Introduction: Why Your CaaS RFP Will Make or Break the Engagement
Organizations issuing poorly scoped RFPs for CISO-as-a-Service typically receive responses that look similar on paper but deliver wildly different results when the engagement goes live. The RFP itself is the first test of whether a provider can deliver governance rather than just activity logs.
The stakes are real: 79% of security service providers report high demand for vCISO services, while the pool of qualified executive-level security leaders continues to shrink. The global cybersecurity workforce gap stands at 4.8 million professionals—a 19% increase year-over-year. This supply-demand mismatch means the RFP process must filter rigorously for providers who can own governance outcomes, not just report on activity.
Understanding the three CaaS engagement models is critical before drafting your RFP:
- Virtual CISO: Remote strategic advisory with defined monthly hours, typically 20-40 hours per month
- Fractional CISO: Ongoing executive ownership at lower time commitment, usually part-time but indefinite duration
- Team-based CaaS: Provider organization assigns a lead CISO plus supporting analysts or program managers
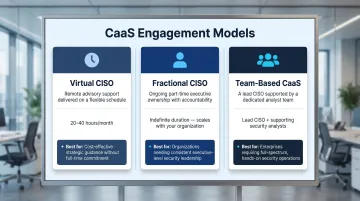
Your RFP structure must reflect which model you're actually buying, because evaluation criteria differ materially. A virtual CISO RFP should prioritize board reporting fluency and governance artifacts. A team-based model requires organizational stability, bench depth, and succession planning that solo practitioners cannot offer.
Getting that model clarity right is what separates a productive engagement from an expensive mismatch. This guide covers the seven essential RFP categories and the highest-signal questions to identify true strategic advisors. It also includes a scoring methodology that weights governance quality over certifications, along with a red flag/green flag framework for evaluating proposals.
TLDR
- Organize your CaaS RFP into seven categories: provider background, executive qualifications, service delivery, governance and board reporting, compliance coverage, SLA terms, and pricing
- Demand evidence instead of claims—request sample board reports, 90-day onboarding plans, and documented escalation thresholds
- Score proposals on governance quality and communication clarity rather than certification counts
- Prioritize providers with enterprise-grade experience who translate risk into business terms, not just technical language
- Limit your RFP to 5-8 qualified providers, then narrow to 3 finalists for structured interviews
Why Issue a Formal RFP for CISO-as-a-Service?
Unlike commodity IT services, CaaS engagements involve a senior advisor who will influence board-level decisions, regulatory posture, and risk tolerance. A structured RFP protects your organization from underqualified vendors who present well in sales meetings but lack the strategic depth to hold up under a real breach or regulatory inquiry.
The practical value of an RFP for CaaS:
- Forces internal alignment on what your organization actually needs—project-based vs. ongoing, compliance-only vs. full program leadership
- Creates defensible audit trail for the selection decision, which matters when regulators or board committees review procurement
- Generates side-by-side comparison that's especially important when price quotes vary significantly across providers
- Tests provider governance fluency before signing a contract—their RFP response quality previews the quality of deliverables they'll produce for your board
The regulatory landscape has shifted materially. The SEC cybersecurity disclosure rules now require material incident disclosure via Form 8-K and annual risk management disclosure in Form 10-K. CMMC Phase 1 implementation began November 10, 2025, with full rollout extending through 2028.
Your fractional CISO will need to navigate these frameworks fluently—not just understand them in theory.
The cost of a wrong hire compounds fast: breaches exceeding 200-day lifecycles cost $5.01M on average—$1.39M more than breaches contained faster. That gap is largely an executive response problem. SLA terms and escalation commitments in your RFP are where that risk either gets controlled or gets ignored.
