Introduction
Most boardroom conversations about cyber resilience default to the CISO, but the CIO carries equal accountability for the infrastructure, technology decisions, and operational continuity that determine whether an organization survives a disruption. Fewer than 15% of U.S. public companies disclose having a board member with cybersecurity experience, and when boards do engage on cyber topics, they often skip the CIO entirely—leaving a critical oversight gap.
This gap isn't a failure of intent. CIOs are positioned as business enablers, which makes it easy for boards to accept optimistic updates about digital transformation progress without interrogating operational resilience. 79% of CISOs have felt boardroom pressure to downplay the severity of cyber risks. Comfort and confidence routinely eclipse actual readiness in these conversations.
The questions below reveal whether your organization can execute, recover, and adapt when pressure arrives. They are not compliance questions—they are governance questions designed to surface whether decision-making infrastructure exists, not just whether documentation does.
TLDR
- Most boards direct cyber questions to the CISO, overlooking the CIO's accountability for infrastructure and operational continuity
- Strong board questions produce specific answers—names, dates, tested results—not framework references or vendor lists
- Technology debt, untested recovery plans, and shadow AI adoption are blind spots boards consistently miss
- Effective CIO oversight requires quarterly trend-based reporting, not point-in-time status updates
- Regulatory frameworks including SEC rules and DORA now place technology governance squarely on the board's agenda
Why Boards Ask the Wrong Questions of Their CIO
The CIO role differs fundamentally from the CISO role, yet boards often conflate them or skip the CIO entirely during cyber resilience discussions. The CISO owns security policy, threat detection, and incident response. The CIO owns technology governance, infrastructure stability, operational continuity, and digital transformation. Both roles matter, but boards need distinct, targeted questions for each.
The confusion creates a deflection pattern. CIOs under-prepared for board scrutiny respond with project updates, vendor names, or framework references that sound like progress but reveal nothing about actual resilience readiness. A CIO might reference ISO 27001 certification, name a cloud migration partner, or cite NIST alignment—all of which describe documented intent, not operational reality.
Frameworks and certifications are valuable tools, but they don't answer the core governance question: Can you execute when pressure arrives? 80% of boards only act decisively on cyber risk after a breach occurs, suggesting that early warning signals are either absent or ignored.
Regulatory Context: Technology Oversight Is Now Board Accountability
Recent regulatory guidance places technology oversight—not just security oversight—on the board's accountability agenda:
- SEC (2023): Final rules require annual disclosure of board oversight of cybersecurity risk, identification of the responsible board committee, and management's role in assessing material risks. Material incidents must be reported within four business days.
- DORA (EU): Article 5 requires management bodies to bear "ultimate responsibility" for managing ICT risk, with members required to "actively keep up to date with sufficient knowledge and skills to understand and assess ICT risk."
- NACD Guidance: Positions cybersecurity oversight as "a core component of a board's fiduciary oversight duties" and calls for boards to move beyond "reactive, compliance-focused, check-the-box mentality."
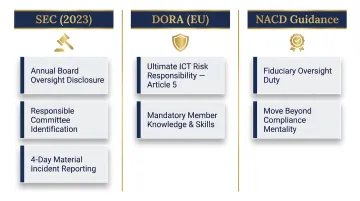
These frameworks share a common thread: boards cannot delegate technology governance to management and maintain no inspectable oversight. They must ask informed questions and demand inspectable answers.
The 7 Questions Every Board Should Ask Their CIO About Cyber Resilience
Strong questions produce specific, named, measurable answers. Vague answers are themselves a finding. The following seven questions test whether the CIO's program is operational and inspectable—not just documented.
Question 1: What is our current technology risk exposure—and where is it growing?
A credible answer names the top 2–3 technology-driven risks by category—such as unpatched infrastructure, end-of-life systems, or cloud misconfigurations—describes what has changed since the last briefing, and quantifies exposure in business terms, not in technical jargon alone.
