Introduction
Public companies now face a structural governance problem: boards and audit committees must treat cybersecurity as a reportable compliance obligation, not an IT maintenance item. Since December 2023, the SEC has required companies to file Form 8-K disclosures within four business days of determining a cybersecurity incident is material.
Annual 10-K filings must now detail cyber risk management processes, board oversight structures, and management's role in assessing threats — all subject to federal securities law.
Yet many boards still treat these requirements as technicalities rather than governance imperatives. The SEC's enforcement record tells a different story. Six companies have paid penalties ranging from $990,000 to $4 million for minimizing known intrusions, treating realized incidents as hypothetical risks, or omitting material facts about breach scope.
Even as the current administration narrows enforcement to "fraudulent disclosure," the rules remain fully binding. State regulators, plaintiffs' attorneys, and the Division of Corporation Finance continue to scrutinize what companies file.
This article explains what the SEC's 2023 cybersecurity disclosure rules require, how the materiality determination clock actually works, what boards must document to demonstrate active oversight, and what the enforcement record reveals about how companies fail.
TLDR
- SEC rules require Form 8-K filing within four business days of a materiality determination, with annual 10-K disclosures covering risk management and governance
- "Material" has no dollar threshold — operational impact, reputational harm, and qualitative factors all count
- Enforcement penalties ($990K–$4M) have targeted vague disclosures, minimizing known breaches, and framing realized incidents as hypothetical
- The Trump administration narrowed enforcement focus to "fraudulent disclosure," but disclosure obligations remain unchanged and enforceable
- Boards are directly in scope: the SEC expects documented oversight, clear decision rights, and defined escalation processes
What the 2023 SEC Cybersecurity Rules Actually Require
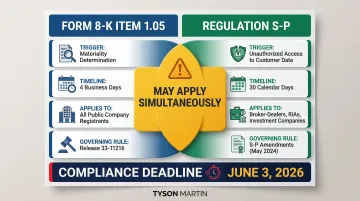
The SEC adopted Release No. 33-11216 on July 26, 2023, creating mandatory cybersecurity incident and governance disclosure requirements for all Exchange Act reporting companies. The rule became effective September 5, 2023, and compliance deadlines are now fully active: Form 8-K Item 1.05 took effect December 18, 2023 for most companies and June 15, 2024 for smaller reporting companies.
Two primary obligations:
- Form 8-K Item 1.05 — material cybersecurity incident disclosure within four business days of materiality determination
- Regulation S-K Item 106 — annual Form 10-K disclosure covering cyber risk management strategy, processes, and governance
Who is covered:
The rules apply to all public companies subject to Securities Exchange Act reporting requirements:
- Domestic registrants
- Foreign private issuers (via Forms 6-K and 20-F)
- Smaller reporting companies
- Emerging growth companies
What must be disclosed in Form 8-K:
Companies must describe (1) the material aspects of the incident's nature, scope, and timing; and (2) the material impact or reasonably likely material impact on financial condition and operations. The SEC does not require disclosure of technical details that would impede response or remediation.
Two important carve-outs shape how companies approach these timelines in practice.
National security delay carve-out:
The U.S. Attorney General may authorize disclosure delays if immediate filing poses substantial risk to national security or public safety. Maximum delay periods:
- Initial delay: 30 days
- First extension: additional 30 days
- Final extension (extraordinary circumstances): additional 60 days
- Total maximum: 120 days
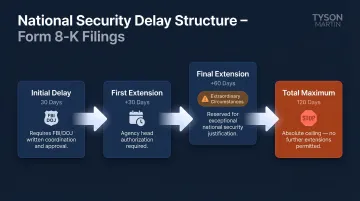
This is a narrow exception. It requires active coordination with the FBI and DOJ, and companies should not treat it as a default buffer for difficult disclosures.
Third-party and cloud incidents are covered:
Where an incident originates does not determine whether disclosure is required — impact does. The SEC made clear that incidents occurring through third-party service providers or cloud environments still require an 8-K filing if the impact on the registrant is material.
