Introduction: Healthcare Cybersecurity Strategy in 2026
Healthcare is not just the most-targeted sector by cybercriminals — it's the most consequential. A breach in healthcare isn't merely a data problem. It's an operational crisis that delays procedures, diverts ambulances, cancels chemotherapy, and creates years of legal exposure. According to IBM's 2025 Cost of a Data Breach Report, healthcare breaches cost an average of $7.42 million — the highest of any industry for the 14th consecutive year.
Most healthcare organizations spend heavily on security tools and still get breached. The problem is strategy, governance, and decision-making — not the technology stack. Boards rubber-stamp briefings they don't understand. Executives delegate cybersecurity entirely to IT. No one owns the outcome when things go wrong.
This guide is written for boards and executive teams, not IT departments. It covers the 2026 threat landscape, governance requirements, the compliance-security gap, and how to build a roadmap with named owners and measurable outcomes — so accountability is clear before the next incident.
TLDR: Key Takeaways
- Healthcare remains the costliest sector for breaches, driven by high-value PHI, legacy systems, and connected medical devices
- HIPAA compliance is a floor, not a ceiling — compliant organizations still get breached
- Boards and C-suite must own cybersecurity as governance, not delegate it entirely to IT
- Effective strategy balances proactive prevention with tested incident response capability
- Organizations that survive breaches share one trait: someone at the top owned the outcome before the incident happened
Why Healthcare Is the #1 Target for Cybercriminals
Healthcare attracts attackers for three structural reasons:
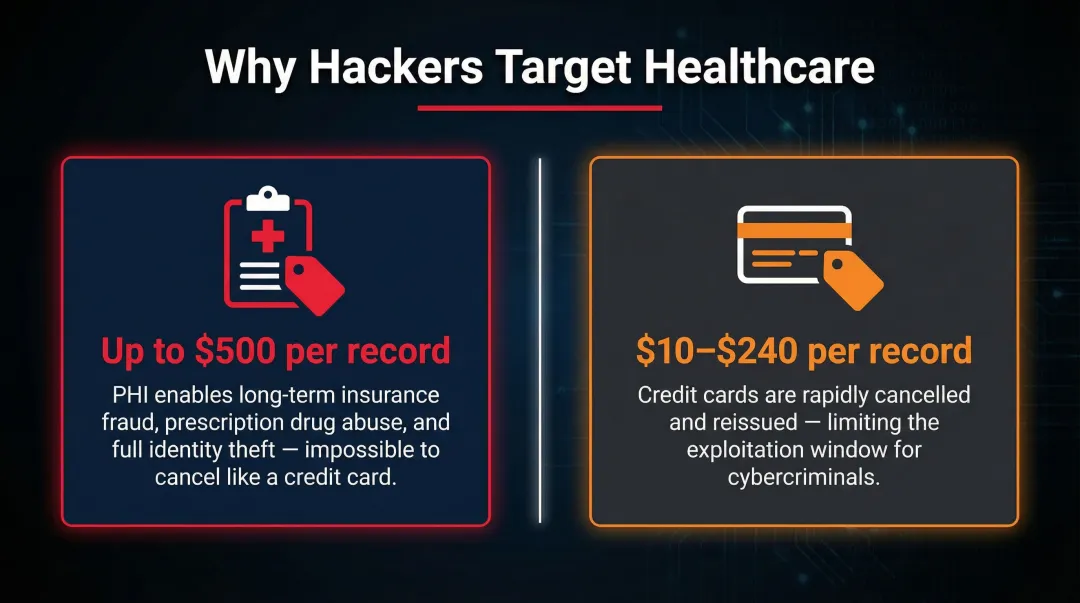
1. Protected Health Information (PHI) commands extraordinary dark web value
Medical records sell for up to $500 on underground markets, compared to just $10–$240 for credit card details. Why? PHI enables complex insurance fraud, identity theft, and extortion schemes that credit cards cannot.
2. Healthcare is critical infrastructure
Organizations restore operations at any cost when lives are at stake. This willingness to pay ransoms — combined with operational downtime that threatens patient safety — makes healthcare especially vulnerable to extortion-based attacks.
3. Sprawling, mixed-age IT environments expose more entry points
Healthcare networks integrate decades-old imaging systems, modern EHRs, third-party billing platforms, and connected medical devices — each with different security standards and patch cycles.
