Introduction
Third-party vendors now represent one of the most consequential attack surfaces a CISO must defend. The evidence is documented, expensive, and increasingly public:
- The SolarWinds attack in 2020 compromised up to 18,000 customers through a single trojanized software update.
- The 2023 MOVEit breach exposed data from more than 8,000 organizations globally.
- In 2025, 30% of all data breaches involved a third party—a 100% increase from the previous year.
Most organizations have some vendor review process in place. The problem is not absence but inconsistency: assessment frequency varies, depth varies, ownership is unclear, and escalation protocols differ dramatically across teams. These governance gaps persist even in mature security programs, leaving CISOs exposed when incidents occur and regulators ask who was accountable.
That gap is exactly what this guide addresses. It walks CISOs through how to build and run a defensible third-party risk management program—from the prerequisites and vendor tiering that must happen before any assessment begins, through structured review processes, board reporting frameworks, and the most common failures to avoid.
TLDR
- TPRM is a core CISO responsibility—vendor failures trigger breaches, regulatory penalties, and operational disruption
- Effective programs start with a complete vendor inventory, apply risk-based tiering, and use structured assessments rather than annual questionnaires
- Key threat surfaces to monitor: supply chain attacks, shadow IT, fourth-party exposure, inadequate vendor controls, breach risk, and compliance gaps
- Board reporting should translate vendor risk into business impact, show trend data, and establish clear escalation thresholds
- Common failures: treating TPRM as a one-time event, lacking cross-functional ownership, and applying uniform assessments regardless of vendor tier
What You Need Before Building a TPRM Program
Effective TPRM requires organizational prerequisites before any vendor assessment begins. Jumping into questionnaires without governance foundations creates inconsistency and false assurance. The work that precedes vendor review determines whether your program produces defensible decisions or advisory noise.
Program Governance Readiness
Confirm that executive sponsorship and defined decision rights exist: who approves new vendors, who can pause or terminate vendor relationships, and who escalates to the board. Without this, vendor assessments inform no one and change nothing.
Organizations in leadership transition or without a sitting CISO often benefit from interim or fractional CISO support to establish this foundation quickly. The interim model can lock in decision rights, build cross-functional coordination, and create a repeatable governance structure before permanent leadership takes over.
Vendor Inventory and Risk Tiers
Establish a complete, current inventory of all third-party relationships before assessing any of them. The scale is larger than most programs anticipate:
- Organizations maintain an average of 2,643 third parties, yet 61% lack a comprehensive inventory of who has access to sensitive data
- 60% of organizations work with more than 1,000 third parties
- By 2027, 75% of employees will acquire or modify technology outside IT's visibility, up from 41% in 2022
Once the inventory exists, define risk tiers based on data access, system criticality, and regulatory sensitivity. Shadow IT vendors — onboarded outside formal approval — are often the biggest gap.
Regulatory Baseline