The Four-Day Clock: How Materiality Determinations Work in Practice
The four-business-day filing deadline starts on the date the company determines the incident is material—not the date of discovery, occurrence, or remediation. Erik Gerding, Director of the Division of Corporation Finance, confirmed this in December 2023: "The clock begins only after the company determines an incident is material."
The Materiality Standard
The SEC applies the traditional Supreme Court standard from TSC Industries (1976), Basic Inc. v. Levinson (1988), and Matrixx Initiatives (2011): information is material if there is a "substantial likelihood that a reasonable shareholder would consider it important" in making an investment decision.
Materiality is not limited to financial loss. Gerding's May 2024 statement clarified that companies must assess qualitative factors:
- Reputational harm
- Impact on customer or vendor relationships
- Competitive position damage
- Likelihood of litigation or regulatory investigations
- Operational disruption
The "Without Unreasonable Delay" Requirement
While the SEC has not defined a specific number of days, it requires that materiality determinations be made "without unreasonable delay" following discovery. The SEC has flagged practices that constitute unreasonable delay:
- Intentionally postponing committee meetings to avoid triggering the clock
- Extending internal reporting deadlines mid-incident
- Changing escalation criteria after discovery
Legal, finance, IT, and cybersecurity must be involved in materiality assessment from the start — not sequentially. Cross-functional readiness before an incident is what separates a defensible timeline from a flagged one.
Aggregation Risk
The "without unreasonable delay" requirement applies to individual incidents, but a separate exposure point involves patterns across incidents. A series of individually immaterial events from the same threat actor or exploiting the same vulnerability may collectively become material. Companies need processes to track and reassess related incidents over time — evaluating each event in isolation is not sufficient.

Item 1.05 vs. Item 8.01
If a company chooses to disclose an incident before completing a materiality determination — or concludes the incident is not material but still wants to inform investors — it should file under Item 8.01. Item 1.05 is reserved strictly for incidents the company has determined to be material. Filing under the wrong item invites SEC staff scrutiny and signals to investors that internal processes may not be well-defined.
Board Oversight and the Annual 10-K: What Must Be Documented
Regulation S-K Item 106 requires three categories of annual disclosure in Form 10-K:
Risk Management and Strategy (Item 106(b))
Companies must describe:
- Processes for assessing, identifying, and managing material cybersecurity risks
- How those processes integrate into overall enterprise risk management
- Whether the company engages third-party assessors or auditors
- Whether prior incidents have materially affected or are reasonably likely to materially affect business strategy, operations, or financial condition
Board-Level Governance (Item 106(c)(1))
Companies must identify:
- Which board committee oversees cybersecurity risk
- How the board or committee is informed about cyber threats and incidents
- Evidence of active oversight, not passive reception of updates
The SEC removed the proposed requirement to disclose individual board members' cybersecurity expertise, but expects boards to demonstrate substantive engagement—documented decision-making, not checkbox briefings.
Management-Level Governance (Item 106(c)(2))
Companies must describe:
- Who within management is responsible for assessing and managing cyber risk
- That person's relevant experience
- How they monitor incidents
- How they report to the board or relevant committee
This places the CISO (or equivalent role) directly in the SEC disclosure framework for the first time.
The Board's Documentation Dilemma
Boards face a tension: disclosures must give investors enough information to evaluate the company's cyber posture without creating a roadmap for attackers. Working with securities counsel to strike that balance is essential — and boards in transition face compounded risk because governance structures may be unclear or untested at exactly the moment disclosure scrutiny is highest. Transition scenarios that create particular exposure include:
- New leadership inheriting undocumented oversight processes
- M&A activity where cybersecurity governance spans two distinct frameworks
- Post-incident recovery, when prior decisions are subject to retroactive review
A board advisor or fractional CISO with SEC disclosure experience can help structure the oversight processes, escalation thresholds, and decision-rights frameworks the SEC expects to see documented. When the next filing deadline is approaching and governance documentation doesn't yet exist, that's when the gap becomes a liability.