What boards are testing for:
- Does the CIO articulate risk in language that connects to business operations?
- Is the CIO tracking change over time, or only reporting a snapshot?
- Does the organization understand which technology risks create the most business exposure?
Why it matters: 92% of executives report their teams must deprioritize essential work to address unplanned downtime, and IT outages cost businesses a median of $76 million annually. Technology risk isn't theoretical—it's operational and financial.
Red flags:
- Responses that reference frameworks or vendor names without naming specific risks
- Inability to describe what changed since the last board briefing
- No mention of business impact or quantified exposure
Question 2: Which critical systems have no tested recovery plan?
This question exposes the gap between documented business continuity plans (BCPs) and operational readiness. A board-ready answer names specific systems, their recovery time objectives (RTOs), when they were last tested, and what the results showed—not a general statement that a plan exists.
What boards are testing for:
- Which systems are genuinely recoverable—and which are untested assumptions?
- Are recovery plans tested under realistic conditions, or only on paper?
- Do stated RTOs reflect validated results, or wishful targets?
Why it matters: The testing gaps are striking:
- 71% of organizations conduct no failover testing to validate outage prevention protocols
- Only 33% run disaster recovery simulations
- 35% require days or weeks to recover lost SaaS data
- Average outage resolution runs 196 minutes—far beyond most documented RTOs

When recovery plans go untested, documented RTOs become aspirational, not operational.
Red flags:
- Responses that confirm a plan exists but can't name the last test date
- No mention of test results or gaps discovered
- RTO numbers presented without evidence they've been validated
Question 3: How is technology debt being measured, prioritized, and funded?
Technology debt—unsupported systems, deferred upgrades, legacy integrations—is a direct resilience liability. The CIO should be able to show a current inventory of end-of-life systems, an estimate of associated risk, and a funded remediation plan with timelines—not a general acknowledgment that debt exists.
What boards are testing for:
- Is technology debt treated as a governance priority or a backlog wish list?
- Does the organization have a realistic plan to reduce exposure, or is debt accumulating faster than it's being addressed?
- Is remediation funded, or dependent on future budget cycles?
Why it matters: Gartner projected that by 2025, 40% of the average IT budget would be consumed by technical debt. Even more concerning, up to 60% of breaches are tied to unpatched vulnerabilities.
Red flags:
- Responses that acknowledge debt exists but provide no inventory or timeline
- No connection between debt and business risk
- Remediation plans that lack funding or named owners
Question 4: Who holds the authority to take systems offline during an active incident—and what triggers that decision?
Decision authority in a crisis is not the same as having a role listed on an org chart. Boards should push for named individuals, pre-defined thresholds, and a documented escalation path that does not require consensus before action can be taken.
What boards are testing for:
- Will the organization act decisively during an incident, or will decisions stall waiting for consensus?
- Are authority thresholds documented and known in advance?
- Does the CIO have the delegated authority to protect operations, or must every decision escalate?
Why it matters: Incidents move faster than consensus-building. If decision rights are ambiguous, critical minutes are lost while leadership debates who has authority to act. The median time between publication of a new critical vulnerability on edge devices and mass exploitation is zero days. Unresolved decision authority at that point is an operational liability.
Red flags:
- rather than adopted by business units independently and flagged only after the fact. Ask for examples of recent technology decisions that included a risk tradeoff analysis.
What boards are testing for:
- Does the CIO have visibility into technology adoption across the organization?
- Are risk reviews happening proactively, or reactively after adoption?
- Vendor audits referenced but no process described for tracking results over time
- Inability to name the process for responding to vendor compromises
Question 7: What does the 90-day technology roadmap show about risk reduction—and who owns each item?
A resilience roadmap should have named owners, measurable outcomes, and a defined reporting cadence—not a project inventory with no accountability attached. If the CIO cannot identify the top three actions underway to reduce technology risk, with owners and timelines, the governance infrastructure is not yet in place.
