Introduction
Technology and cyber risk don't pause for deal timelines. Traditional advisors focus on valuation, deal structure, and regulatory filings — while the systems, data liabilities, and security gaps that determine real deal value after close receive no scrutiny at all. By the time integration begins, the exposure has already transferred.
The pain is specific: boards are approving billion-dollar transactions with incomplete visibility into inherited infrastructure debt, open compliance gaps, and cyber exposure that transfers the moment the deal closes. Strategic technology advisory exists to close that gap — before the ink dries, not after the damage surfaces.
TLDR
- Technology and cyber risk in financial services M&A requires specialized assessment that traditional deal advisors are not equipped to provide
- Inherited breaches, compliance gaps, and technical debt can materially reduce deal value or create post-close liability
- Technology advisory—spanning assessment, due diligence, and integration—is a deal requirement, not an optional workstream
- Boards need independent, plain-language visibility into technology risk before a transaction closes
Why Financial Services M&A Requires Specialized Technology Advisory
Financial services is the most heavily regulated and most aggressively targeted industry for cyber attacks. Both realities become structural problems the moment two organizations merge.
The numbers are clear:
- Finance was the most breached industry in 2023, accounting for 27% of all breaches, up from 19% in 2022
- FinCEN reports 432 ransomware incidents in financial services from 2022-2024, totaling approximately $365.6 million in payments—the highest dollar-value impact of any industry
- Average breach costs in finance reached $6.08 million—22% higher than the global average

Investment bankers optimize for deal structure and valuation. That mandate doesn't cover:
- Security operations maturity at the target firm
- Data governance posture and residency compliance
- The cost of inheriting infrastructure 18 months behind on critical patches
The M&A Vulnerability Window
M&A creates a defined period of organizational vulnerability:
- Governance decision rights are unclear
- IT teams are uncertain about reporting lines
- Security monitoring fragments across two environments simultaneously
The FBI issued a formal warning that ransomware actors specifically target companies during merger negotiations. Three publicly traded companies were attacked while actively in M&A talks. Attackers researched publicly available information to identify time-sensitive financial events, then used that pressure to maximize ransom demands.
Financial services firms are high-value targets during this window. Whether the board has a credible answer to that risk before signing is what separates a manageable integration from an inherited crisis.
Recognizing What Traditional Advisors Miss
Standard due diligence checks financial statements, contracts, regulatory filings, and litigation exposure. It lacks the technical depth to evaluate:
- Whether the target has defensible cybersecurity controls
- Unresolved regulatory enforcement actions tied to IT systems
- Systemic gaps in data residency and privacy compliance
Even the largest advisory firms now acknowledge this gap. Deloitte operates a formal IT M&A Practice analyzing technology components with material impact on deal value, including cybersecurity posture and digital footprint analysis as distinct workstreams.
For deal teams without that capability in-house, the gap doesn't close on its own — it surfaces in post-close remediation costs, regulatory scrutiny, and integration delays.
The Technology and Cyber Risks That Transfer With Every Acquisition
Inherited Technical Debt
Legacy systems are the most common and underestimated risk in financial services M&A:
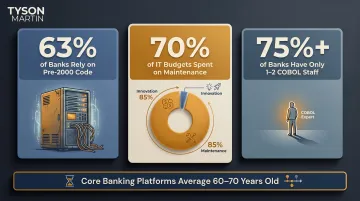
- 63% of banks still rely on code written before 2000
- 70% of bank IT budgets are spent maintaining legacy systems, not innovating
- More than 75% of banks have only 1-2 COBOL-skilled staff—creating a single point of failure
Core banking platforms at many institutions are 60 to 70 years old. When you acquire these systems, you inherit fragmented cloud environments, unpatched infrastructure, and outdated identity management. What holds it together is institutional knowledge—and that knowledge leaves during post-close attrition.
Compliance Gaps Transfer Immediately
Unresolved compliance gaps formally transfer the moment the deal closes:
- Open regulatory findings
- Consent orders
- Pending examinations
- Data governance deficiencies under GLBA, PCI DSS, or state privacy regulations
You don't just inherit the revenue. You inherit the risk register.