Key Enforcement Cases and What They Reveal
R.R. Donnelley & Sons Co. — $2.125 Million Penalty (June 2024)
The SEC penalized RRD for failures related to a 2021 ransomware attack that exfiltrated 70 GB of data affecting 29 clients. The violations:
- Failed to provide its managed security service provider with adequate alert prioritization schemes
- Failed to act on three escalated alerts identifying lateral movement and malware
- Overburdened internal cybersecurity staff
The SEC charged RRD under Section 13(b)(2)(B) of the Exchange Act, treating IT systems and networks as assets requiring sufficient internal controls. This established that cybersecurity control failures can trigger accounting controls violations.
That principle was immediately tested in court.
SolarWinds Corp. and CISO Timothy Brown — Case Dismissed (November 2025)
The SEC filed a federal securities fraud complaint — the first to name a sitting CISO individually — in October 2023 against SolarWinds and Timothy Brown. In July 2024, Judge Paul Engelmayer of the Southern District of New York dismissed most claims, ruling:
- "Accounting critically delimits the statute's reach"—cybersecurity controls fall outside Section 13(b)(2)(B)
- Risk factor disclosures were not materially misleading
- Public statements were "non-actionable corporate puffery"
The court sustained only fraud claims related to the company's public Security Statement. In November 2025, the SEC abandoned the remaining claims entirely.
Key implication: Individual CISO liability under novel accounting-controls theories is now substantially narrower. Accountability for knowingly false disclosures, however, remains intact and fully actionable.
Four SolarWinds-Linked Settlements — $6.985 Million Combined (October 2024)
Four companies paid penalties for minimizing known SolarWinds-related intrusions in subsequent SEC filings:
| Company | Penalty | Violation |
|---|---|---|
| Unisys Corp. | $4,000,000 | Described known intrusions as "hypothetical" despite gigabytes exfiltrated |
| Avaya Holdings Corp. | $1,000,000 | Claimed "limited number" of emails accessed; actually 145+ files in cloud sharing |
| Check Point Software | $995,000 | Described incidents in "generic terms" despite specific knowledge |
| Mimecast Limited | $990,000 | Failed to disclose nature of code exfiltrated and quantity of credentials accessed |
Common pattern: Each company made materially misleading disclosures by minimizing realized risks or framing known incidents as hypothetical future possibilities. All four were pursued under pre-2023 rules — which means companies now operating under the 2023 mandatory disclosure framework face the same scrutiny with tighter timelines and fewer ambiguities to hide behind.

How Enforcement Priorities Are Shifting in 2025 and 2026
The Trump Administration's Narrower Enforcement Focus
In February 2025, Acting Chairman Mark Uyeda announced the creation of the Cyber and Emerging Technologies Unit (CETU), replacing the Crypto Assets and Cyber Unit. The unit's stated priorities include "public issuer fraudulent disclosures regarding cybersecurity" and "regulated entities' cybersecurity compliance," with emphasis on deploying "enforcement resources judiciously."
In April 2026, the SEC announced FY2025 results: 456 enforcement actions filed, with Chairman Atkins stating the Commission "put a stop to regulation by enforcement and recentered its enforcement program on the Commission's core mission."
What this means: Enforcement has shifted from penalizing disclosure deficiencies broadly to concentrating on fraudulent disclosure. The bar has moved from "insufficient" to "knowingly false." But the rules remain fully binding.
14 Proposed Cyber Rules Withdrawn (June 2025)
On June 12, 2025, the SEC withdrew 14 proposed rules issued between March 2022 and November 2023, including:
- Cybersecurity Risk Management for Investment Advisers and Registered Investment Companies
- Cybersecurity Risk Management Rule for Broker-Dealers and Clearing Agencies
Critical clarification: The 2023 public-company cybersecurity disclosure rules (Release 33-11216) were not among the withdrawn proposals. Those rules remain fully effective and enforceable.
Regulation S-P Amendments — June 3, 2026 Compliance Deadline
The SEC adopted Regulation S-P amendments in May 2024, requiring broker-dealers, registered investment advisers, and investment companies to:
- Provide notice to affected individuals within 30 days of unauthorized access to sensitive customer information
- Implement expanded safeguards for customer information
- Strengthen service provider oversight obligations
Compliance deadlines by entity size:
| Entity Type | Deadline |
|---|---|
| Larger entities | December 3, 2025 |
| Smaller entities | June 3, 2026 |
Financial services firms now face two overlapping notification obligations — the 4-business-day materiality clock under the 2023 disclosure rules and Reg S-P's 30-day customer notification requirement — each with its own triggers, timelines, and compliance infrastructure.
