Introduction
Enterprise IoT is no longer a technology problem—it is a board-level risk problem. Connected devices embedded in supply chains, retail operations, manufacturing floors, and critical infrastructure mean a breach in one sensor, camera, or building automation controller can cascade across the entire enterprise. When 75% of businesses suffered an IoT security breach in the past 12 months, that risk is material, measurable, and still underweighted in most board agendas.
What has changed heading into 2026? The attack surface now spans 19.8 to 22.3 billion connected devices globally, yet the average U.S. enterprise scores just 35.9 out of 50 for operational technology security maturity. Attackers are moving faster—the median time from vulnerability publication to active exploitation has collapsed to five days.
Regulatory pressure has followed. The EU Cyber Resilience Act, NIST CSF 2.0, and Executive Order 14028 have converted IoT security gaps into legal and financial exposure that boards can no longer treat as an IT problem.
This post covers each of those dimensions: threat vectors, the five pillars of a defensible program, compliance obligations, and what board-level governance actually looks like when it works.
TLDR
- Enterprise IoT attack surfaces have expanded to 19.8–22.3 billion devices globally, with 75% of businesses breached via IoT in the past year
- Firmware supply chains and router botnets now threaten enterprise infrastructure directly—attackers weaponize devices before they leave the factory
- Five pillars define a defensible strategy: device visibility, Zero Trust enforcement, firmware integrity, behavioral monitoring, and IoT-specific incident response
- EU Cyber Resilience Act fines reach €15M or 2.5% of global revenue, with NIST 2.0 and EO 14028 adding contractual and regulatory exposure
- Boards must own IoT risk with clear decision rights, stable trend metrics, and 90-day remediation plans—not rely on technical teams to self-govern
Why 2026 Is a Turning Point for Enterprise IoT Security
The global IoT attack surface reached 19.8 to 22.3 billion connected devices in 2025, according to authoritative projections from Statista and Ericsson, with cellular and short-range enterprise connections driving continuous expansion. Yet 75% of businesses suffered an IoT security breach in the past 12 months, with 76% attributing project failures to device-level vulnerabilities. The gap between device proliferation and security maturity has never been wider.
The historical boundary separating operational technology from enterprise IT has collapsed. Industrial sensors, building automation systems, retail point-of-sale terminals, and supply chain devices now share network infrastructure with enterprise IT, creating lateral movement pathways attackers exploit systematically. What once lived in isolated OT environments is now addressable from the corporate network. Attackers have noticed.
Botnets are evolving beyond consumer routers into enterprise infrastructure. Bitdefender's 2025 IoT Security Landscape Report forecasts that future botnets will integrate EV chargers, smart inverters, and industrial controllers. Cloudflare already recorded a 31.4 Tbps DDoS attack in Q4 2025 launched by the Aisuru-Kimwolf botnet, comprising 1–4 million infected devices, primarily Android TVs. When enterprise IoT devices join these botnets, they become weapons: directed at third parties, or turned against the enterprise's own connectivity.
Firmware supply chains have become ground zero for 2026 attacks. Attackers target shared SDKs and firmware components upstream, meaning a single compromised library propagates silently across entire product ecosystems. The BADBOX 2.0 campaign infected over 1 million off-brand Android devices with factory-installed backdoors before reaching end-users, bypassing perimeter defenses entirely. The FBI confirmed the supply chain compromise in June 2025.
