regulatory exposure can void R&W insurance coverage, trigger indemnification disputes, and result in post-close enforcement actions against the acquirer. In significant cases, it forces deal renegotiation or financial write-downs that were not priced into the transaction.