Introduction
Boards now face enforceable personal liability for cyber risk oversight. Since September 2023, SEC Rule 33-11216 requires public companies to disclose board cyber oversight in annual 10-K filings and report material incidents within four business days on Form 8-K.
Delaware courts are expanding Caremark liability to treat cybersecurity failures as "mission-critical" risks demanding heightened board attention. The SolarWinds enforcement action — in which the SEC personally sued the CISO — signals that regulators treat gaps between internal knowledge and external disclosure as potential fraud.
Yet despite increased regulatory pressure, boards are getting worse at governing cybersecurity. The World Economic Forum found only 2% of organizations have implemented firm-wide cyber resilience. Attention isn't the issue. The gap is between what gets reported and what actually enables governance.
Why Most Cyber Metrics Aren't Built for the Boardroom
Most cybersecurity reporting to boards consists of operational data—patch coverage percentages, vulnerability counts, mean time to detect—that describes activity without enabling oversight. Directors receive trivia when they need signal.
The NACD's 2026 Director's Handbook identifies a "material governance gap" created when boards defer to a single cybersecurity expert: if the expert nods, the board proceeds to the next agenda item. This undermines collective oversight duties under Caremark-related case law.
The Translation Gap
Raw technical scores don't tell directors what they need to know:
- CVSS ratings measure vulnerability severity in technical terms but explicitly exclude monetary losses, customer counts, or business impact
- Ticket volumes show security team workload, not organizational exposure
- Open finding counts describe backlog, not whether critical assets are protected
These metrics answer "what is the security team doing?" Directors need answers to different questions: "How exposed are we?" and "What decisions do we need to make?"
That distinction points to a governing principle.
The Core Principle
Board-facing cybersecurity metrics must enable governance functions—setting risk appetite, allocating resources, providing oversight—not substitute for management-level monitoring. Boards need clarity on risk, accountability, and decisions; operators need execution details. Those are different jobs, and conflating them produces reports that serve neither audience.
Reporting built around this distinction gives directors something to act on—not just something to acknowledge.
The Five Categories of Metrics Every Board Should Track
The NACD's 2026 Director's Handbook establishes a five-category framework for board-level cyber metrics: (1) Threat Environment, (2) Financial Loss Exposure, (3) Cyber Risk Profile and Maturity, (4) Supply Chain and Third-Party Exposure, and (5) Investment and Business Decision Alignment. How deeply each category is reported depends on the organization's size, industry, and risk profile.
Threat Landscape and Quantified Financial Exposure
Board threat briefings should answer three questions in plain language:
- What are the top threats facing our industry this quarter?
- What have peer organizations experienced?
- Have emerging threats—ransomware variants, AI-assisted attacks, zero-day exploitation—materially changed our exposure?
The answer should never be a CVE list. According to Verizon's 2024 Data Breach Investigations Report, ransomware is the top threat across 92% of industries. The WEF Global Cybersecurity Outlook 2026 reports 94% of respondents identify AI as a driver of cybersecurity change, with 87% calling AI-related vulnerabilities the fastest-growing risk.
Expressing risk in financial terms matters because boards govern best when they can act on it. The FAIR Institute's Factor Analysis of Information Risk (FAIR) — the only international standard quantitative model for operational risk — translates exposure into probability percentages and dollar ranges, rather than the color charts and numerical scales that dominate most security reports.
The NACD Handbook directs boards to request "quantitative risk models that measure ransomware impacts in dollars and probabilities." A "10% annual probability of ransomware with $2M–$8M loss exposure" prompts a governance decision. A "high severity red rating" rarely does.
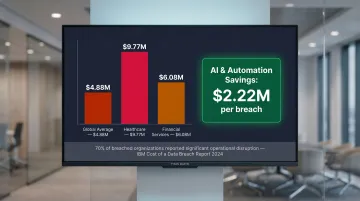
IBM's Cost of a Data Breach 2024 report gives boards the benchmarks needed to assess whether current security investment aligns with actual financial exposure:
- Global average breach cost: $4.88M (10% increase year-over-year)
- Healthcare industry: $9.77M (most expensive for 14 consecutive years)
- Financial services: $6.08M
- Organizations using AI/automation saved $2.22M per breach
- 70% of breached organizations reported significant disruption
Risk Profile, Third-Party Exposure, and Investment ROI
Boards should see how the organization benchmarks against NIST CSF, CIS Controls, or CMMC—validated by an independent third party—and critically, whether that score is improving over time. Trend lines matter more than point-in-time ratings because they reveal whether management's investments are working.