What to Include in a CaaS RFP: The Seven Core Categories
Category 1 — Provider Background and Organizational Stability
What to request:
- Years in business and number of active CaaS clients currently under contract
- Revenue percentage invested in R&D or continuing education for advisory staff
- Subcontractor or affiliate relationships that would be used to deliver services
- Professional liability or E&O insurance coverage limits and policy details
- Organizational structure—solo practitioner, partnership, or firm with multiple CISOs
Why continuity matters:
A solo practitioner and a firm have different risk profiles. Solo practitioners may offer deeper personal engagement but create single-point-of-failure risk if they're unavailable during an incident. Firms provide bench depth but may rotate personnel. Your RFP should surface these tradeoffs explicitly.
If the provider subcontracts key deliverables, you need to know upfront. Request disclosure of which services are delivered in-house versus outsourced, and whether subcontractors have been vetted to the same standard as the primary provider.
Category 2 — Executive Qualifications and Bench Depth
What to specify:
- Resume for the named individual who will serve as your CISO (not just company credentials)
- Relevant certifications: CISSP, CISM, and CISA are the baseline—approximately 170,000 CISSP holders globally and 100,000+ CISM holders
- Executive experience at comparable organizations—has this person held a full-time CISO role or are they an IT security director being repackaged?
- Whether a backup or transition plan exists if the named individual leaves or becomes unavailable
- Industry-specific credentials where relevant: HCISPP for healthcare, QSA for payment card environments
The CISO role focuses on risk assessment, digital security policies, incident response, and cybersecurity governance—distinct from the CIO role, which oversees overall technology strategy and IT resource integration. Your RFP must verify that the candidate has true CISO-level experience, not rebranded IT operations management.
Request specific examples: "Describe the most complex security transformation you've personally led—not as a consultant, but as a named executive. What was the outcome?"
Category 3 — Service Scope, Delivery Model, and Time Allocation
What to define:
- Monthly hours committed and how they're allocated (strategic vs. operational)
- Whether services are delivered remotely or on-site, and what triggers on-site presence
- How the provider handles surge needs: M&A security due diligence, active incidents, imminent audits
- Which deliverables are included in the base engagement vs. billed separately
- Defined exclusions—what is explicitly out of scope
Scope creep in CaaS engagements almost always starts here. Be specific about what "fractional CISO" means in hours per month: does it include board meetings, vendor reviews, and policy development? If a material incident occurs, does the provider participate in real-time response or only post-incident analysis?
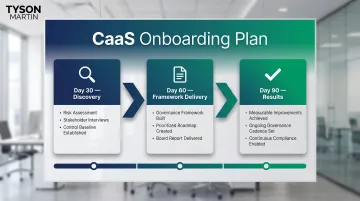
Request a sample 30/60/90-day onboarding plan with owners and measurable outcomes. If the provider cannot produce this during the RFP phase, they're unlikely to deliver structured governance during the engagement.
Category 4 — Governance, Board Reporting, and Decision Rights
Board reporting is where most fractional CISOs reveal whether they're operating strategically or just staying busy. Ask for evidence, not assertions.
What to request:
- Sample board or executive reports (anonymized) the provider has actually delivered
- Documentation on how the provider establishes decision rights and escalation thresholds
- How they translate technical risk into financial and operational terms for non-technical audiences
- Examples of risk posture summaries that differentiate between trend and noise
According to the NACD 2026 Cyber Risk Handbook, board-level cybersecurity metrics should cover five categories:
- What is the threat environment we face?
- What is our cyber loss exposure in economic terms?
- What is our cyber-risk profile?
- What is our supply chain exposure?
- Are we making the right business and operational decisions?
Evaluate whether the provider's sample deliverables align with this framework. Do they communicate potential revenue loss, downtime costs, and regulatory penalties—or just patch counts and firewall rules?
Board-CISO alignment dropped to 64% in 2025, down from 84% in 2024. That 20-point decline suggests many organizations implement the form of board cyber oversight without the substance. Your RFP should test for providers who can build and sustain trust-based board relationships, not just generate reports.