AT&T Comment Letter: What the SEC Expects in Item 1.05 Filings
In July 2024, the Division of Corporation Finance sent a comment letter to AT&T regarding its Form 8-K Item 1.05 filing, challenging the qualitative completeness of its disclosure. The SEC asked AT&T to clarify whether the incident — exfiltration of call and text records of nearly all wireless customers — was determined material and why the filing did not describe qualitative impacts such as reputational harm and customer relationship effects.
The practical implication for disclosure counsel and CISOs: an Item 1.05 filing that quantifies financial exposure but omits reputational, operational, or customer-facing consequences will draw SEC scrutiny. Boards should expect staff to probe the reasoning behind materiality determinations, not just accept them.
What Boards and Executive Teams Should Do Right Now
Audit Disclosure Controls Against Item 1.05 Requirements
Boards should verify:
- Does the company have a documented process to escalate potential cyber incidents to a cross-functional materiality assessment team?
- Are decision rights, escalation thresholds, and timelines clearly defined in writing?
- Have those processes been tested in tabletop exercises before an incident occurs?
The four-day clock starts at materiality determination, not discovery—which means the escalation and assessment process must function under pressure without adding unreasonable delay.
Review Form 10-K Cybersecurity Disclosures Against Enforcement Patterns
With enforcement patterns now established, compare your most recent Form 10-K Item 106 disclosures against what the SEC has actually penalized:
- Vague language treating known risks as hypothetical
- Omitting material facts about scope or impact of previous incidents
- Inconsistency between what management knows and what is disclosed
- Generic boilerplate that does not describe actual processes or governance structures
The Division of Corporation Finance has issued staff guidance emphasizing that qualitative factors—reputation, competitiveness, customer relationships, litigation risk—must be considered in materiality assessments and reflected in disclosures where relevant.
Address Governance Gaps in Transition Scenarios
Once disclosures are tightened, governance gaps become the next exposure point—particularly for organizations in transition. Common risk concentrations include:
- New leadership may not know where decision rights sit
- M&A activity creates unclear reporting lines
- Post-incident recovery often reveals governance processes were never documented
A fractional CISO or board advisor with SEC disclosure experience can step in to establish:
- Defensible oversight processes
- Clear escalation thresholds and decision-rights frameworks
- A 90-day compliance plan with measurable outcomes and assigned owners
- Board-ready reporting templates that satisfy Item 106 requirements

The disclosures follow from the governance. Get the structures right, and accurate reporting becomes an output, not an exercise.
Frequently Asked Questions
What are the new SEC cybersecurity disclosure requirements?
The 2023 SEC rules require public companies to file a Form 8-K within four business days of determining a cybersecurity incident is material, and to include annual disclosures in Form 10-K covering their cyber risk management processes, board oversight structure, and management's role in assessing cyber risk.
What is an 8-K filing with the SEC?
Form 8-K is a current report that public companies must file with the SEC to notify investors of significant events that may affect their investment decisions. The 2023 cybersecurity rules added Item 1.05, which specifically governs how and when material cybersecurity incidents must be reported to investors.
How does the SEC define a "material" cybersecurity incident?
The SEC applies the same materiality standard as other disclosures—an incident is material if a reasonable investor would consider it important in making an investment decision. The SEC weighs both quantitative factors (financial impact) and qualitative factors (reputational harm, operational disruption, customer data exposure) — no dollar threshold triggers automatic materiality.
Do the SEC cybersecurity disclosure rules apply to private companies?
The 2023 rules apply to public companies subject to the Securities Exchange Act of 1934 reporting requirements, including domestic registrants and foreign private issuers. Private companies face no equivalent Form 8-K or 10-K filing obligations under these rules.
What must a company disclose in its annual Form 10-K about cybersecurity?
Companies must describe their processes for assessing and managing material cybersecurity risks, the board's oversight role and which committee (if any) is responsible, and management's role and relevant expertise in assessing and managing those risks under Regulation S-K Item 106.