Introduction
Cybersecurity gaps have become deal-breakers in M&A transactions. Nearly 1 in 4 executives experienced a cyber incident during or shortly after a transaction, with 42% reporting significant valuation reductions and 20% facing delays or pauses. Undisclosed vulnerabilities, inherited regulatory liabilities, and inadequate controls force renegotiations and trigger post-close losses — turning cyber due diligence into one of the highest-stakes steps in any deal process.
Those losses are now driving formal requirements. In 2026, M&A cyber risk assessment has moved from technical afterthought to board-level compliance obligation. SEC cybersecurity disclosure rules require acquirers to account for material cyber risks in filings within four business days of determining materiality. Cross-border regulations like GDPR — which can impose fines up to €20M or 4% of worldwide annual turnover — create liabilities that transfer directly with the deal.
The insurance market is adding its own pressure. Cyber insurers have tightened underwriting standards and are increasingly requiring documented due diligence outputs before covering combined post-close operations.
TLDR
- Cyber risk assessments expose inherited liabilities and compliance gaps that affect deal valuation and integration cost
- Top providers combine compliance frameworks with M&A workflows, not generic security testing
- Kroll, SecurityScorecard, Coalfire, Mandiant, and Deloitte Cyber Risk Services are the leading options for M&A contexts
- Prioritize M&A experience, regulatory alignment, board-ready reporting, and timeline flexibility when selecting a provider
- A fractional CISO can help define scope requirements and interpret findings for boards before negotiation
Cyber Risk Assessment and M&A Compliance: What's at Stake in 2026
A cyber risk assessment in an M&A context is a structured evaluation of a target company's security posture, data governance practices, third-party dependencies, and compliance obligations. It surfaces risks that could affect deal price, indemnification language, escrow calculations, or post-close integration cost — giving boards and legal counsel the technical findings they need to make defensible business decisions.
Regulatory pressure has made assessments non-negotiable in 2026. Three converging requirements are driving demand:
- SEC disclosure rules require public acquirers to account for material cyber risks in Form 8-K filings
- GDPR and state privacy laws — including California's AB 1824, which requires acquirers to honor prior opt-out requests and transfer privacy records — create data liability that transfers with ownership
- Cyber insurers now scrutinize combined post-close coverage and won't underwrite deals without target company assessments
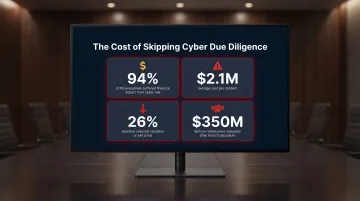
That regulatory exposure compounds the financial risk. Buyers who skip or rush assessments absorb technical debt, legal exposure, operational disruption, and reputational damage in a single transaction. Kroll's 2026 study of 325 PE executives found 94% suffered financial impact from cyber risk, averaging $2.1M per incident, with 26% reporting reduced valuation or exit price. The high-profile 2017 Verizon-Yahoo deal saw a $350M price reduction following breach disclosures — a number that would have been recoverable with pre-LOI diligence.
Top Cyber Risk Assessment Providers for M&A Compliance in 2026
Selection criteria for each provider below:
- Demonstrated M&A due diligence capability across buy-side and sell-side engagements
- Compliance framework coverage relevant to regulated industries
- Board-ready reporting quality that deal teams and legal counsel can act on
- Ability to operate within compressed deal timelines
Kroll
Kroll runs one of the largest dedicated M&A cyber due diligence practices globally, with a transaction services practice spanning hundreds of buy-side and sell-side engagements across financial services, healthcare, and critical infrastructure.
Kroll integrates threat intelligence from thousands of incident response engagements and regulatory compliance gap analysis into a single M&A workflow. Their three-tier framework spans external digital footprint analysis, inquiry-based reviews, and technology-facilitated internal assessments.
Findings map directly to indemnification schedules, escrow calculations, and representations and warranties language — outputs deal teams and legal counsel can act on without translation.
| Feature | Details |
|---|---|
| M&A-Specific Services | Buy-side and sell-side cyber due diligence, pre-close risk quantification, post-close remediation roadmaps |
| Compliance Frameworks Covered | SOC 2, ISO 27001, NIST CSF, HIPAA, GDPR, PCI DSS |
| Best Suited For | Mid-market to enterprise transactions in regulated industries; PE-backed deal teams requiring audit-defensible findings |
SecurityScorecard
SecurityScorecard provides continuous, data-driven security ratings widely used by M&A deal teams and private equity firms to rapidly establish a target company's external security posture before full diligence begins. This enables acquirers to triage risk and prioritize assessment depth during early stages.