Undisclosed Breaches Reduce Deal Value
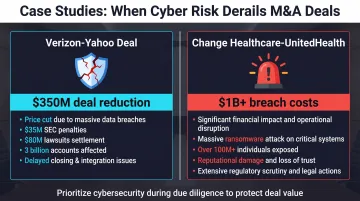
Case Study: Yahoo/Verizon (2016-2017)
Verizon reduced its acquisition price for Yahoo by $350 million—from $4.83 billion to $4.48 billion—after two massive breaches were disclosed:
- Breach #1: At least 500 million accounts compromised in late 2014; disclosed September 2016
- Breach #2: More than 1 billion accounts compromised in August 2013; disclosed December 2016
The deal didn't collapse, but Verizon negotiated a 50/50 liability split for government investigations and third-party lawsuits.
Case Study: Marriott/Starwood (2016-2024)
Marriott paid a $52 million multi-state settlement in 2024 for a breach inherited through its 2016 Starwood acquisition. The breach originated in 2014—two years before Marriott's acquisition—but wasn't discovered until November 2018. Up to 500 million guests were affected.
Vendor relationships compound this exposure further.
Third-Party and Vendor Risk Exposure
Financial services firms operate within dense ecosystems:
- Payment processors
- Core banking vendors
- Cloud providers
- Data aggregators
When you acquire a financial services firm, you inherit all third-party relationships—and their risk profiles. A target's vendor due diligence program (or absence of one) is a material risk factor.
The Financial Stability Board's Third-Party Risk Toolkit highlights systemic concentration risk: a small number of providers serve a vast portion of the financial sector, creating risks that extend to "N-th party" subcontractors with limited visibility.
Security Culture Mismatch
Acquirers often discover post-close that the target operated with:
- Minimal security governance
- No formal risk escalation process
- No board-level cyber reporting cadence
Technology integration timelines are rarely the constraint. Governance gaps and undocumented risk tolerances are what stall post-close execution and expose acquirers to incidents they had no framework to prevent.
The Strategic Advisory Framework: From Due Diligence to Integration
Strategic technology advisory begins before a term sheet is signed: independent pre-deal assessment of the target, conducted by advisors separate from the deal team. This produces a clear, risk-adjusted view of what's being acquired—including remediation costs, regulatory exposure, and realistic integration timelines.
Before the Deal Closes
Structured technology due diligence includes:
- Mapping decision rights and governance structures at the target
- Identifying open regulatory and compliance obligations tied to technology
- Assessing incident history and breach disclosure posture
- Evaluating security operations and vendor management maturity
This work should produce board-level documentation—not a technical report only engineers can interpret. Directors need to understand three things from that documentation:
- What the known technology risks are
- What remediation costs and timelines look like
- What the first 90 days post-close must address
Tyson Martin structures this reporting to show trend, not trivia—giving boards the stable, plain-language view they need to make defensible decisions and carry that clarity into the integration phase.
From Signing to Integration
Integration is the most operationally demanding phase:
- Establishing unified identity and access management
- Rationalizing security tooling
- Consolidating vendor contracts
- Harmonizing compliance programs
- Establishing clear governance and escalation structures

Integration is where most post-merger cyber incidents occur.
Organizations navigating M&A often benefit from interim or fractional executive support—a fractional CISO, CIO, or Chief Digital Officer who provides stability, leads integration workstreams, and serves as a credible point of contact for regulators during transition.
Tyson Martin steps into that role directly: providing interim or fractional executive coverage that keeps integration workstreams moving, maintains regulator confidence, and ensures the combined entity has clear technology leadership from day one.
Regulatory Dimensions That Can Make or Break a Deal
Financial services M&A is subject to review from multiple regulators depending on the institutions involved:
- Office of the Comptroller of the Currency (OCC)
- Federal Deposit Insurance Corporation (FDIC)
- Federal Reserve
- Securities and Exchange Commission (SEC)
- Consumer Financial Protection Bureau (CFPB)
- State banking regulators
Recent example: The OCC conditionally approved Capital One's merger with Discover Bank (resulting entity: approximately $660 billion in assets). Approval required Capital One to provide "approved plans detailing effective and sustainable corrective actions" to address outstanding enforcement actions against Discover Bank—including IT controls and data security.
