Introduction
Boards navigating cross-border M&A face intense pressure to move quickly, yet cyber vulnerabilities hidden in acquisition targets can materially erode deal value and trigger regulatory penalties across multiple jurisdictions. The Verizon-Yahoo transaction makes this concrete: undisclosed breaches affecting more than 1 billion user accounts led to a $350 million price reduction and a $35 million SEC penalty.
The Marriott-Starwood deal shows the compounding risk when acquirers inherit breaches they never detected. A 2014 intrusion on Starwood systems went unnoticed through the 2016 close, ultimately producing £18.4 million in ICO fines, a $52 million U.S. state settlement, and 20 years of FTC oversight.
In cross-border deals, cyber risk spans data protection law compliance, third-party exposure, geopolitical threats, and post-close integration complexity. Selecting the right advisory firm is a board-level decision with direct valuation implications.
TLDR
- Cross-border M&A introduces risks domestic deals don't: multi-jurisdiction compliance, uneven security maturity, and an attack surface that grows with every new entity added
- Undisclosed breaches reduce valuations, trigger fines, and create liabilities that outlast the transaction
- The strongest advisors pair deep cybersecurity expertise with cross-border regulatory knowledge — and convert technical findings into decisions boards can act on
- Choose based on deal complexity, geography, and whether you need governance support that extends past closing
Why Cross-Border M&A Amplifies Cyber Risk
Cross-border deals trigger simultaneous compliance obligations across multiple jurisdictions — often all at once. A single transaction can activate exposure across several regulatory regimes:
- GDPR: Fines up to €20 million or 4% of global turnover
- NIS2: Penalties of €10 million or 2% of turnover for essential entities
- DORA: 1% of average daily worldwide turnover for ICT providers
- CCPA: $7,500 per intentional violation
- HIPAA: Layered obligations when health data is involved

Each jurisdiction adds compounding exposure that domestic-only diligence frameworks miss entirely.
Acquired entities expand the attack surface immediately. Targets often bring incompatible security architectures, undisclosed vendor relationships, OT/IT convergence risks common in industrial deals, and legacy technical debt. According to IBM's 2024 Cost of a Data Breach report, breaches involving third-party business partners averaged $4.99 million and required 294 days to identify and contain — well beyond typical M&A integration timelines.
Cross-border transactions also face distinct geopolitical threats. Mandiant identified APT group UNC3524 specifically targeting M&A-related emails, maintaining access for up to 18 months — with TTPs overlapping Russian cyber-espionage groups APT28 and APT29.
Criminal operators work the same angle from a different direction. The FBI issued a November 2021 warning that DarkSide, REvil, and LockBit ransomware operators deliberately target companies during M&A to exploit deal-closing pressure. Advisors without active threat intelligence integration have no framework for surfacing these risks during diligence.
Leading Advisory Firms for Cross-Border M&A Cyber Risk
The firms below demonstrate proven ability to deliver actionable cyber risk assessments at the board level, with cross-border deal experience, multi-jurisdiction compliance coverage, and capacity to integrate findings into deal structure and valuation decisions.
Deloitte
Deloitte operates across 150+ countries with a dedicated M&A cybersecurity advisory practice that integrates cyber diligence alongside financial, operational, IT, and HR reviews within unified deal processes. What sets it apart: simultaneous pre-deal threat assessment, regulatory compliance review across jurisdictions, and post-close integration security planning — making it particularly strong for large-cap or highly regulated transactions.
Deloitte's cyber due diligence framework evaluates security governance, open-source software usage, cloud security, intellectual property protection, cyber resilience, HR-related risks, and compliance with GDPR, CCPA, and PCI DSS. Findings flow directly to Business Steering Committees and inform deal valuation and SPA conditions.
| Attribute | Detail |
|---|---|
| Focus Area | Pre-deal cyber risk assessment, regulatory compliance (GDPR, CCPA, sector-specific), integration security planning |
| Ideal Deal Profile | Large-cap, highly regulated, multi-jurisdiction cross-border acquisitions |
| Distinguishing Capability | Single-firm integration of cyber findings with financial, operational, and legal diligence streams |
KPMG
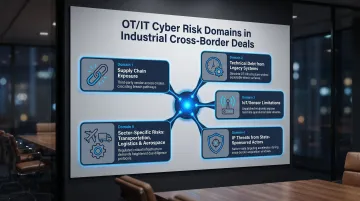
KPMG's global advisory network operates in 143 countries and maintains a dedicated M&A Technology Center of Excellence. Its strength centers on industrial manufacturing and OT/IT convergence challenges, addressing five specific risk domains: supply chain exposure from interconnected partners, technical debt from legacy systems, IoT/sensor limitations, intellectual property threats from state-sponsored actors, and sector-specific risks in transportation, logistics, and aerospace.
