Introduction
M&A transactions are scrutinized down to the decimal on financials, yet cyber risk — often the most consequential hidden liability — is consistently deprioritized until after the deal closes.
When undisclosed breaches, weak controls, or inherited vulnerabilities surface post-close, they don't show up as tidy line items. They show up as renegotiated prices, regulatory fines, and boards facing questions they can't answer.
In 2024, 53% of dealmakers discovered significant cybersecurity issues only after closing, triggering unexpected remediation spending and governance challenges. Cyber due diligence is a governance responsibility that belongs at the decision-making level. What follows is what happens when it isn't treated that way.
TL;DR
- Cybersecurity failures in M&A due diligence reliably destroy deal value — and most are preventable
- Inherited cyber vulnerabilities translate directly into valuation cuts, regulatory penalties, and integration setbacks that erode the original deal thesis
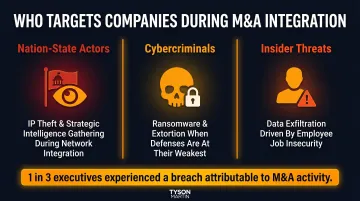
- The M&A integration window is among the most actively targeted periods by threat actors: 1 in 3 executives experienced a data breach attributable to M&A activity
- Most post-close surprises were discoverable pre-signing; the gap is governance rigor, not missing information
- Boards that treat cyber due diligence as a technical afterthought are accepting risks that belong on the term sheet
What Is Cyber Due Diligence in M&A?
Cyber due diligence is a structured pre-acquisition assessment of the target company's security posture, historical incidents, governance practices, and inherited liabilities, conducted before deal terms are finalized. Ownership sits with deal leadership and the board, not the IT department.
When It Fits in the Deal Lifecycle
Cyber due diligence should begin at or before the letter of intent (LOI) stage, not after exclusivity is signed and financial pressure to close has mounted. Yet 57% of organizations perform cyber due diligence only after the deal closed, rather than during initial evaluation.
This timing matters because:
- Early engagement gives deal teams time to quantify risk before reputational and financial pressure peaks
- Pre-LOI assessments can use outside-in methods (open-source intelligence, external scanning) without full target cooperation
- Findings inform the post-merger integration budget and deal structure before terms are locked
The output of cyber due diligence is a risk-adjusted picture of what the acquirer is actually buying — including what remediation will cost and which liabilities transfer with the deal.
How Cybersecurity Failures Destroy M&A Value
Poor cyber due diligence causes documented, quantifiable damage across deal types, company sizes, and industries. Three failure modes explain how that destruction consistently unfolds.
Failure Mode 1: Valuation and Financial Damage
Undisclosed breaches and security deficiencies have a direct, quantifiable effect on deal price — both through forced renegotiation and post-close remediation costs that were never built into the model.
Why this failure is so damaging:
The global average cost of a data breach reached USD $4.44 million in 2025, down from $4.88 million in 2024 but still representing significant financial exposure. Remediation costs alone can dwarf what cyber assessment would have cost pre-deal.
Documented valuation impact:
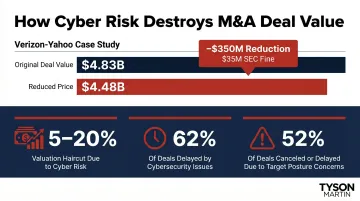
- Verizon-Yahoo: Verizon reduced its acquisition price by $350 million (from $4.83B to $4.48B) following disclosure of two massive data breaches affecting over 1.5 billion accounts. The SEC subsequently fined Yahoo/Altaba $35 million for failing to disclose the 2014 breach during due diligence calls with Verizon
- Industry benchmarks: IBM estimates a 5-20% valuation haircut when significant cyber vulnerabilities are discovered during due diligence
- Deal delays: 62% of M&A deals are delayed due to cybersecurity problems; 52% of respondents have delayed or canceled a deal specifically due to concerns over the target's cybersecurity posture
What gets damaged:
- Deal multiple
- Integration budget
- Synergy timeline
- EBITDA projection
- The financial architecture of the deal thesis itself
Failure Mode 2: Regulatory and Legal Exposure
When an acquirer closes a deal without understanding the target's cyber posture, it inherits not just the assets — but the liability for every undisclosed incident, every unpatched vulnerability, and every compliance gap that predates the transaction.