The Internet of Medical Things (IoMT) Vulnerability
Networked infusion pumps, imaging systems, patient monitors, and clinical devices often run outdated firmware, lack encryption, or are managed by third-party vendors. According to Claroty's 2025 analysis of over 2.25 million IoMT devices, 99% of healthcare organizations have connected medical devices with Known Exploited Vulnerabilities (KEVs). Worse, 8% of imaging systems carry KEVs linked to ransomware and are insecurely connected online.
Financial and Operational Impact
Breaches don't just trigger regulatory penalties. In April 2026, Signature Healthcare in Massachusetts suffered a cyberattack that forced Brockton Hospital to divert ambulances and cancel chemotherapy infusion services. The incident brought down electronic medical records, forcing staff to revert to pen-and-paper documentation.
When a cyberattack cancels chemotherapy and diverts ambulances, it stops being a security operations problem. Boards and executive teams own the response — and the liability that follows.
The Most Dangerous Threats Facing Healthcare in 2026
Ransomware Remains the Dominant Threat
Modern ransomware gangs use double extortion: encrypt systems and exfiltrate data. According to the FBI's Internet Crime Complaint Center (IC3), healthcare was the most targeted critical infrastructure sector in 2025, with 278 ransomware attacks tracked.
One vendor breach now exposes dozens of healthcare organizations simultaneously — and the tactics have shifted. Sophos's 2025 State of Ransomware in Healthcare report shows data encryption dropped to 34%, but extortion-only attacks tripled to 12%. Attackers now threaten to publish stolen data without ever encrypting a system.
Social Engineering and Phishing Grow More Sophisticated
Phishing remains the most common initial access point into healthcare systems — and it's getting harder to defend against. The 2024 HIMSS Healthcare Cybersecurity Survey confirms phishing as a leading cause of compromise, and the 2025 Verizon Data Breach Investigations Report notes attackers now pair social engineering with direct vulnerability exploitation.
What's changed is the sophistication of the lure:
- AI-generated phishing emails mimic internal communications with near-perfect accuracy
- Voice cloning (vishing) impersonates executives or IT staff to bypass verbal verification
- Business email compromise (BEC) manipulates finance and HR teams into fraudulent transfers or credential handoffs
Training alone no longer closes the gap. Process controls and technical safeguards have to carry more of the load.
Supply Chain and Third-Party Risk
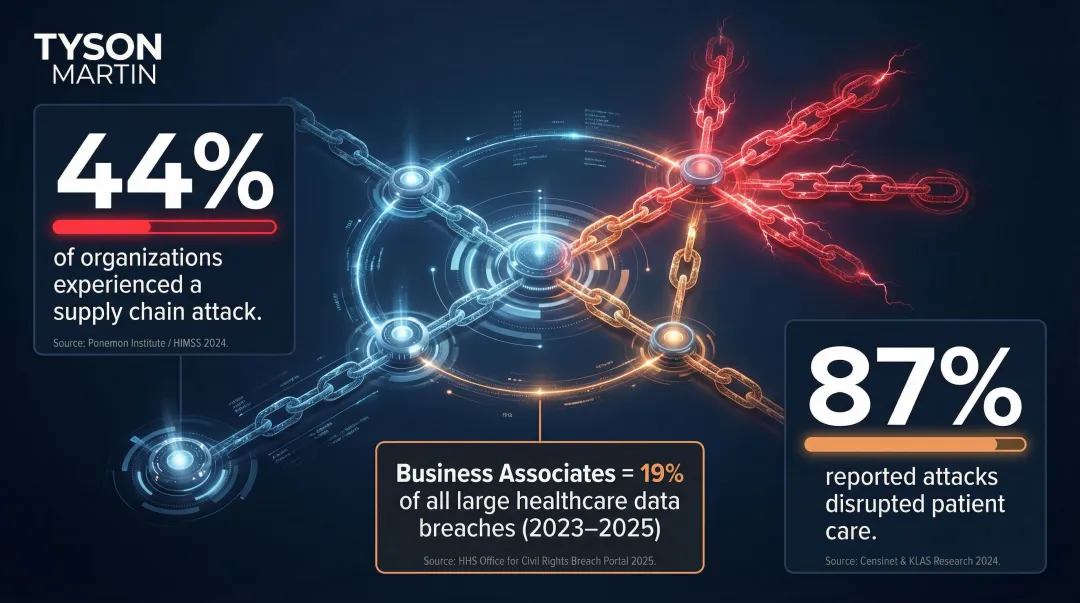
Healthcare organizations are increasingly breached through vendors, clearinghouses, and business associates. Between 2023 and 2025, Business Associates accounted for 419 of the 2,198 large healthcare data breaches reported to HHS OCR — 19% of total incidents.