Identify which regulations apply to your vendor relationships before choosing assessment frameworks. Regulatory requirements should drive the scope and frequency of vendor reviews:
- DORA (EU): Mandates due diligence on concentration risks before contracting with ICT providers and establishes oversight for critical third-party providers
- NIST SP 800-161: Requires satisfaction of security requirements in contracts, flow-down to subcontractors, and periodic supplier revalidation
- HIPAA: Requires Business Associate Agreements ensuring safeguards for protected health information and subcontractor oversight
- GDPR Article 28: Mandates written contracts requiring processors to follow controller instructions and pass obligations to sub-processors
- FTC Safeguards Rule: Requires financial institutions to oversee service providers and periodically assess their risks
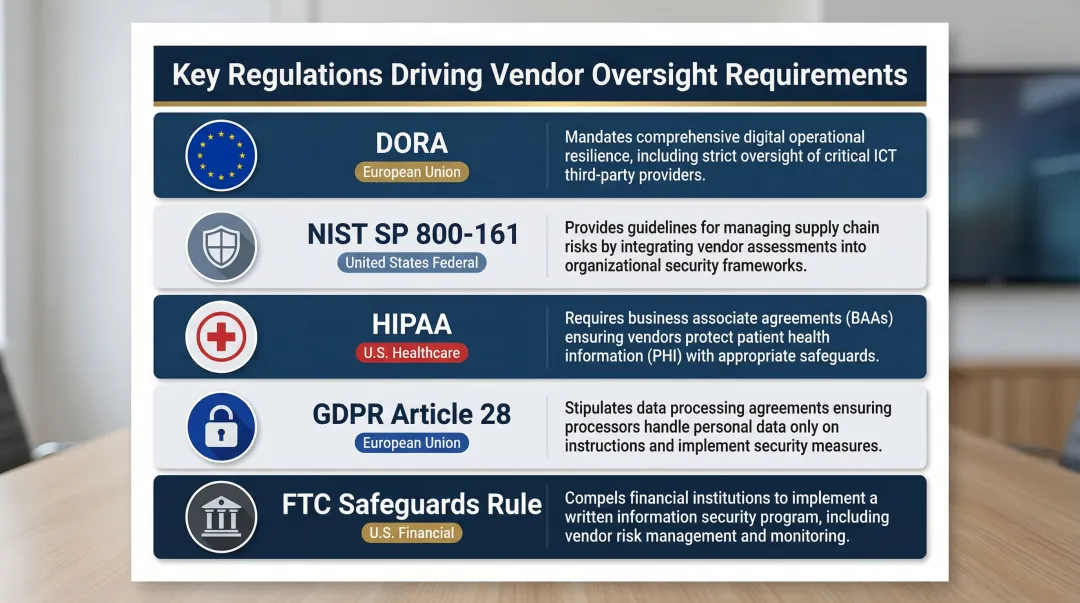
In 2020, HHS OCR fined Athens Orthopedic Clinic $1.5 million for systemic noncompliance, including failure to enter into business associate agreements with three vendors. In 2024, Providence Medical Institute paid $240,000 for HIPAA violations that included the absence of a business associate agreement with an IT vendor managing ePHI.
How CISOs Should Build a Third-Party Risk Management Program
This section outlines a phased, repeatable process that must be inspectable—meaning every step should produce documentation that can be shown to auditors, legal counsel, or the board.
Step 1: Conduct Vendor Discovery and Tiering
Map all third-party relationships across the organization—including IT, procurement, HR platforms, and business unit tools. Classify each vendor into risk tiers (critical, high, moderate, low) based on:
- Does the vendor access regulated data, customer PII, or intellectual property?
- Could vendor failure halt revenue-generating operations or critical business functions?
- Does the vendor relationship trigger compliance obligations under HIPAA, GDPR, DORA, or other frameworks?
Flag shadow IT relationships discovered during this process and initiate a formal onboarding or termination decision for each. Research shows that organizations assess an average of only 36% of their third parties, leaving significant coverage gaps.
Step 2: Standardize the Risk Assessment Process
Apply structured security questionnaires aligned to the risk tier. Critical vendors should undergo comprehensive assessments covering security controls, incident response procedures, business continuity plans, and access management. Lower-tier vendors can use streamlined versions.
How you structure assessments matters — but so does how often you run them. Annual-only cycles leave organizations exposed: 60% report that completing a single third-party assessment takes 4 to 12+ months, and 45% receive updates on vendor risk posture changes only yearly or never.
That gap carries real cost. Organizations experience an average of 12 data breaches or security incidents caused by third parties per year, many occurring between assessment cycles. Assessment frequency should match risk tier: critical vendors may require quarterly reviews and continuous monitoring, while lower-risk vendors may warrant annual cadences.
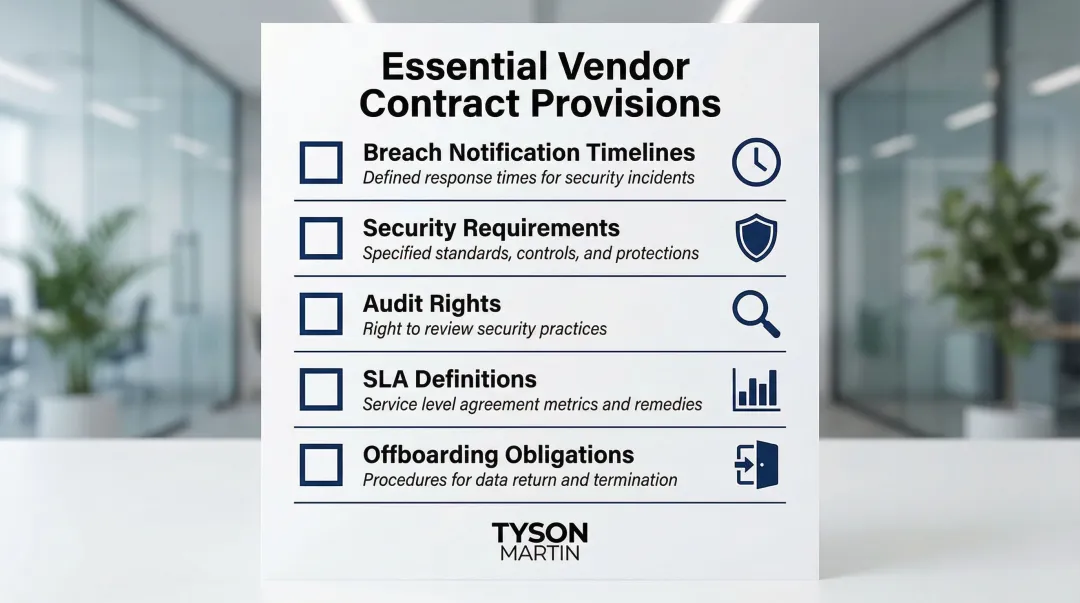
Step 3: Establish Contractual Accountability
Ensure vendor contracts include breach notification timelines, security requirements, audit rights, SLA definitions, and offboarding data destruction obligations. Many organizations discover these clauses are missing or vague only after an incident occurs.