NIST CSF 2.0 defines four implementation tiers:
- Tier 1 — Partial: Ad hoc and reactive, with no consistent processes
- Tier 2 — Risk Informed: Management is aware of risk but processes remain limited
- Tier 3 — Repeatable: Formal policies in place with regular review cycles
- Tier 4 — Adaptive: Continuous improvement with predictive and proactive capabilities
Movement between tiers—and the timeline for that movement—tells the governance story.
Third-party and supply chain risk has moved squarely into board territory. The data explains why:
- Verizon's 2025 DBIR reports third-party involvement in breaches doubled from 15% to 30% in one year
- The NACD Handbook cites a 431% surge in supply chain attacks
- WEF data shows 65% of large companies identify supply chain vulnerabilities as their greatest challenge
- Only 27% simulate cyber incidents with ecosystem partners
- Only 33% map their ecosystem in detail
Given that exposure, boards should be asking for four specific data points:
- Which vendors carry the highest cyber risk to the organization
- Estimated financial impact of a significant third-party breach
- Whether vendor mitigation requirements are measurably reducing risk
- Third-party risk concentration (how many critical dependencies exist on single vendors)
On the investment side, boards should track which controls deliver the greatest risk reduction per dollar and which are underperforming. Two benchmarks worth anchoring this conversation:
- Security technology ROI: Organizations using AI and automation extensively saved $2.22M per breach versus those without it (IBM, 2024)
- Cyber insurance adequacy: The NACD Handbook instructs boards to "oversee a coordinated review of all cyber-relevant policies, including D&O and standalone cyber insurance," validated annually against current risk conditions

Having cyber insurance isn't the question. Whether policy limits match your quantified risk exposure is.
Translating Technical Data Into Business-Ready Risk Statements
Every metric presented to the board should pass the "so what" test: what does this mean for the business, and what decision or oversight action does it inform? A metric that cannot answer these questions belongs in management reporting, not board presentations.
The "What Changed" Principle
Instead of presenting snapshots, each briefing should anchor to the prior one: "Our estimated financial exposure to ransomware has shifted since last quarter, and here is why."
Boards need to see movement and causality, not isolated data points. This means:
- Comparing current quarter metrics to previous quarter
- Explaining what drove changes (new controls deployed, threat landscape evolution, business expansion)
- Indicating whether movement is favorable or requires action
Applied consistently, this approach turns a static dashboard into a governance tool—one the board can act on rather than simply receive.
Risk Appetite Alignment
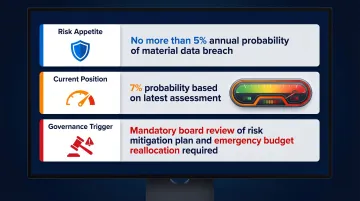
Metrics only become meaningful oversight tools when tied to board-approved risk thresholds. When a metric exceeds pre-agreed tolerance, it triggers a governance response—a decision, resource allocation, or formal escalation—not just a note in the management deck.
Example structure:
- Risk appetite: No more than 5% annual probability of material data breach
- Current position: 7% probability based on latest assessment
- Governance trigger: Exceeded threshold requires board review of mitigation plan and budget allocation
The Translation Function
Boards get the most from cybersecurity metrics when a senior advisor or fractional CISO bridges the gap between technical teams and the boardroom. That role produces a stable dashboard focused on trend and risk posture—not operational noise.
Done well, this translation layer connects cyber exposure directly to what boards are accountable for:
- Revenue protection and financial exposure
- Customer trust and brand reputation
- Regulatory compliance and legal liability
- Operational continuity under adverse conditions
What a Board-Level Cyber Dashboard Actually Looks Like
A well-constructed cyber dashboard holds five to seven stable KPIs, organized by risk domain: threat environment, control effectiveness, financial exposure, and compliance posture. Each metric shows current status and directional trend — and stays consistent quarter over quarter so directors can actually track progress.
Dashboard Structure
Leading dashboards include:
Threat Environment Domain:
- Top 3 industry-specific threats this quarter
- Peer breach incidents with business impact
- Emerging threat assessment (stable vs. elevated vs. critical)
Financial Exposure Domain:
- Quantified annual loss expectancy by scenario (ransomware, data breach, business disruption)
- Cyber insurance coverage vs. quantified exposure gap
- Estimated cost of current unmitigated risks
Control Effectiveness Domain:
- Maturity tier (NIST CSF 1-4) with trend direction
- Mean time to detect and contain incidents
- Critical system patch compliance rate
- Backup recovery test success rate
Third-Party Risk Domain:
- Vendor risk concentration score
- High-risk vendor count and mitigation status
- Third-party assessment completion rate
Compliance and Governance Domain:
- Regulatory compliance posture (SEC, industry-specific)
- Incident response plan test date and results
- Board-approved risk exceptions and status

Reporting Cadence
A dashboard is only useful if it's reviewed on a rhythm directors can rely on. The NACD Handbook recommends substantive cyber briefings at least quarterly, with at least one annual deep-dive into overall risk posture. WEF research shows 99% of highly resilient organizations report board involvement in cybersecurity, with 52% receiving regular updates.