The 2025 Ponemon Healthcare Cybersecurity Report found that 44% of organizations experienced a supply chain attack, and 87% of those reported that the attack disrupted patient care.
Core Elements of a Healthcare Cybersecurity Strategy
A security program accumulates tools and policies. A security strategy connects risk decisions to business priorities, allocates resources against the highest-impact exposures, and creates accountability from the board down. That distinction determines whether your organization responds to threats or reacts to them.
Risk Assessment as the Foundation
Healthcare organizations should conduct regular, structured risk assessments against recognized frameworks: NIST CSF 2.0, HIPAA Security Rule requirements, and HHS Cybersecurity Performance Goals. The output should be a prioritized risk register, not a compliance checklist.
A good risk assessment produces:
- Ranked vulnerabilities by severity and business impact
- Clear ownership of each risk and mitigation action
- Resource allocation decisions based on highest-impact exposures
- Board-ready risk posture summary with trends, not trivia
This differs from a compliance audit, which checks whether controls meet a standard at a point in time. A risk assessment forces decisions: which weaknesses matter to the business, and what to do first.
Proactive Controls That Matter Most
High-ROI control categories:
- Multi-factor authentication (MFA) across all systems
- Privileged access management to limit admin credentials
- Network segmentation between clinical and administrative systems
- Email filtering to block phishing and malicious attachments
Employee Security Awareness Training
Annual training is insufficient. The HHS 405(d) Health Industry Cybersecurity Practices (HICP) recommends continuous campaigns, including monthly simulated phishing tests. The January 2025 HIPAA Security Rule NPRM proposes requiring training at least once every 12 months, plus ongoing reminders of security responsibilities and relevant threats.
In healthcare, clinical staff are often the highest-risk population. They need role-specific training, not generic modules.
Incident Response Planning
An untested incident response plan is just a document. Tabletop exercises — run at least annually — are what turn it into a capability. Each exercise should validate four core roles:
- Incident Manager — owns the response timeline and decisions
- Technical Lead — directs containment and investigation
- Communications Lead — manages internal and external messaging
- Legal/Compliance — advises on notification obligations and liability
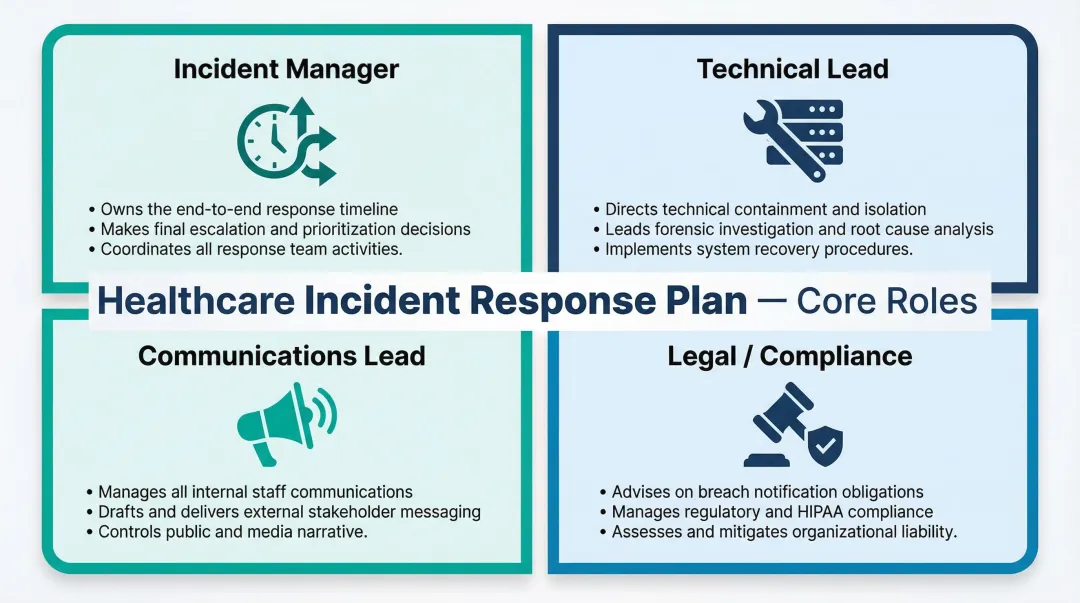
Printed contact lists matter too. When systems go offline, digital runbooks disappear. The board should receive a briefing on tabletop outcomes — not just confirmation that the exercise happened.