Key contractual provisions:
- Breach notification timelines: Maximum window (such as 24-48 hours) from the vendor's discovery to notification
- Security requirements: Minimum controls, encryption standards, access restrictions, and compliance certifications
- Audit rights: Right to audit vendor security controls directly or through third-party assessors
- SLA definitions: Uptime requirements, response times, and penalties for non-performance
- Offboarding obligations: Certified data destruction and credential return within defined timeframes
Step 4: Implement Continuous Monitoring
Supplement point-in-time assessments with ongoing signals: news monitoring for vendor incidents, threat intelligence feeds, and periodic re-assessments triggered by defined events (such as a vendor acquisition, a major breach in their sector, or regulatory action against them).
Define escalation thresholds in advance. Not every change in a vendor's risk posture warrants the same response:
- Immediate CISO review: Active breach, ransomware incident, or regulatory action involving the vendor
- Scheduled reassessment: Leadership change, acquisition, or sector-wide threat activity
- Board notification: Material exposure to regulated data, operational disruption risk, or regulatory reporting trigger
This prevents both under-reporting of serious issues and over-burdening the board with noise.
Step 5: Integrate TPRM Into Incident Response and Business Continuity
Ensure vendor-related failure scenarios are included in tabletop exercises and business continuity plans. Map critical vendors to the business functions they support so impact can be assessed instantly when an incident occurs.
Establish a documented incident communication protocol for third-party breaches:
- Who internally is notified first (CISO, legal, privacy officer, CEO)?
- What the vendor is required to communicate and when?
- What regulatory reporting obligations are triggered?
- What customer or partner notification is required?
The Top Third-Party Risks Every CISO Must Monitor
These six risk categories most commonly create exposure in enterprise environments. Each requires a specific control or monitoring posture.
Inadequate Vendor Security Controls
Many smaller vendors lack mature security programs and are targeted precisely because they provide trusted access to larger organizations. Continuous risk scoring rather than annual snapshots is the recommended control.
Third-party vendor and supply chain compromises cost an average of $4.91 million, and supply chain compromises take the longest to detect and contain, averaging 267 days — nearly nine months.
Mitigation controls:
- Replace point-in-time assessments with continuous risk scoring platforms
- Tier vendors by access level and apply proportionate scrutiny
- Include security maturity requirements in vendor qualification criteria
Third-Party Data Breach Risk
Breaches originating at vendors are harder to detect because they don't appear on your own network. This makes breach notification SLAs in contracts critical, not optional. In 2025, 30% of all breaches involved a third party, representing a 100% increase from the previous year.