Category 5 — Compliance Coverage, Regulatory Fluency, and Risk Frameworks
What to ask:
- Which frameworks the provider actively works within: NIST CSF, ISO 27001, SOC 2, PCI DSS, HIPAA, CMMC, SEC cyber disclosure rules
- How they stay current with regulatory changes and translate them into client advisory work
- Whether they can produce audit-ready evidence packages and support audit preparation
- For 2026 specifically: fluency in AI risk governance frameworks including NIST AI RMF and ISO/IEC 42001
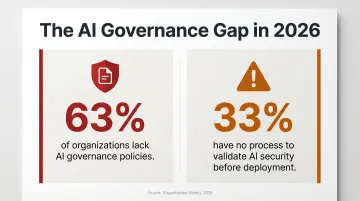
AI governance has become critical:
63% of organizations lack AI governance policies, and 33% have no process to validate AI security before deployment. If your organization uses or plans to deploy AI systems, your CaaS provider must demonstrate documented methodology for AI risk assessment and governance.
Ask: "Which frameworks have you led clients through most recently, and what were the audit or certification outcomes?" Vague claims of compliance expertise don't count. Request specific examples with verifiable results.
Category 6 — SLA Terms, Escalation, and Incident Support
Most CaaS RFPs define what the CISO will do—but not what happens when things go wrong at 2 a.m. on a holiday weekend. SLA terms close that gap.
What to specify:
- Sample SLA document with defined response time commitments for urgent security events
- Whether the provider participates in incident response or only post-incident analysis
- How SLA non-compliance is measured and remediated
- What happens when the named individual is unavailable—is a qualified backup contractually guaranteed?
The IBM data provides clear justification for strict SLA terms: breaches with lifecycles exceeding 200 days cost $1.39M more than faster-contained breaches. Executive response time directly impacts financial outcomes.
Your SLA should define three tiers:
- Critical incidents (material breach requiring board notification): Response within 2 hours
- High-priority incidents (significant security event): Response within 4 hours
- Routine advisory requests: Response within 1 business day
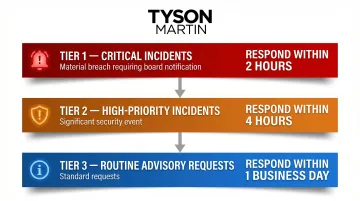
Request explicit language about backup coverage. If your fractional CISO is on vacation when ransomware hits, who responds?
Category 7 — Pricing Structure and Contract Terms
Pricing models vary significantly across CaaS providers.
What to request:
- Fully itemized fee structure: hourly, retainer, flat monthly, or tiered by scope
- Whether pricing is fixed or consumption-based
- Contract duration and termination provisions (notice period, early termination penalties)
- What is explicitly excluded from the base engagement and would trigger additional charges
Typical pricing structures:
- Hourly: $250-$500/hour for qualified CISOs, billed monthly
- Retainer: $5,000-$15,000/month for defined scope and hours
- Flat monthly: $8,000-$20,000/month for comprehensive fractional CISO coverage
- Tiered: Basic ($5K/month), Standard ($10K/month), Premium ($15K+/month) based on scope
Compare full 12-month costs, not just the monthly rate. A provider at $8,000/month with a defined scope can cost less than a $5,000/month provider who charges hourly overages for every board meeting and policy review.
High-Value Questions to Ask Every CaaS Provider
Governance and Board Fluency Questions
Board governance is where most CaaS providers fall short. These questions surface whether a provider can actually function at the board level—not just produce slide decks.
Question 1: "Provide a sample board-level cyber risk summary from a prior engagement (anonymized). How does your reporting differentiate between trend and noise?"
Look for reports that:
- Communicate risk in business terms (revenue impact, regulatory exposure)
- Show trend data over time, not just current-state snapshots
- Highlight what changed since the last briefing
- Include clear decision points for the board
Question 2: "Describe how you establish and document decision rights and escalation thresholds at a new client. What does that look like in the first 90 days?"
Strong answers will reference:
- Documented RACI matrices for security decisions
- Written escalation thresholds tied to business impact
- Clear ownership for risk acceptance vs. risk mitigation
- Regular governance cadences (weekly, monthly, quarterly)
Question 3: "How do you communicate a material change in risk posture to a board that has limited technical background?"