Backup and Recovery
Air-gapped backups remain a primary ransomware defense — but only when tested through actual restoration drills, not just backup confirmation. Organizations should verify they can restore critical systems within defined recovery time objectives. In healthcare, regulators and insurers increasingly expect documented RTOs, with many critical systems targeting recovery within 4–24 hours.
The Board's Role in Healthcare Cybersecurity Governance
Most healthcare boards either rubber-stamp IT security updates they don't understand or avoid the topic altogether. Neither is defensible. Regulatory pressure is making board-level accountability explicit. The SEC's 2023 Final Rule requires public companies to disclose material incidents within four business days and report on board oversight of cyber risk annually.
What the Board Should Own vs. Delegate
The board owns:
- Risk appetite (what exposures are tolerable, what aren't)
- Escalation thresholds (when management must brief the board)
- Accountability for material failures
Management owns execution — that division of responsibility needs to be explicit and documented.
In practice, this means the board should ask:
- Is our risk posture improving or worsening?
- Does management have adequate resources?
- Are decision rights clear — who can accept risk, who escalates?
- What changed since the last briefing?
The board should not ask for technical details on firewall configurations or vulnerability scan results.
What Good Cybersecurity Reporting to the Board Looks Like
Effective board reporting includes:
- Plain-English risk posture summary
- What changed since the last briefing
- Trend data (not trivia)
- Clear flags for decisions requiring board-level input
Contrast this with typical IT security briefings that give the board 40 slides of data but no clear action or decision point.
C-Suite Accountability
CEOs, COOs, and General Counsel must recognize cybersecurity as a business risk — not an IT problem. C-suite leaders should approve the cybersecurity roadmap, ensure adequate resourcing, and hold third-party vendors accountable through contract terms and audit rights.
The Fractional/Interim CISO Model as a Governance Solution
Many mid-size healthcare organizations don't need (or can't afford) a full-time CISO. But they do need someone who can translate risk into board-ready language, build the governance structure, and move from plan to action quickly.
Fractional or interim CISO engagements deliver stability, clear oversight, and a 90-day executable plan. This model addresses the governance gap by providing senior security leadership with authority and decision rights — not just technical staffing or operational support.
Compliance Is Not a Strategy: HIPAA and the 2026 Regulatory Landscape
HIPAA sets a legal minimum. Organizations that are "compliant" can still be breached. The HIPAA Security Rule requires a risk analysis but does not prescribe specific technical controls, leaving significant gaps that attackers routinely exploit. The HIPAA Security Rule requires a risk analysis but does not prescribe specific technical controls, leaving significant gaps that attackers routinely exploit. That gap is now closing — at least on paper.
Proposed HIPAA Security Rule Updates
Published in the Federal Register on January 6, 2025, the HHS OCR Notice of Proposed Rulemaking (NPRM) seeks to modernize the HIPAA Security Rule. Key proposed mandates include:
| Provision | Requirement |
|---|---|
| Multi-Factor Authentication (MFA) | Expressly requires deployment across all technology assets |
| Encryption | Requires encryption of ePHI at rest and in transit, with limited exceptions |
| Vulnerability Management | Requires scanning at least every six months and penetration testing at least annually |
| Contingency Planning | Establishes procedures to restore systems and data within 72 hours |
| Risk Analysis & Audits | Requires written risk assessment and compliance audit at least once every 12 months |
The NPRM grounds these mandates in hard data. 2016-2017 OCR audits found only 14% of covered entities and 17% of business associates were adequately performing ePHI risk analysis — the most basic Security Rule requirement.