What boards are testing for:
- Is the CIO managing risk reduction proactively, or reacting to incidents?
- Are priorities clear, or is everything treated as equally urgent?
- Can progress be tracked and reported consistently?
Why it matters: A roadmap without accountability is a wish list. Boards need to see that risk reduction is funded, assigned, and tracked—not deferred indefinitely.
Red flags:
- Project lists that lack named owners or committed timelines
- No mention of risk reduction—only feature delivery or modernization
- Inability to identify the top three priorities or their status
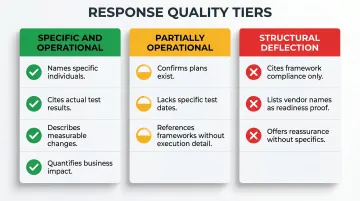
What Strong Answers Look Like—and How to Spot Deflection
Answers that reference specific individuals, thresholds, tested results, and recent changes indicate that decision-making infrastructure exists. Answers that reference frameworks, percentages, vendor names, or org charts without context indicate that readiness is documented but not operational.
Three Response Types Boards Will Encounter
1. Specific and Operational
- Names individuals responsible for decisions
- Cites recent test results and what they revealed
- Describes what changed since the last briefing
- Quantifies exposure in business terms
2. Partially Operational
- Confirms plans exist but can't name test dates or results
- References frameworks or vendors without describing execution
- Provides status snapshots without trend data
3. Structural Deflection
- Cites framework compliance instead of execution evidence
- Lists vendor names or tool deployments as proof of readiness
- Offers reassurance without specifics
The "Framework Trap"
"We use [framework/vendor/tool]" is not an answer to a governance question. Tools and frameworks describe capability, not execution. Boards should follow up any tool or standard reference with: "When was that last tested and what did the test reveal?"
The Value of Trend-Based Reporting
A CIO who can show the board what has changed since the last briefing — risks that decreased, new ones that emerged, actions completed — is operating with governance infrastructure. One who can only report a current status snapshot is not.
That infrastructure doesn't build itself. A board advisor or interim CIO like Tyson Martin works with organizations to establish the stable reporting metrics and escalation thresholds that make these kinds of defensible, trend-based answers possible — before the board has to ask for them.
CIO-Specific Blind Spots Boards Often Miss
Technology Debt Is Under-Discussed Compared to Security Posture
Boards are often shown security metrics—patch compliance percentages, vulnerability scan results—while unpatched infrastructure, end-of-life systems, and unsupported platforms continue to accumulate risk. This creates a dangerous blind spot: up to 60% of breaches are tied to unpatched vulnerabilities, yet technology debt rarely appears on board risk dashboards.
Boards should ask for a current inventory of end-of-life systems and legacy platforms, an assessment of associated risk, and a funded plan to reduce exposure over time.
The AI Adoption Blind Spot
As business units deploy AI tools for productivity, the CIO's ability to govern data flow, access controls, and integration points often lags adoption. 63% of organizations lack formal AI governance policies, and 97% of AI-related breach victims lacked proper access controls.
The question worth asking is whether AI tools in use have been reviewed for data exposure and access risk—not just whether an AI policy exists on paper.
The Crisis Coordination Gap
During an incident, the CIO (who controls systems and infrastructure) and the CISO (who leads the security response) must operate with clear, pre-defined roles. Yet 73% of senior cybersecurity decision managers say they would not be adequately prepared to respond to a future incident, with the top gap cited as difficulties coordinating key stakeholders.
A board that hasn't confirmed the CIO-CISO handoff is documented, tested, and rehearsed is assuming coordination will emerge under pressure. It rarely does.