Data Governance and Privacy Obligations Don't Pause
GLBA, state privacy laws, and international equivalents apply throughout the transaction:
- Acquirers must assess whether the target's data handling practices are defensible
- Consent frameworks must align
- Cross-border data transfer mechanisms must be validated
- Plans must exist to bring them into alignment post-close
Data governance gaps don't stay contained — they can trigger public disclosure obligations before the ink is dry.
SEC Cyber Incident Disclosure Requirements
The SEC cybersecurity rule adopted July 26, 2023 imposes strict timelines that don't pause for deal activity:
- 4 business days to file an 8-K after determining an incident is material
- No general exemption for incidents at acquired entities
- Material incidents discovered during or after close may require immediate disclosure
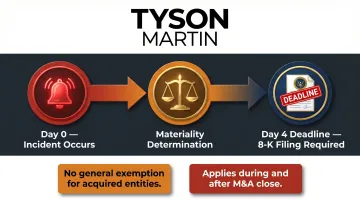
The acquirer's ability to make accurate, timely disclosures depends entirely on visibility into the target's security posture. Without pre-close diligence, that visibility often doesn't exist when it's needed most.
How Boards Should Structure Oversight During a Financial Services Transaction
Boards are not operators, but they are accountable for ensuring management has:
- The right advisors
- The right process
- The right reporting structure to evaluate technology risk
Boards should ask whether an independent technology and cyber advisory voice is part of the transaction team—separate from the investment banker and legal counsel.
Clear Decision Rights Are Critical
M&A governance failures often begin with unclear decision rights. When it's unclear who owns technology risk assessment, who escalates issues to the board, and who is accountable for integration outcomes, the default is that everyone assumes someone else is handling it.
Boards should require:
- Clear decision rights and escalation thresholds defined before the deal progresses past a specific milestone
- Documentation of who owns what
Post-Close Risk Updates
Audit and risk committees should request a post-close technology risk update at a defined interval—typically 90 days—that documents:
- What was discovered
- What remediation is underway
- Whether risk assumptions made during due diligence were accurate
This creates a governance record and ensures the board remains engaged beyond deal close.
Governance Principles for Cyber Oversight
That post-close discipline needs to rest on a coherent governance framework, not improvised checklists. The NACD Director's Handbook on Cyber-Risk Oversight outlines six core principles, starting with treating cybersecurity as a strategic enterprise-wide risk, not an IT issue.
Principle 3—oversight structures and expertise—is directly applicable during transactions. Boards should confirm before deal close that they have access to an independent cybersecurity voice capable of evaluating target company risk, not just ratifying management's assessment:
- Independent advisory access: A cybersecurity expert who reports to the board, not through the deal team
- Defined escalation triggers: Specific thresholds that automatically surface risk findings to the audit or risk committee
- Expertise continuity: The same advisor involved in pre-close diligence should be available to validate post-close findings against original assumptions
Frequently Asked Questions
What makes financial services M&A different from other industries when it comes to technology risk?
Financial services faces dense regulatory oversight, high data sensitivity, complex vendor ecosystems, and disproportionate targeting by threat actors. Technology and cyber risk in a financial services deal is both higher-stakes and more complex to evaluate than in most other sectors.
What should a board ask about cybersecurity before approving an acquisition?
Four essential questions: Has an independent cyber posture assessment been conducted? Are there known regulatory findings or compliance gaps that will transfer? What is the estimated cost to remediate? What does the 90-day post-close technology governance plan look like?
How can inherited cyber debt affect deal valuation in financial services acquisitions?
Unresolved technical debt, open regulatory findings, and undisclosed breach history create three distinct risks: purchase price adjustments that reduce deal value, unmodeled post-close remediation costs, and regulatory liability that surfaces after close. Each can be mitigated through structured due diligence before signing.
What is the role of a fractional or interim CISO during an M&A transaction?
A fractional CISO provides independent technology leadership—conducting or overseeing due diligence, translating findings for the board, and leading integration workstreams—without requiring a permanent executive hire. For organizations under deal timelines, this structure delivers senior judgment at speed, without the 90-day lag of a full executive search.
What regulatory agencies scrutinize technology governance in financial services M&A?
Primary regulators include the OCC, FDIC, Federal Reserve, SEC, CFPB, and applicable state regulators. Each may impose technology-specific conditions as part of merger approval. Since 2023, several of these agencies have issued updated guidance tying merger approval timelines directly to cyber governance posture.