Mitigation controls:
- Contractual breach notification timelines (24-48 hours)
- Vendor security posture monitoring via continuous assessment platforms
- Incident response playbooks that include third-party breach scenarios
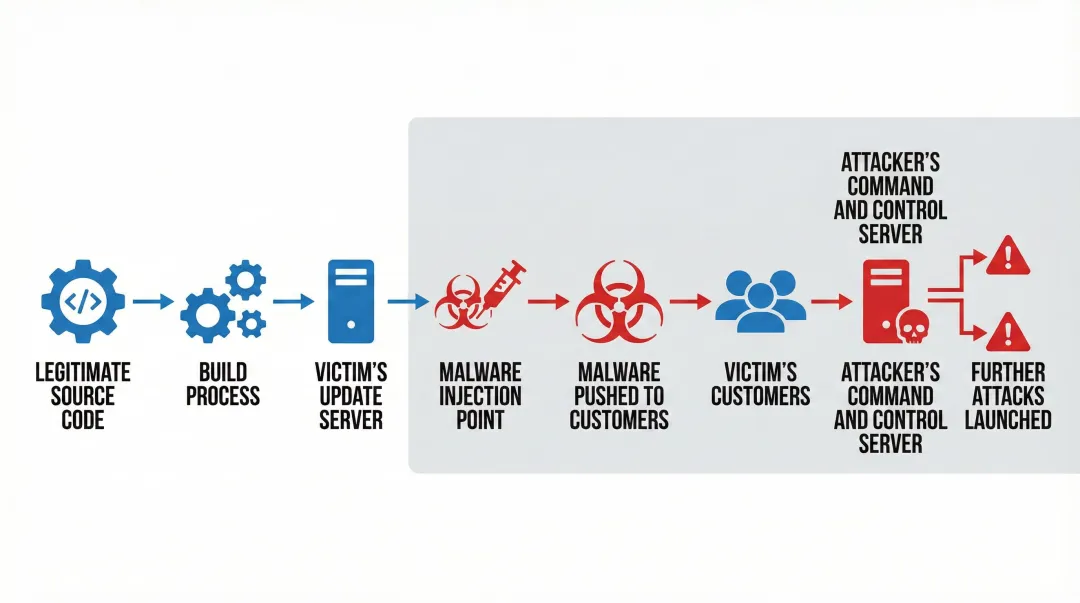
Supply Chain and Software Integrity Risks
Attackers embed threats through legitimate software updates, code dependencies, and firmware. These threats require procurement-level controls, not just IT reviews.
Notable supply chain attacks:
- XZ Utils (2024): Malicious backdoor (CVE-2024-3094) inserted into Linux xz utility, allowing remote code execution with specific SSH keys
- 3CX DesktopApp (2023): Trojanized installer spread malware via prior compromise of Trading Technologies' X_TRADER software
- Codecov (2021): Attackers modified Bash Uploader script to export credentials, tokens, and keys from customers' CI environments
The number of attacks detected in the software supply chain doubled in 2024. Procurement-level response requires:
- Software bill of materials (SBOM) requirements in vendor contracts
- Secure build pipeline validation before deployment approval
- Dependency scanning integrated into the vendor onboarding process
Shadow IT and Unapproved Vendors
Undiscovered vendor relationships represent the biggest blind spot in any TPRM program. Discovery tools and cross-functional onboarding gates — requiring security review before any vendor integration is approved — are the core mitigation.
With 75% of employees projected to acquire technology outside IT's visibility by 2027, CISOs must implement discovery mechanisms that surface unapproved SaaS tools, cloud services, and vendor relationships before they create risk.
Fourth-Party and Nth-Party Risks
Third-party risk refers to direct vendors. Fourth-party risk arises from vendors' vendors. CISOs are accountable for this extended chain even though they have no direct visibility.
The exposure gap is real: 26% of organizations do not assess or monitor fourth parties at all, yet 4.5% of breaches now extend to fourth parties — meaning one vendor compromise can cascade through your entire extended supply chain. Only 58% of organizations review their third parties' TPRM programs to verify fourth-party oversight exists.
Mitigation approach:
- Require vendors to disclose their own TPRM practices in contracts
- Request attestations confirming vendors apply equivalent security standards to their subcontractors
- Review vendors' supplier oversight procedures during assessments
Regulatory Compliance Gaps
Non-compliant vendor behavior can create liability for the contracting organization, not just the vendor. This is especially acute in regulated industries where regulators increasingly hold organizations accountable for their vendors' compliance failures — not just their own.
Mitigation controls:
- Contractual compliance attestations tied to renewal cycles
- Automated tracking of vendor certification expiration (SOC 2, ISO 27001, PCI DSS)
- Right-to-audit clauses for vendors handling regulated data
How CISOs Should Report Third-Party Risk to the Board
This is where most TPRM programs lose their strategic value. Sound programs that can't translate risk into business terms fail to secure funding, escalation authority, or board-level accountability — no matter how thorough the underlying work.
Translate Risk Into Business Impact Language
Board reporting should frame vendor risk in terms of operational disruption potential, regulatory exposure in dollar or reputational terms, and concentration risk—not vulnerability counts or questionnaire scores.
Effective board reporting means plain-English risk posture and what changed since the last briefing. The questions that matter at the board level:
- Which vendors could stop revenue if they failed?
- What regulatory penalties could result from vendor non-compliance?