Broader Regulatory Direction
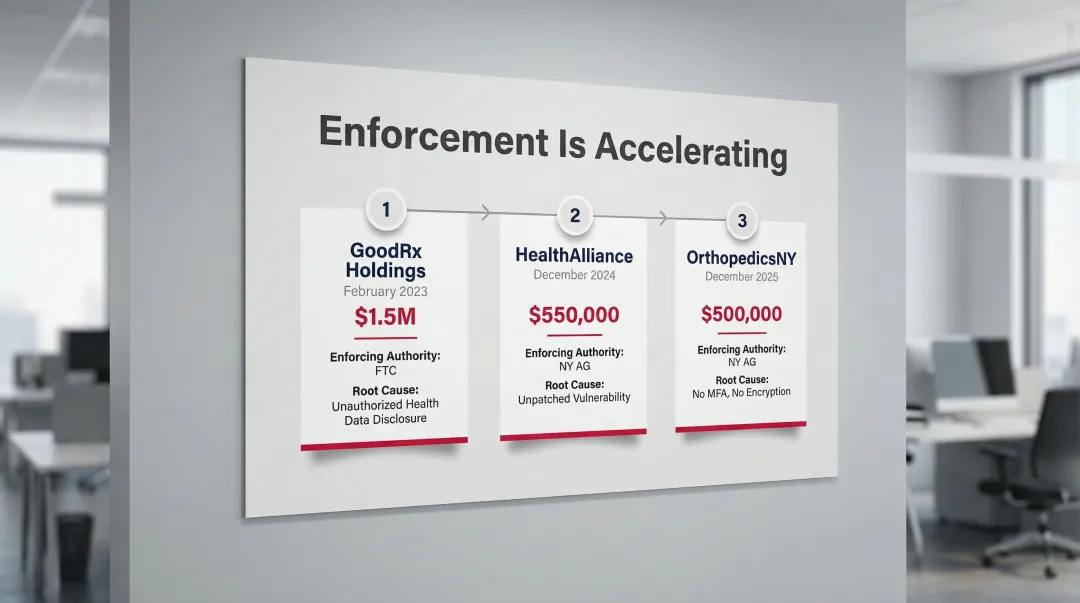
Federal proposals aren't the only pressure point. State attorneys general are moving faster than Congress, and enforcement is targeting the same foundational failures: no MFA, unpatched vulnerabilities, and unencrypted data. Recent actions make the stakes concrete:
- $500,000 penalty — OrthopedicsNY (Dec 2025): No MFA for remote access, no encryption — 656,000 records exposed. NY Attorney General.
- $550,000 penalty — HealthAlliance (Dec 2024): Known vulnerability left unpatched, 242,641 patient records breached. NY Attorney General.
- $1.5 million civil penalty — GoodRx Holdings (Feb 2023): Unauthorized disclosure of health information to Facebook and Google. FTC enforcement.
Building Your Healthcare Cybersecurity Roadmap
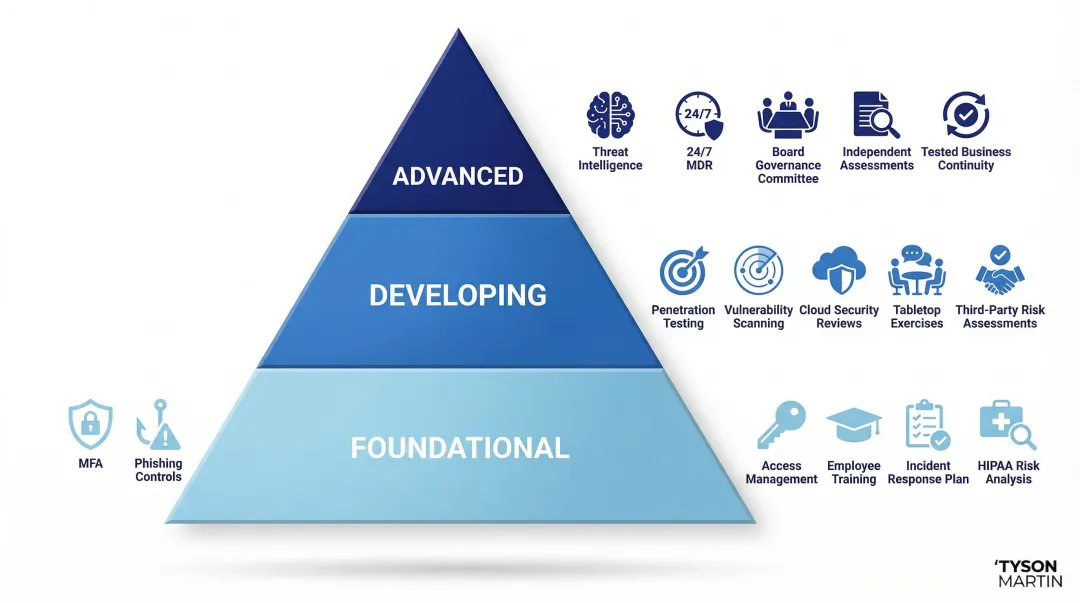
Healthcare organizations are at different starting points. A 10-physician practice and a regional health system have different resources and risk profiles. A maturity-tiered approach respects this reality. Start where you are, not where you wish you were.