Evaluate whether the provider:
- Translates technical events into business outcomes
- Uses plain-English language consistently
- Provides context and trend, not just alerts
- Recommends specific board actions with cost/benefit tradeoffs
Qualification and Independence Questions
Credentials matter less than accountability. These questions distinguish providers who've held genuine executive responsibility from those who've only advised from the sidelines.
Question 4: "Describe the most complex security transformation you've personally led—not as a consultant, but as a named executive. What was the outcome?"
Look for:
- Named organizations and measurable outcomes
- Direct accountability for budget, staffing, and execution
- Evidence of board-level reporting and stakeholder management
- Specific metrics: time to contain incidents, audit findings reduced, compliance achieved
Question 5: "Do you serve any vendors whose products you might recommend to our organization? How do you manage that conflict?"
Conflicts of interest are common in the CaaS market—and rarely disclosed voluntarily. Demand:
- Full disclosure of vendor relationships and referral fees
- Written policy on maintaining independence
- Separation between advisory and product sales
Question 6: "Who is your backup if you are unavailable during a security incident?"
Solo practitioners must have documented coverage arrangements. Firms should assign a named backup with comparable credentials. No acceptable answer includes "we'll figure it out."
Service Delivery and Scope Questions
Scope and delivery mechanics determine whether you get a functional security program or an expensive status call. Push for specifics.
Question 7: "Walk us through your standard onboarding process—what does your 30/60/90 day plan look like?"
Strong providers will produce a templated plan showing:
- 30 days: Risk assessment, stakeholder interviews, control baseline
- 60 days: Governance framework, prioritized roadmap, board report
- 90 days: Measurable improvements, ongoing cadence established
Question 8: "What is explicitly not covered by your base engagement, and what would trigger an out-of-scope charge?"
Scope creep destroys CaaS engagements. Providers should clearly define:
- Exclusions: hands-on penetration testing, 24/7 SOC operations, technology implementation
- Triggers for additional billing: M&A due diligence, incident response beyond advisory support, audit preparation exceeding X hours
Question 9: "How do you handle a situation where your risk recommendation conflicts with what our CEO or board wants to do?"
Providers who can't answer this credibly aren't actually serving an executive function. Look for answers that demonstrate:
- Documenting the risk and leadership's acceptance in writing
- Escalating to audit or risk committee when necessary
- Walking away from engagements where ethical lines are crossed
Regulatory and Compliance Questions
Regulatory exposure is a top driver of CaaS engagements. These questions confirm whether a provider has done the actual work—not just studied the frameworks.
Question 10: "Which frameworks have you led clients through most recently, and what were the audit or certification outcomes?"
Request specific details:
- SOC 2 Type II achieved within X months
- ISO 27001 certification with zero non-conformities
- CMMC Level 2 certification completed ahead of DoD deadline
Question 11: "How do you approach AI risk governance—do you have a documented methodology, and have you applied it?"
For 2026, this is non-negotiable. Evaluate whether the provider:
- References NIST AI RMF or ISO/IEC 42001 specifically
- Has conducted AI risk assessments for clients
- Can produce sample AI governance frameworks or board briefings
Question 12: "Describe how you've helped a client meet a compliance deadline they were behind on when you were engaged."
Vague answers here are a red flag. A provider who has done this work will remember the details. Look for:
- Specific timeline compression achieved
- How they prioritized critical path activities
- Whether the audit/certification was successful
Reference and Evidence Questions
References and incident history are the closest thing to due diligence available in an advisory relationship. Use them.
Question 13: "Provide 2-3 referenceable clients in a similar industry. What specific deliverables did you produce for them?"
Contact references directly and ask:
- Did the provider's deliverables hold up under an actual audit or incident?
- Did the board find their reporting useful?
- Did they push back effectively when leadership wanted to take on unacceptable risk?