Its M&A-specific capabilities include side-by-side portfolio scoring, integration risk dashboards, and supply chain visibility showing inherited third-party exposure. PE case studies demonstrate how sponsors use SecurityScorecard to manage multi-target diligence pipelines and platform acquisition strategies at scale.
| Feature | Details |
|---|---|
| M&A-Specific Services | Rapid external security posture scoring, portfolio-level risk comparison, supply chain and vendor exposure analysis |
| Compliance Frameworks Covered | NIST CSF, CIS Controls, GDPR readiness indicators, ISO 27001, HIPAA, PCI DSS, SOC 2, DORA, NIS2 |
| Best Suited For | PE firms and corporate development teams needing scalable, fast-turnaround risk triage across multiple targets |
Coalfire
When a target company's certification status — SOC 2, FedRAMP, ISO 27001 — is a material deal term or integration dependency, Coalfire is purpose-built for that scenario. The firm's M&A advisory services bridge technical security assessment and regulatory certification readiness in a single engagement.
Coalfire's differentiator is its ability to produce assessment outputs satisfying both technical due diligence requirements and the documentation standards expected by regulatory auditors and cyber insurers — reducing duplicative work across the deal lifecycle. As a recognized FedRAMP 3PAO, Coalfire brings certification expertise critical for government-adjacent transactions.
| Feature | Details |
|---|---|
| M&A-Specific Services | Compliance gap assessments, certification readiness reviews, regulatory liability mapping for M&A transactions |
| Compliance Frameworks Covered | SOC 2, FedRAMP, ISO 27001, PCI DSS, HIPAA, DORA, NIS2, and 100+ global frameworks |
| Best Suited For | Organizations where compliance certification status is a material deal term or integration dependency |

Mandiant (Google Cloud Security)
Where Coalfire focuses on certification posture, Mandiant — now within Google Cloud Security — addresses a different risk: whether the target is already compromised. Their compromise assessment service identifies prior breaches, active targeting, or breach indicators that could surface post-close as material incidents.
For high-value or strategic acquisitions, Mandiant's combination of frontline incident response history and nation-state threat intelligence provides adversarial context that compliance-only assessments cannot provide — giving boards and deal teams visibility into inherited risk that standard frameworks won't surface.
| Feature | Details |
|---|---|
| M&A-Specific Services | Threat intelligence-led due diligence, compromise assessment, post-close incident readiness review |
| Compliance Frameworks Covered | NIST CSF, ISO 27001, sector-specific frameworks; incident-driven regulatory posture analysis |
| Best Suited For | Strategic or high-value acquisitions where undisclosed compromise, nation-state exposure, or advanced threat risk is a material concern |
Deloitte Cyber Risk Services
Deloitte Cyber Risk Services integrates M&A cyber due diligence into its broader transaction advisory practice. This allows deal teams to receive technical security findings alongside financial, operational, and legal risk analysis within a unified framework that boards and general counsel can act on cohesively.
Cross-border transactions — where multiple data protection regimes, compliance obligations, and integration risk factors must be assessed simultaneously — are where Deloitte's sector depth and regulatory expertise across financial services, healthcare, government, and technology carry the most weight.
| Feature | Details |
|---|---|
| M&A-Specific Services | End-to-end M&A cyber due diligence, integration risk planning, regulatory exposure mapping, board-level risk reporting |
| Compliance Frameworks Covered | GDPR, CCPA, SOC 2, ISO 27001, NIST CSF, sector-specific frameworks (HIPAA, DORA, FedRAMP) |
| Best Suited For | Large, complex, or cross-border transactions requiring integrated cyber and regulatory due diligence within a unified advisory structure |
How to Choose the Right M&A Cyber Risk Assessment Provider
The most common mistake buyers make is scoping cyber assessment like a standard IT audit — assigning it too late, underestimating timeline, or selecting a provider without M&A deal experience. M&A cyber assessments must be scoped against deal structure, target industry, data assets, and post-close integration plans, not just generic control checklists.