- Where is vendor concentration risk creating single points of failure?
- What remediation actions are underway and who owns them?
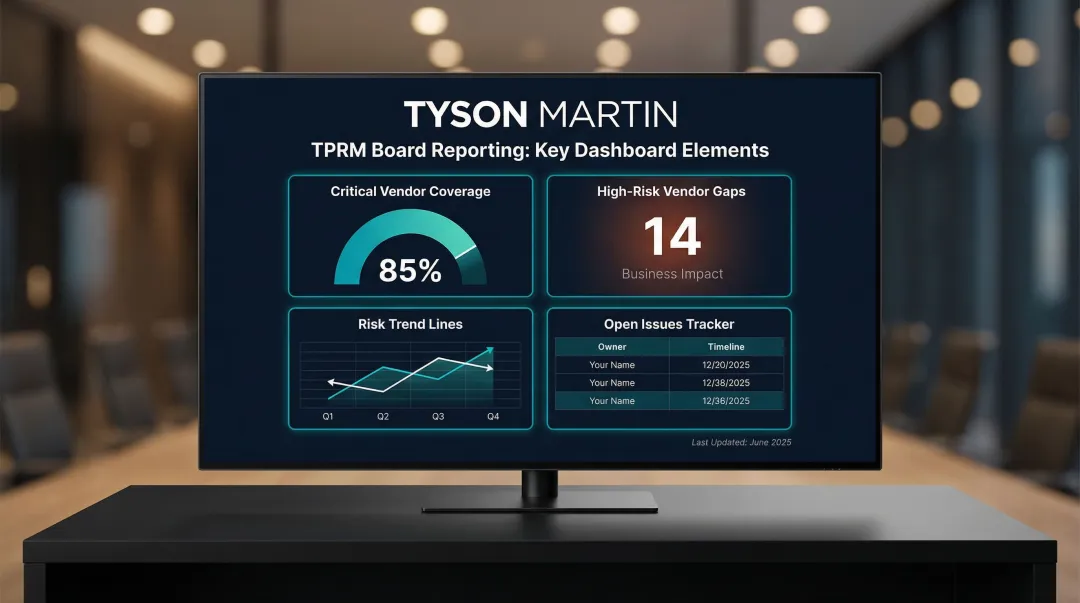
Use a Stable Dashboard With Trend Data
Boards need to see risk trajectory, not just a snapshot: which vendors moved from moderate to high risk, what was remediated, and what remains open. Research shows that only 40% of organizations regularly report to the board about TPRM program status, and 58% provide this information only if a security incident has occurred.
That reporting gap feeds a larger confidence problem: 90% of non-executive directors lack confidence in cybersecurity value, with only 10% expressing strong confidence in cybersecurity investments. Consistent, trend-based reporting is how CISOs close that gap.
Effective dashboard elements:
- Percentage of critical vendors with current risk assessments
- Number of high-risk vendor gaps and their business impact
- Trend lines showing risk reduction or emergence over time
- Clear owners and remediation timelines for open issues
Define Escalation Thresholds Explicitly
Establish in advance what level of vendor risk change requires an emergency board notification versus a standard quarterly update. Clear decision rights prevent both under-reporting of serious issues and over-burdening the board with noise.
Example escalation thresholds:
- Emergency notification (same day): Vendor breach affecting customer data, vendor failure halting critical operations, regulatory action against a critical vendor
- Immediate CISO review (within 48 hours): Vendor acquisition or merger, security incident in a vendor's sector, failed audit or assessment, contractual non-compliance
- Scheduled quarterly update: Routine risk tier changes, completed remediations, new vendor onboarding volume
Build an Audit-Ready Evidence Trail
Document every vendor review, remediation action, and waiver decision. This protects both the CISO and the board if a regulatory inquiry or post-incident review follows.