Structure should remain consistent across quarters so directors develop literacy over time.
Why Dashboards Fail
Common failure modes:
- Rotating 30+ metrics each quarter with no consistent baseline to compare against
- Technical language presented without business context or dollar-denominated consequences
- Metrics disconnected from the board's approved risk appetite thresholds
- No clear ask — directors leave without knowing what decision or endorsement is needed
Pre-Defined Escalation Thresholds
The most defensible dashboards include agreed trigger points — specific metric thresholds that automatically escalate an issue to board awareness or decision-making. This draws a clear line between what management watches daily and what requires a board decision.
Example: "Any incident affecting more than 100,000 customer records automatically triggers board notification within 24 hours, regardless of whether materiality determination is complete."
The Questions Every Board Director Should Be Asking
The NACD's 2026 Director's Handbook establishes six core principles for board cyber oversight, each generating specific governance questions:
Foundational Governance Questions
Risk Appetite and Crown Jewel Protection:
- What is our cyber risk appetite expressed in financial terms, and are we tracking within it?
- Which assets are our "crown jewels," and how is their protection validated?
- Has our risk posture improved or deteriorated since the last briefing, and why?
Investment and ROI Oversight:
- Which controls are delivering the most risk reduction per dollar invested?
- Which security investments are underperforming or redundant?
- Does management model the direct and indirect costs of cyber incidents in empirical and economic terms?
These investment questions keep the board focused on outcomes — not tool counts or headcount — while leaving execution accountability with management.
Incident Preparedness and Escalation Governance
Critical questions before an incident occurs:
- Has the organization tested its incident response and disclosure plan?
- Does the board have a defined role during a significant cyber event, distinct from management's operational response?
- Who has authority to decide whether to pay a ransom, and under what circumstances is that decision elevated to the board?
The NACD Handbook emphasizes that leading boards participate in scenario exercises and tabletop simulations that test decision-making under stress. WEF data shows only 27% of organizations simulate cyber incidents or plan recovery exercises with ecosystem partners—a significant preparedness gap.
Third-Party and Emerging Risk Questions
- Can management confidently identify our most critical dependencies, including key fourth parties, which could put us at risk?
- Are our AI systems hardened against cyber attacks such as prompt injections, data poisoning, and jailbreaking?
- Are we regularly reviewing our cyber strategy to ensure management is identifying, measuring, and mitigating cyber risk in every business vertical?
WEF research links board accountability to resilience outcomes directly: 30% of highly resilient organizations report board members hold personal liability for cyber breaches, compared to only 9% of insufficiently resilient organizations. That gap suggests accountability structures — not just security budgets — are a material driver of organizational resilience.
Frequently Asked Questions
What cybersecurity metrics should be reported to the board?
Boards should receive metrics in five strategic categories: threat environment (top industry threats and peer incidents), quantified financial exposure (dollar-denominated loss scenarios), program maturity (NIST/ISO benchmarking with trend), third-party risk (vendor concentration and exposure levels), and investment ROI (risk reduction per dollar spent)—each framed in business terms, not technical outputs.
Is a CVSS score of 9.8 considered critical?
A CVSS score of 9.8 is technically classified as critical, but raw CVSS scores are not appropriate board-level metrics. The scoring system explicitly excludes monetary losses, customer impact, and business context. Technical severity must be translated into financial and operational risk before it reaches the board.
How often should cybersecurity metrics be reported to the board?
Boards should receive substantive cyber risk updates at least quarterly, with one annual deep-dive into overall posture. Material incidents or significant risk changes require immediate reporting — the SEC's four-day disclosure rule makes a defined escalation path non-negotiable.
What is the difference between operational and board-level cybersecurity metrics?
Operational metrics (patch rates, ticket counts, vulnerability counts) describe what the security team is doing—they measure activity and workload. Board-level metrics describe the organization's risk exposure, posture trend, and alignment to risk appetite—they enable governance decisions like resource allocation and risk acceptance rather than management execution.
What questions should board directors ask about cybersecurity risk?
Directors should press on five areas:
- What is our cyber risk appetite in financial terms, and are we within it?
- Which assets are most critical, and how is their protection validated?
- Are our cyber investments measurably reducing exposure?
- Do we have tested escalation and disclosure plans with clear board versus management roles?
- Which third-party dependencies create concentrated risk?