Question 14: "Provide documentation of a security incident where your guidance was directly tested. What was the outcome?"
Incidents reveal true capability. Request anonymized incident timelines showing:
- How quickly the provider engaged
- What guidance they provided
- Whether their escalation thresholds held under pressure
- Post-incident lessons learned and improvements implemented
Scoring and Evaluating CaaS RFP Responses
Establish a Weighted Scoring Framework
Build a simple weighted matrix that makes comparison defensible:
| Evaluation Dimension | Weight | Scoring Criteria |
|---|---|---|
| Executive qualifications | 30% | Named individual's resume, CISO-level experience, certifications |
| Governance and board communication quality | 25% | Sample board reports, plain-English risk summaries, trend vs. noise differentiation |
| Scope clarity and deliverable specificity | 20% | 30/60/90 plan, defined exclusions, SLA commitments |
| Regulatory coverage | 15% | Framework fluency, audit outcomes, AI governance capability |
| Pricing value | 10% | Total cost of ownership, contract terms, scope-to-price ratio |
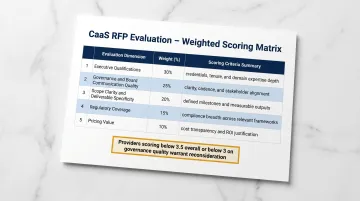
Score each provider 1–5 on each dimension, multiply by weight, and total. Any provider scoring below 3.5 overall—or below 3 on governance quality—warrants serious reconsideration regardless of price.
Evaluate Governance Quality as the Primary Differentiator
The single most important signal is whether the provider's sample deliverables show:
- Plain-English risk posture without technical jargon
- Measurable outcomes with clear owners for every initiative
- Metrics that show trend over time, not dashboards full of raw alerts
- Business impact framing that translates risk into revenue exposure, regulatory liability, and reputational consequence
Fractional CISOs who have operated at enterprise scale—where board reporting is a real accountability, not a slide deck exercise—produce materially different deliverables than IT security generalists. The difference shows up in sample outputs, not sales conversations.
99% of highly resilient organizations report board-level involvement in cybersecurity, yet only 52% receive regular cybersecurity updates. The gap between board involvement and board insight comes down to communication quality—exactly what your RFP evaluation should prioritize.
Conduct Structured Follow-Up Interviews with Finalists
The written RFP response should be followed by a structured 60-minute interview where the named individual (not a sales representative) walks through their approach to a real-world scenario.
Sample scenario:
"Our board wants to delay a $500K security infrastructure investment to meet quarterly earnings targets. The investment addresses a critical vulnerability in our payment processing environment. Walk us through how you would advise the CEO and board."
What to evaluate:
- Do they communicate the business risk in financial terms?
- Do they offer alternative risk mitigation options with cost/benefit analysis?
- Can they articulate how to document the board's risk acceptance if leadership proceeds anyway?
- Do they know when to escalate to the audit committee or external advisors?
Check References Rigorously
Ask references:
- "Did the provider's deliverables hold up under an actual audit or incident?"
- "Did the board find their reporting useful—did it drive decisions or just inform?"
- "Did they push back effectively when leadership wanted to take on unacceptable risk?"
- "Would you hire them again, and for what type of engagement?"
References should be recent (within 18 months) and from organizations facing similar regulatory or operational complexity. Strong references on all four questions give you reasonable confidence the written proposal reflects how the provider actually operates under pressure.