KPMG embeds cyber diligence throughout transaction timelines, deploys compromise assessments to detect hidden threats, and forms transaction-specific cybersecurity teams. This makes it a preferred choice for deals involving industrial, manufacturing, or infrastructure targets in complex geographies.
| Attribute | Detail |
|---|---|
| Focus Area | OT/IT convergence risk, supply chain cyber exposure, technical debt assessment, smart manufacturing M&A |
| Ideal Deal Profile | Industrial, manufacturing, energy, or infrastructure cross-border acquisitions |
| Distinguishing Capability | Deep OT/ICS cybersecurity expertise combined with global regulatory intelligence |
EY (Ernst & Young)
EY's transaction-focused cybersecurity practice operates through EY-Parthenon's strategy and transactions group, led by specialists including a former FBI Special Agent and former DOJ cybercrime prosecutor. EY links cyber findings directly to deal strategy, valuation framing, and buyer positioning.
EY goes beyond vulnerability identification to assess how cyber risk affects competitive positioning, regulatory trajectory, and post-deal value creation. This approach resonates with buyers focused on growth theses rather than pure risk mitigation.
| Attribute | Detail |
|---|---|
| Focus Area | Cyber risk within deal strategy, threat landscape analysis, incident history review, regulatory compliance alignment |
| Ideal Deal Profile | Strategy-driven acquisitions where cyber posture affects market position or regulatory approval |
| Distinguishing Capability | Integration of cyber findings with commercial, operational, and regulatory diligence for unified deal view |
Kroll
Kroll unified its global risk intelligence capabilities (including former Duff & Phelps operations) under one brand in 2021, creating a firm of nearly 5,000 professionals across 30 countries serving 61% of Fortune 100 companies. Its investigative and forensic background delivers a unique lens for cross-border M&A cyber diligence.
Kroll excels at uncovering hidden risks standard diligence misses: undisclosed breaches, governance failures, state-sponsored threat exposure, and sensitive third-party relationships. Its three-tier assessment framework ranges from external digital footprint analysis to internal technology-facilitated threat hunting. This makes it particularly valuable for deals involving geopolitically sensitive geographies or targets with complex ownership structures.
| Attribute | Detail |
|---|---|
| Focus Area | Hidden breach identification, forensic investigation, governance and third-party risk, geopolitical threat analysis |
| Ideal Deal Profile | Deals with elevated risk profiles, sensitive counterparties, or geopolitically complex cross-border structures |
| Distinguishing Capability | Investigative and forensic methodology applied to cyber diligence, surfacing risks standard assessments overlook |
PwC
PwC operates a global network of 364,782 professionals across 136 countries, serving 82% of the Fortune Global 500. Its M&A deals practice connects cyber diligence directly to value creation planning, post-deal synergy realization, and regulatory compliance readiness.
PwC frames cyber risk findings as factors that affect deal value — not just liability items to flag and move on. This helps deal teams quantify how resolving cyber gaps accelerates integration, reduces regulatory exposure, and supports investor confidence. PwC collaborated with the World Economic Forum on Principles for Board Governance of Cyber Risk, which explicitly addresses M&A as requiring cyber-risk integration.
| Attribute | Detail |
|---|---|
| Focus Area | Cyber risk tied to value creation, post-close integration security, regulatory readiness, deal positioning |
| Ideal Deal Profile | Multinational deals where cyber posture directly influences investor confidence and post-close integration planning |
| Distinguishing Capability | Links cyber findings to strategic and operational value drivers, enabling acquirers to price and plan around risk |
Fractional Board-Level Cyber Advisor (Tyson Martin)
For mid-market organizations, board committees navigating M&A without a dedicated CISO, or executive teams needing senior cyber risk judgment between transactions, a fractional board-level advisor provides targeted expertise without large firm engagement costs. This model proves especially effective when boards need clear oversight, defensible decision-making, and credible reporting rather than full diligence operations.
Tyson Martin draws on enterprise leadership experience at AWS, Home Depot, and Best Buy, plus active participation in the World Economic Forum Centre for Cybersecurity, NRF CISO Executive Committee, and NACD. He serves as a board advisor or interim/fractional CISO who clarifies decision rights, tightens governance, and builds cyber oversight that holds under pressure — including during M&A transitions.
| Attribute | Detail |
|---|---|
| Focus Area | Board-level cyber governance, decision rights clarity, credible risk reporting, M&A transition oversight |
| Ideal Deal Profile | Mid-market organizations, boards without a CISO, executive teams in M&A transition needing senior cyber judgment fast |
| Distinguishing Capability | Plain-English board reporting, stable risk dashboards, 90-day executable plans with measurable outcomes — reducing noise without reducing rigor |
What to Look for in a Cross-Border M&A Cyber Advisor
The most common mistake: treating cyber advisory as a late-stage compliance check. By the time a target's cyber posture is reviewed, deal terms may already be set — limiting the acquirer's ability to price risk, renegotiate, or walk away. Strong advisors enter early and shape how findings affect deal structure.