Why this failure compounds over time:
The Marriott-Starwood case demonstrates how inherited liabilities cross jurisdictions and regulatory regimes. Attackers had been inside Starwood's systems for two years before Marriott's 2016 acquisition. When the breach surfaced in September 2018, Marriott faced consequences across three separate authorities:
- UK ICO fine of £18.4 million under GDPR for insufficient due diligence during the acquisition
- FTC enforcement action requiring a 20-year compliance program
- $52 million penalty paid to 49 US states and the District of Columbia
The ICO established that due diligence is "not time-limited or a one-off requirement" — creating a continuing obligation standard for acquirers.
Current regulatory landscape:
The SEC's cybersecurity disclosure rules, adopted July 26, 2023, create new legal exposure for public companies that fail to identify and disclose material cyber risks:
- Item 1.05 Form 8-K disclosure required within four business days of determining a cybersecurity incident is material
- Annual 10-K disclosure of cybersecurity risk management, strategy, and governance
- Board oversight practices become reportable items
Downstream effects:
- Regulatory standing
- Indemnity exposure
- General counsel's ability to defend the transaction
- Investor confidence under scrutiny from the SEC or data protection authorities
Failure Mode 3: Operational Risk During the Integration Window
Between deal announcement and full system integration, IT teams are distracted, network boundaries are shifting, and attackers actively target companies in transition. This window is structurally exposed — and threat actors know it.
Why this failure is structurally predictable:
IBM reports that 1 in 3 executives experienced a data breach attributable to M&A integration activity. When systems are merging and monitoring responsibilities are in flux, gaps in incident response open — and threat actors move fast to exploit them.
Three categories of threat actors target M&A:
- Nation-state actors: IP theft and strategic advantage during network integration
- Cybercriminals: Ransomware and extortion opportunities when defenses are weakest
- Insider threats: Employees at target companies exfiltrating data due to job insecurity
Integration-specific vulnerabilities:
- Legacy or unsegmented systems from the acquired company introduce lateral movement opportunities that didn't exist before the deal
- Pressure to connect networks before the target's environment has been fully audited ("Day 1 connectivity" risk)
- Inherited technical debt and unpatched systems that serve as entry points
What gets damaged:
- Business continuity
- Customer trust
- Day 1 stability
- Post-close integration timeline
- Whether the deal delivers projected returns
What Happens When Cyber Due Diligence Is Skipped or Rushed
Across documented M&A failures, the risks were rarely unknowable. They went unexamined, or the findings never reached the people with authority to act on them.
Post-Close Discovery Is the Norm, Not the Exception
53% of dealmakers in 2024 discovered significant cybersecurity issues after deal close, triggering unexpected remediation spending and governance challenges. The information existed. The process failed to surface it before signatures were exchanged — and by then, the acquiring organization had already assumed the liability.
The Board-Level Consequence
When cyber gaps surface post-close, boards are left defending decisions made without complete information — to investors, regulators, and in some cases courts. Directors who approved the deal without adequate cyber visibility have limited defense when regulators or shareholders start asking questions.
Director accountability mechanisms:
- SEC disclosure rules require boards to report cybersecurity oversight practices in annual 10-K filings
- Cyber risk governance in targets becomes a reportable item for the acquirer post-close
- Shareholders and regulators can trace governance failures directly to board-level oversight gaps
The Mid-Market Blind Spot
This exposure is sharpest in mid-market transactions, where security infrastructure is thinner and due diligence scrutiny often isn't. Mid-market targets frequently lack:
- Dedicated CISO with clear reporting lines (relying instead on general IT managers)
- Endpoint detection and response (EDR) tools (relying on legacy antivirus)
- Formal, tested incident response plans
- Written information security policies
This security debt is systematic in mid-market transactions, yet mid-market deals often receive less rigorous cyber due diligence than large-cap acquisitions — creating disproportionate exposure.
What the Board Needs to Demand Before Any Deal Closes
The board doesn't need to run a penetration test. It does need to hold management and deal teams accountable for answering specific questions before approval. The right questions reveal whether the target has genuine security maturity or just compliance paperwork.
Board-Level Question 1: Governance and Oversight
Does the target have a CISO with clear reporting lines, board-level visibility into cyber risk, and documented incident disclosure procedures?
If the answer is vague, that vagueness is itself a risk signal. 82% of CISOs now report directly to the CEO, up from 47% in 2023. A CISO who reports to the CIO or CTO instead of the CEO or board is a concrete governance gap — not a maybe.
Board-Level Question 2: Incident History
Has the target experienced any breaches, regulatory findings, or significant incidents in the past three to five years?