The financial exposure is documented. According to Claroty's 2024 Global State of CPS Security report, cyberattacks on cyber-physical systems carried measurable costs:
- 45% of organizations reported financial impacts of $500,000 or more in the past 12 months
- 27% reported losses exceeding $1 million
- Operational downtime, regulatory liability, and reputational damage are now direct line items — not backlog items for the security team
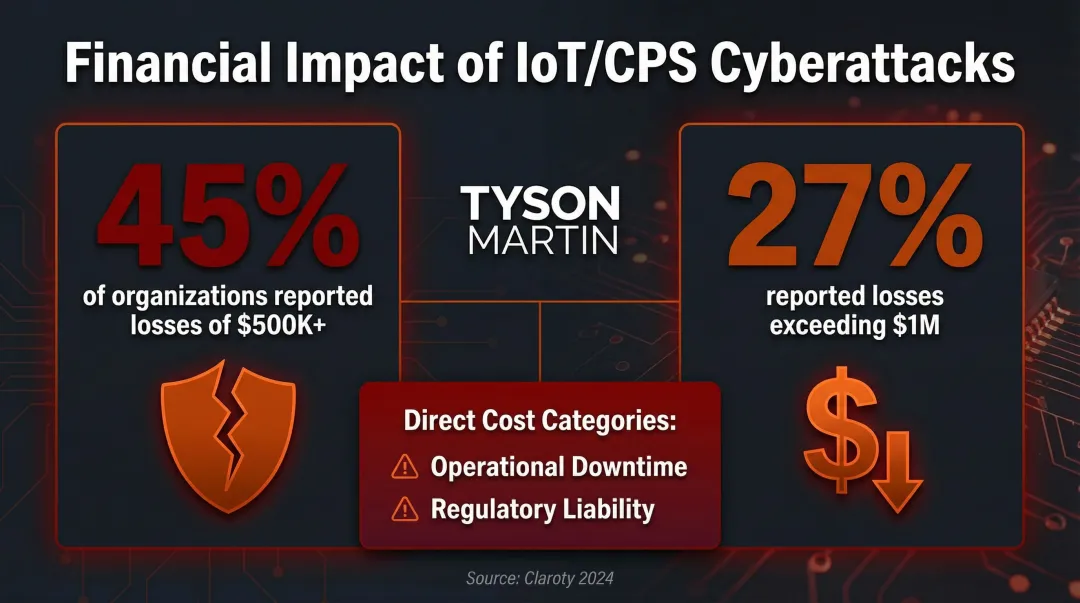
These figures belong on the enterprise risk register. IoT security is a board-level exposure, not a technical footnote.
The Threat Landscape Every Enterprise Leader Should Understand
The Unmanaged Device Problem
Routers and switches average 32 vulnerabilities per device and account for 34% of devices with the most critical vulnerabilities, according to Forescout's 2026 analysis. The core issue is visibility—organizations cannot defend what they cannot see. Shadow IoT devices installed by facilities teams, business units, or vendors sit outside formal asset management, creating entry points security teams never inventoried.
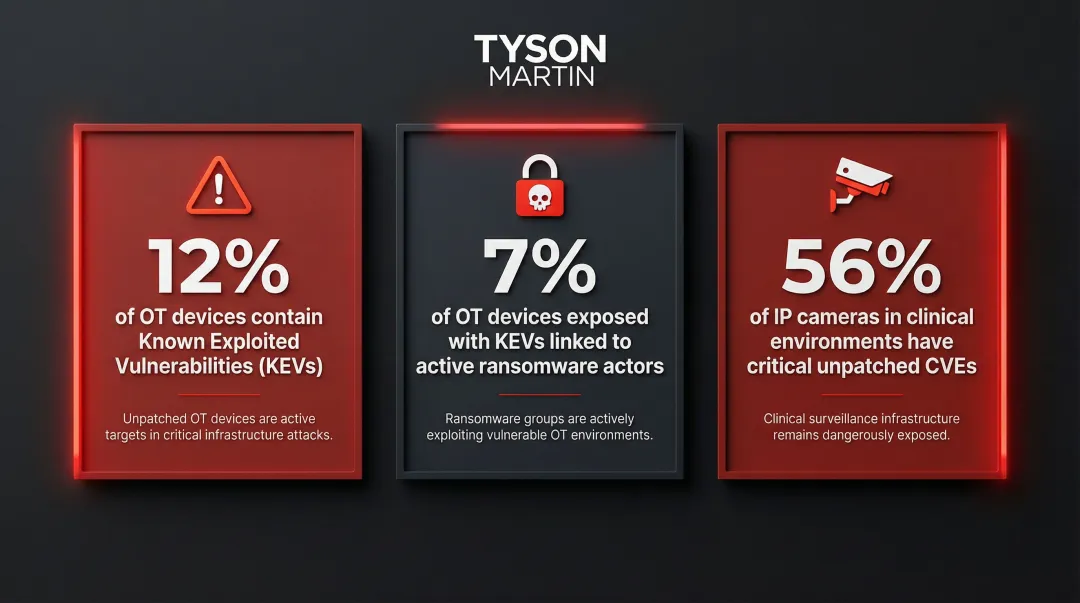
Key vulnerability statistics:
- 12% of analyzed OT devices contain Known Exploited Vulnerabilities (KEVs)
- 7% are exposed with KEVs linked to known ransomware samples and actors
- 56% of IP cameras in clinical environments have critical unpatched CVEs
IoT as the Unlocked Door
Attackers rarely target IoT devices as the end goal. Compromised cameras, smart plugs, routers, and industrial sensors serve as entry points for lateral movement into more critical systems, including OT environments.