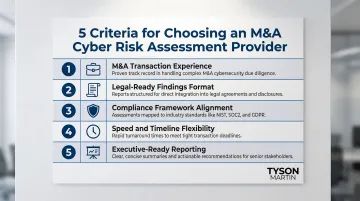
Five criteria matter most:
- Demonstrated M&A transaction experience — not just general cybersecurity credentials
- Findings in a format usable by legal counsel — for reps and warranties and indemnification structuring
- Compliance framework alignment — with the target's operating environment and regulatory obligations
- Speed and flexibility — to operate within compressed deal timelines
- Executive-ready reporting — that boards and general counsel can act on without translation
Organizations without an internal CISO, or with a CISO who lacks M&A-specific governance experience, often benefit from engaging a fractional CISO or board-level cyber advisor. Advisors like Tyson Martin define scope requirements, translate assessment findings into business risk language, and help boards ask the right questions before and after due diligence closes.
That advisory lens extends beyond signing day. Post-close matters as much as pre-close — the right provider delivers a remediation roadmap and integration risk framework, not just a point-in-time findings report that loses value the moment the deal closes.
How We Selected These Providers
Each provider on this list was evaluated against five criteria:
- Publicly documented M&A due diligence service offerings
- Demonstrated experience in regulated industry transactions
- Compliance framework breadth across relevant standards
- Reporting quality suited to board and legal audiences
- Ability to operate across deal sizes from mid-market to enterprise
This assessment is editorially independent — no paid placements, sponsorships, or affiliate relationships influenced the selections. Organizations should still conduct their own due diligence, request sample deliverables, and verify that provider experience aligns with their specific deal type, target industry, and regulatory environment.
Conclusion
Choosing a cyber risk assessment provider for M&A compliance in 2026 is a governance decision, not technical procurement. The right provider protects deal value, limits inherited liability, and produces board-ready intelligence that informs both negotiation and integration.
What makes the difference isn't brand or firm size. The providers that deliver in M&A contexts share three qualities:
- M&A-specific experience across pre-close diligence and post-close integration
- Regulatory alignment relevant to the deal's industry and jurisdiction
- Reporting clarity that legal counsel and the board can act on — not just technical summaries
These criteria should drive the selection conversation, not vendor reputation alone.
Organizations navigating M&A, new leadership transitions, or post-close integration can reach out to Tyson Martin directly. As a board-level cyber advisor, he clarifies risk, defines decision rights, and translates technical findings into governance your board can act on.
Frequently Asked Questions
What is a cyber risk assessment in the context of M&A due diligence?
It's a structured evaluation of a target company's security posture, compliance obligations, data governance practices, and control gaps — conducted to identify risks affecting deal valuation, post-close integration cost, or the acquiring party's regulatory exposure.
When in the M&A process should a cyber risk assessment be conducted?
Preliminary external assessments (such as security ratings) are often run pre-LOI, with deeper compliance and control assessments during formal due diligence. Post-close assessments should inform integration planning within the first 90 days.
Can a cyber risk gap discovered during M&A due diligence affect deal valuation?
Yes. Material findings can lead to price adjustments, escrow holdbacks, additional reps and warranties insurance requirements, or deal restructuring — particularly when regulatory non-compliance or evidence of prior undisclosed breach is identified.
What compliance frameworks are typically reviewed in an M&A cyber assessment?
Assessments commonly evaluate alignment with SOC 2, ISO 27001, NIST CSF, GDPR, HIPAA, and PCI DSS depending on the target's industry and data environment. Cross-border deals require additional attention to regional data protection regulations.
What is the difference between a cyber risk assessment and a penetration test in M&A due diligence?
A cyber risk assessment evaluates governance, compliance posture, control maturity, and inherited risk exposure at a program level. A penetration test probes specific systems for exploitable vulnerabilities. Both serve distinct purposes, but the assessment takes priority in compliance-driven diligence.
How long does an M&A cyber risk assessment typically take?
Timeline varies by scope and complexity. External security ratings can be generated in days, while a full compliance-aligned due diligence assessment typically requires two to six weeks. Deals with compressed timelines should build assessment lead time into their diligence schedule.