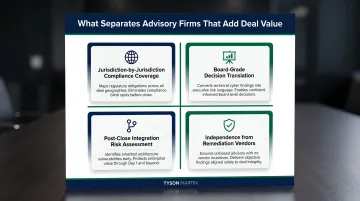
When evaluating a firm, four criteria separate advisors who add deal value from those who generate reports nobody acts on:
- Jurisdiction-by-jurisdiction compliance coverage. The firm should assess the target across every applicable framework — not just GDPR or CCPA, but HIPAA, DORA, NIS2, and CMMC where relevant. A Forescout survey found 53% of organizations encountered critical cybersecurity issues during M&A that jeopardized deals, and 65% experienced buyer's remorse post-close.
- Board-grade decision translation. Findings must answer three questions: Which risks affect deal value or close? What does each exposure cost? What contractual, structural, or remediation steps resolve them? Technical reports alone don't support board decisions.
- Post-close integration risk assessment. The advisor should evaluate how two security architectures, vendor ecosystems, and compliance frameworks interact after close — not just the target's current state. Integration risk is one of the most consistent sources of post-close breach.
- Independence from remediation vendors. Advisors with no financial stake in post-close tooling or IT work give cleaner assessments. In cross-border deals, the pressure to minimize findings and keep momentum is real. According to NACD's 2026 Cyber Risk Handbook, boards now have authoritative M&A-specific guidance to demand that cyber due diligence be integrated into deal governance from the start.
Conclusion
In cross-border M&A, cyber risk is a deal variable affecting valuation, regulatory approval, integration timelines, and investor confidence. The right advisor brings board-ready insight, cross-jurisdiction coverage, and decision-grade findings delivered before terms are finalized — not after close.
For boards and executive teams navigating M&A transitions, Tyson Martin is available as a fractional CISO, board advisor, or interim executive. His engagements deliver plain-English risk reporting, clear decision rights, a 90-day executable plan, and no vendor conflicts — built for decision-making, not documentation.
Reach him at tyson.martin@gmail.com or +1 (802) 430-9200.
Frequently Asked Questions
What makes cross-border M&A cyber risk different from domestic deal risk?
Cross-border deals layer multiple data protection regimes (GDPR, CCPA, sector-specific laws), divergent security maturity across geographies, and data sovereignty requirements onto a single transaction. Domestic diligence frameworks aren't built to catch that exposure — which is where post-close liability typically originates.
When in the M&A process should cybersecurity advisory begin?
Cyber advisory should begin alongside financial and legal diligence — ideally before LOI, or immediately after. Findings surfaced early can be reflected in deal price, representations and warranties, or deal structure; findings surfaced late rarely get the protection they warrant.
How does a target's cyber posture affect deal valuation in cross-border transactions?
Undisclosed breaches, regulatory non-compliance, or weak security controls reduce the acquirer's confidence in earnings sustainability and increase post-close remediation costs. Both factors can reduce enterprise value, trigger price renegotiation, or in serious cases lead to deal termination.
What are the 4 types of CTI?
The four types of Cyber Threat Intelligence (CTI) are:
- Strategic — high-level trends for executives and boards
- Tactical — TTPs (tactics, techniques, procedures) used by threat actors
- Operational — details about specific planned or active attacks
- Technical — indicators of compromise such as IPs, hashes, and malware signatures
For M&A purposes, EC-Council notes that strategic and operational CTI are most relevant when assessing threat landscapes around acquisition targets.
What should a board ask its M&A cyber advisor before a deal closes?
Four questions every board should put to its M&A cyber advisor before close:
- What risks could affect deal value or post-close operations?
- Are there undisclosed breaches or active compromises?
- What regulatory exposure does the target carry across all jurisdictions?
- What is the 90-day remediation priority after close?
Can a fractional CISO provide M&A cyber risk advisory?
Yes. A fractional CISO with enterprise M&A experience can deliver board-level cyber oversight, clarify decision rights, and provide credible risk reporting during a transaction — more efficiently than large firms for mid-market deals. The right fit combines cross-sector diligence experience, clear board communication, and a clean conflict-of-interest record.