Red Flags and Green Flags in Provider Responses
Green Flags That Indicate a Strong CaaS Provider
Executive Credentials
- Named executive with a verifiable full-time CISO track record at comparable organizations
- Active membership in governance bodies: NACD, WEF Centre for Cybersecurity, National Retail Federation CISO Executive Committee, ISC2 leadership roles
- Executive education from recognized programs: Carnegie Mellon CISO Executive Program, Harvard, MIT
Deliverable Quality
- Sample board reports that communicate risk in business terms with clear trend data
- Documented 90-day onboarding plan with owners and measurable outcomes
- Risk posture summaries that show what changed since the last briefing
Commercial Transparency
- Clear pricing structure with defined scope and exclusions
- Professional liability insurance with appropriate coverage limits
- Documented backup coverage and transition planning
Regulatory Fluency
- Specific framework experience with verifiable audit or certification outcomes
- Documented AI risk governance methodology aligned with NIST AI RMF or ISO/IEC 42001
- Current engagement with regulatory changes affecting your industry
Red Flags That Indicate a Provider Is Overpromising or Underqualified
Credential Gaps
- Inability to provide the named individual's resume upfront
- Certifications only at the team level, not the individual who will serve as your CISO
- No verifiable full-time CISO experience—just IT director or consultant roles repackaged
Deliverable Weakness
- Sample reports consisting primarily of technical metrics without executive narrative
- Inability to produce a documented 90-day onboarding plan during the RFP process
- Generic dashboards showing raw alert counts rather than business risk trends
Commercial Red Flags
- Pricing that is purely hourly with no commitment to outcomes
- No defined SLA or vague language about response times
- No professional liability insurance or unwillingness to disclose coverage limits
Governance Gaps
- Vague answers about how they handle conflicts between their recommendation and leadership preference
- No referenceable clients in a comparable industry or regulatory environment
- Inability to demonstrate AI governance capability when asked directly

What to Do When Responses Are Mixed
Most RFP evaluations surface at least one provider with an uneven profile—strong on credentials, weak on governance documentation, or the reverse.
Use the structured follow-up interview to close those gaps:
- If a provider has strong credentials but weak sample deliverables, test whether their interview responses demonstrate governance fluency their written materials didn't show
- Where board reports are strong but executive experience is thin, ask for two or three specific examples of decisions made under pressure—and listen for accountability, not credit-taking
If the interviews don't close the gaps, the issue may be the RFP itself. When no providers can deliver what you originally requested within budget, three paths forward exist:
- Narrow scope to the most critical deliverables
- Extend timeline to allow phased implementation
- Increase budget to match market rates for the capability you need
Hiring an underqualified provider because they were the only one who fit the budget is the worst outcome in this process. Re-scoping costs time. Recovering from a failed engagement costs significantly more.
Frequently Asked Questions
What makes a CaaS RFP different from a standard IT services RFP?
A CaaS RFP focuses on executive qualifications, board-level governance output, and strategic risk leadership rather than technical service specifications or SLA uptime metrics. The most critical evaluation factors are the named individual's credentials and their ability to produce board-ready deliverables that translate technical risk into business terms.
How many vendors should be included in a CaaS RFP process?
Send the RFP to 5-8 qualified providers to generate meaningful comparison, then narrow to 3 finalists for structured interviews. Sending to too few limits negotiating leverage, while too many makes evaluation unmanageable and delays the selection process.
What certifications should a CISO-as-a-Service provider hold?
Certifications confirm knowledge but don't substitute for executive experience. CISSP, CISM, and CISA are the standard baselines; HCISPP (healthcare) and QSA (payment card) add industry relevance. Verify the candidate has held a full-time CISO role with direct accountability for security program outcomes.
Can a fractional CISO fulfill board reporting obligations?
A qualified fractional CISO can and should own board reporting. The ability to translate technical risk into business-relevant terms for directors is a defining capability of the role. Organizations should request sample board reports during the RFP process to verify this fluency before signing a contract.
How long does a CaaS RFP process typically take from issuance to selection?
Plan for 6-10 weeks: roughly 1-2 weeks for distribution, 2-3 weeks for vendor responses, and 2-4 weeks for scoring, interviews, and reference checks. Incident recovery or imminent audit situations can compress this to 4-6 weeks.
What should a CaaS SLA include that most organizations forget to require?
Most organizations omit two requirements: a defined response time for urgent security events (separate from scheduled deliverables), and explicit terms covering named-individual unavailability. Confirm contractually that any backup holds comparable credentials and authority.