Foundational Tier
- MFA across all systems
- Phishing-resistant email controls
- Basic access management
- Employee awareness training
- Documented (not imagined) incident response plan
- HIPAA-aligned risk analysis
These controls address the most common attack vectors. According to CISA, using MFA makes organizations 99% less likely to be hacked. Yet the 2024/2025 Ponemon Study found only 49-54% of healthcare organizations are using MFA to reduce email-based attacks.
Developing Tier
- Penetration testing on a regular cadence
- Vulnerability scanning (at least every six months)
- Cloud security configuration reviews (Microsoft 365 and EHR platforms are common weak points)
- Tabletop exercises
- Formalized third-party risk assessments for key vendors
Advanced Tier
- Threat intelligence integration
- 24/7 monitoring or managed detection and response (MDR) partnership
- Board-level governance structure with a security committee
- Annual independent assessments
- Tested business continuity plan that accounts for full system outages
The Execution Gap
Most healthcare organizations have strategies on paper that never get implemented because no one owns the outcomes. The 2025 Ponemon Healthcare Cybersecurity Report found that 93% of surveyed organizations experienced at least one cyberattack in the past 12 months, with an average of 43 attacks per organization. Nearly three-quarters (72%) reported these attacks disrupted patient care.
A 90-day plan with named owners and measurable milestones — reviewed by leadership, not just IT — separates organizations that improve from those that just document.
Frequently Asked Questions
How does cybersecurity work in healthcare?
Healthcare cybersecurity involves the policies, technologies, and governance practices used to protect patient data (PHI), clinical systems, and medical devices from unauthorized access, disruption, or theft — while ensuring care delivery continues uninterrupted.
What are the 5 C's of cybersecurity?
The 5 C's are Change, Compliance, Cost, Continuity, and Coverage. In healthcare, each carries patient safety implications:
- Change — managing updates without disrupting care delivery
- Compliance — meeting HIPAA and other regulatory mandates
- Cost — balancing security investment against operational budgets
- Continuity — keeping operations running during and after incidents
- Coverage — protecting all systems, devices, and data assets
What is the biggest cybersecurity threat to healthcare organizations in 2026?
Ransomware — especially double-extortion variants targeting third-party vendors — remains the highest-impact threat. AI-assisted phishing amplifies that risk by making social engineering attacks more convincing and far more difficult to catch before damage is done.
How should a healthcare board oversee cybersecurity without getting into technical weeds?
Boards should focus on risk appetite, escalation thresholds, and trend-based reporting. Ask whether the organization's risk posture is improving, whether management has adequate resources, and whether decision rights are clear — rather than evaluating technical controls directly.
How does HIPAA compliance relate to cybersecurity strategy?
HIPAA sets a legal minimum for PHI protection but does not guarantee security. Organizations can be fully compliant and still suffer a major breach, which is why a mature cybersecurity strategy goes beyond checkbox compliance.
What should a healthcare organization do immediately after discovering a cyberattack?
Activate the incident response plan immediately: isolate affected systems, notify legal counsel and relevant leadership, and preserve forensic evidence. Organizations without a pre-tested plan routinely lose critical hours in those first moments — time that directly affects containment outcomes.