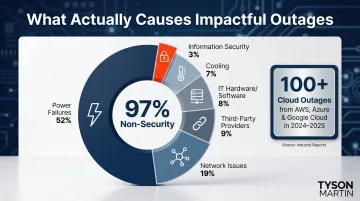
Operational Continuity Is Distinct from Cybersecurity
Resilience is not only about preventing attacks—it includes the ability to maintain or restore operations during technology failures, supply chain disruptions, or cloud outages. Only 3% of impactful outages are information security-related. The remaining 97% break down as:
- Power failures: 52%
- Network issues: 19%
- Third-party providers: 9%
- IT systems hardware/software: 8%
- Cooling: 7%
Boards often conflate cybersecurity readiness with broader operational resilience, but the CIO owns much of the latter. Between August 2024 and August 2025, AWS, Azure, and Google Cloud together experienced more than 100 service outages. That distinction belongs in the board's risk vocabulary.
Building Accountability: Cadence, Metrics, and Decision Rights
Questions are only as valuable as the governance structure behind them. Boards should establish a defined cadence for CIO cyber resilience reporting—at minimum quarterly—and that reporting should show trend data, not just point-in-time status, so the board can see whether risk is increasing, decreasing, or stable over time. The dashboard is where cadence becomes visible.
What a Useful CIO Dashboard Contains vs. What Constitutes Noise
The board does not need a technical deep-dive. It needs:
- A plain-English risk posture summary
- A list of what changed since the last briefing
- The top three risks with owners and mitigation status
- Whether any escalation thresholds have been crossed
Avoid dashboards filled with technical metrics that don't inform decisions. 50% of respondents who manage risk ad hoc experienced a breach in 2025, compared with 27% of those using an integrated, automated approach, suggesting that structured, decision-focused reporting drives better outcomes.
Decision Rights: Clarity Prevents Liability Exposure
The board should know in advance which technology-related decisions require board notification, which require board approval, and which are delegated entirely to management. Ambiguity here creates governance gaps and increases liability exposure when incidents occur.
Effective boards define escalation thresholds in advance and document who must be notified and when. Common triggers include:
- Vendor compromises affecting critical systems
- Unplanned downtime exceeding defined RTOs
- Technology debt that creates material business risk
Frequently Asked Questions
What are some good questions to ask a CIO about cyber resilience readiness?
The most useful questions shift from compliance-based to governance-based, testing whether the CIO can name individuals, dates, tested results, and specific risks—rather than referencing frameworks or tools. Focus on questions that reveal operational readiness: Which systems have no tested recovery plan? Who holds authority to take systems offline during an incident? What changed since the last briefing?
What are the 5 pillars of cyber resilience?
The five pillars from the NIST Cybersecurity Framework are Identify, Protect, Detect, Respond, and Recover. The CIO is primarily accountable for Protect and Recover through technology governance and operational continuity; the CISO typically leads Detect and Respond.
What is the 80/20 rule in cybersecurity?
The 80/20 principle in cybersecurity suggests that a small number of high-priority controls—such as patching, access management, and backup integrity—prevent the majority of incidents. Boards should ask whether the CIO has identified and funded that top 20% of risk-reducing actions, ensuring resources focus on controls with the highest impact.
How often should boards review cyber resilience readiness with the CIO?
At minimum, quarterly reporting with a consistent format that shows trend data over time. Major technology changes, incidents, or regulatory updates should trigger off-cycle briefings—regulated industries often warrant monthly cadence with dashboard visibility.
What is the difference between cyber resilience and cybersecurity?
Cybersecurity focuses on preventing and detecting threats, while cyber resilience encompasses the organization's ability to maintain and restore operations before, during, and after a disruption—making the CIO's role in operational continuity and technology governance central to resilience, not just the CISO's role in threat management.
How should a CIO present cyber risk to a non-technical board?
Effective CIO reporting translates technical risk into business impact—operational downtime, financial exposure, regulatory consequence—and shows what has changed since the last briefing. Skip the jargon; present trend-based information the board can act on, connecting technology risk directly to business outcomes.