Are forensic reports available, and have root causes been remediated? Ask to see evidence of action taken, not just documentation of events. The Verizon-Yahoo case failed precisely at this point: during a June 27, 2016 due diligence call, Yahoo discussed four minor breaches but failed to disclose the massive 2014 breach affecting 500 million accounts.
Board-Level Question 3: Third-Party and Vendor Risk
Who are the critical vendors, cloud providers, and data processors the target uses, and what security obligations exist in those contracts?
Acquirers inherit the target's entire vendor ecosystem and fourth-party exposure, not just its internal systems. Vulnerabilities in shared service providers (such as the 2021 SITA breach affecting over 500,000 frequent flyer records across multiple airlines) can create systemic risks across integrated environments.
Board-Level Question 4: Remediation Cost and Deal Terms
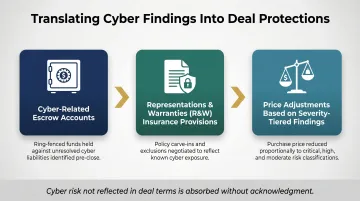
Have the cyber findings been translated into a remediation cost estimate that can be used to adjust price, structure escrow, or define indemnities?
If cyber risk isn't reflected in deal terms, the acquirer is absorbing it without acknowledgment. Use findings to negotiate:
- Cyber-related escrow accounts
- Representations and warranties (R&W) insurance provisions
- Price adjustments based on severity-tiered findings
Boards navigating M&A cybersecurity risk should engage a fractional CISO or board-level advisor before the deal closes — not after. The right advisor translates technical findings into a plain-language risk posture, negotiates terms with evidence, and delivers a 90-day integration plan with owners and measurable outcomes.
Conclusion
Every acquisition is now a technology acquisition, which means every acquisition carries cyber risk — and that risk either gets priced and managed or it gets inherited and discovered.
The organizations that do this well use cyber due diligence as negotiating leverage, a driver of faster integration, and a credibility signal to investors and regulators. That's the difference between boards that control the narrative and boards that react to it.
The NACD's 2026 Cyber Risk Handbook and the World Economic Forum's Principles for Board Governance of Cyber Risk both explicitly classify M&A cyber due diligence as a board-level fiduciary function — not a technical exercise to be delegated below the C-suite.
Boards that own this process get deals done faster, integrate more cleanly, and face fewer post-close surprises. The ones that delegate it find out what they missed at the worst possible time.
Frequently Asked Questions
What is cyber due diligence?
Cyber due diligence is a structured pre-acquisition review of a target company's cybersecurity posture, historical incidents, governance controls, and inherited liabilities, conducted to quantify risk before deal terms are finalized. It provides a risk-adjusted view of what the acquirer is actually buying and what it will cost to own it.
How do cybersecurity issues affect M&A deal valuation?
Undisclosed breaches or weak security controls can trigger direct price reductions — as seen in the Verizon-Yahoo deal ($350 million reduction) — force post-close remediation spending that wasn't in the deal model, and delay synergy realization. All of these erode the original deal thesis and financial projections.
What should a board ask before approving an acquisition?
Boards should demand clear answers to four questions before signing off:
- Does the target have a CISO with defined reporting lines and board oversight?
- Has the target experienced any breaches in the past 3-5 years with documented remediation?
- Who are the critical vendors and what security obligations exist?
- Have cyber findings been translated into price adjustments, escrow, or indemnities?
When in the M&A process should cybersecurity due diligence begin?
Cyber due diligence should begin at or before the letter of intent (LOI) stage — not after exclusivity is signed. Early engagement gives deal teams time to quantify risk before pressure to close mounts, and allows findings to shape the post-merger integration budget.
Where do 90% of all cyber incidents begin?
Most cyber incidents originate through human entry points — primarily phishing and social engineering. The Verizon DBIR 2025 found that human factors were linked to 60% of breaches, which is why assessing a target's security awareness culture and email controls is central to any cyber due diligence review.
What are the top 5 major threats to cybersecurity?
The five threat categories most relevant to M&A due diligence are:
- Ransomware — involved in 44% of breaches in 2025
- Phishing and social engineering — linked to 60% of breaches via human error
- Stolen credentials — present in 29% of breaches
- Supply chain and third-party compromise — often hidden in target environments
- Unpatched vulnerabilities in legacy systems — common in acquisition targets
All five can be assessed and quantified during pre-acquisition review.