Maintain records of:
- Initial risk assessments and scoring rationale
- Re-assessment triggers and results
- Remediation plans, owners, and completion dates
- Risk acceptance or waiver decisions with executive approval
- Vendor incident notifications and response actions
Common Mistakes CISOs Make in Third-Party Risk Management
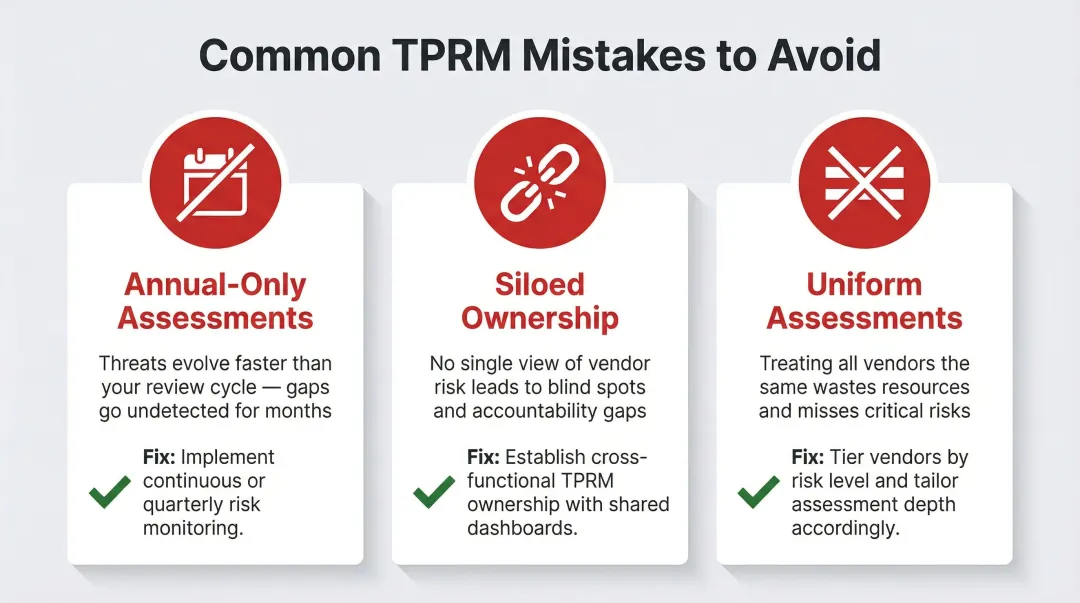
Treating TPRM as an Annual Compliance Event
Point-in-time assessments create a false sense of security given how rapidly vendor risk posture changes. 45% of organizations receive updates on vendor risk changes only yearly or never. Yet despite 83% of organizations considering their TPRM programs established, they still average 12 third-party breaches or security incidents per year.
Lacking Cross-Functional Ownership
When TPRM sits only in IT or security, procurement onboards vendors without review, legal signs contracts without security clauses, and finance maintains relationships with vendors that have failed assessments. CISOs need to establish governance structures where security, procurement, legal, and finance coordinate vendor decisions through defined approval gates.
Applying a One-Size-Fits-All Assessment
Comprehensive questionnaires sent to every vendor regardless of risk tier create volume without insight. Assessment depth should match vendor criticality:
- Critical vendors: Deep reviews covering controls, incident response, business continuity, and access management
- Low-risk vendors: Streamlined checks focused on basic security hygiene and contractual compliance
Frequently Asked Questions
What is third-party risk management in cybersecurity?
TPRM is the process of identifying, assessing, and continuously monitoring risks introduced by external vendors, suppliers, and service providers who have access to an organization's systems, data, or operations. It has become a core CISO function as supply chain attacks grow more frequent and costly.
What is the role of the CISO in risk management?
The CISO defines risk appetite, establishes governance structures, and communicates risk posture to the board in terms executives can act on. In TPRM specifically, the CISO owns vendor oversight and carries accountability when vendor-related incidents occur.
What is the difference between third-party and fourth-party risk?
Third-party risk comes from direct vendors with whom your organization has contracts. Fourth-party risk arises from those vendors' own suppliers and subcontractors. Organizations are often exposed to fourth-party risks without knowing it, which is why requiring vendors to disclose and manage their own TPRM practices is essential.
How often should CISOs conduct vendor risk assessments?
Assessment frequency should be risk-tiered: critical vendors may require quarterly reviews and continuous monitoring, while lower-risk vendors may need annual assessments. Any significant change in a vendor's environment—such as a breach, acquisition, or regulatory action—should trigger an immediate reassessment regardless of schedule.
What frameworks should CISOs use for TPRM?
Key frameworks include NIST SP 800-161 (supply chain risk), ISO 27001, the Shared Assessments TPRM Framework, and NIST CSF 2.0. Choose based on your regulatory environment, vendor complexity, and existing GRC infrastructure.
How should a CISO report third-party risk to the board?
Board reporting should frame vendor risk in business impact terms—operational exposure, regulatory liability, and trend direction—using a stable dashboard that shows trajectory rather than point-in-time scores. Pre-define escalation thresholds clearly so both the board and management know what triggers emergency notification versus a standard quarterly update.