The Volt Typhoon campaign illustrates how far that movement can reach: PRC state-sponsored actors exploited vulnerabilities in public-facing network appliances (routers, VPNs, firewalls), moved laterally to domain controllers, and pre-positioned themselves on VMware vCenter servers adjacent to OT assets like water treatment plants and electrical substations.
A distinct but related threat: UNC3886 deployed custom backdoors on Juniper Networks routers, targeting network authentication services to gain privileged initial access and long-term routing infrastructure control. IoT and network infrastructure devices are not endpoints—they are footholds.
The Persistent Patching Failure
Many IoT devices have multi-year or decade-long operational lifespans but receive security support for only a fraction of that period. The median time from vulnerability publication to active exploitation dropped to just 5.0 days in 2026, according to Rapid7's Global Threat Landscape Report. Meanwhile, 25% of high-risk vulnerabilities are immediately targeted for exploitation, with proof-of-concept code published the same day a vulnerability is disclosed.
Vendors routinely publish CVEs faster than they ship firmware updates, leaving enterprises exposed even when patching processes are mature. That gap turns procurement and vendor management into security functions, not just operational ones.
Supply Chain Attacks on Firmware Signing and OTA Services
Attackers routinely hijack updates by infiltrating vendor networks to insert malware into outgoing updates or by undermining code signing systems via self-signed certificates or compromised access controls. The Notepad++ update hijack in 2026 demonstrated how attackers compromised shared hosting servers, intercepting and redirecting update traffic to serve malicious manifests—succeeding because the updater failed to enforce certificate and signature verification.
For IoT, this means procurement teams must verify that vendors maintain cryptographically signed update mechanisms, staged rollouts, rollback capability, and continuous integrity verification—not manual, ad hoc patching cycles.
The Five Pillars of an Enterprise IoT Security Strategy
Pillar 1: Complete Device Visibility and Asset Inventory
You cannot protect what you cannot inventory. Enterprises must establish a continuously updated asset register covering every IP-addressable device on the network—including OT, building systems, and vendor-managed endpoints.
What this looks like in practice:
- Automated discovery tools that scan continuously, not quarterly
- Protocol-aware scanning that identifies industrial protocols (Modbus, BACnet, OPC-UA)
- Integration with existing configuration management databases (CMDBs)
- Ownership assignment for every device—facilities, IT, OT, or vendor-managed
Visibility must extend across the supply chain: knowing what firmware version a device runs, whether it still receives vendor support, and who is responsible for patching it are mandatory inputs to a defensible IoT security posture.
Pillar 2: Zero Trust Architecture for IoT
Zero Trust in the IoT context assumes every device is untrusted until continuously verified. This requires:
- Hardware-backed device identity using TPMs or X.509 certificates
- Micro-segmentation to contain blast radius and prevent lateral movement
- Policy enforcement that does not rely on perimeter-based assumptions
The default enterprise approach of placing IoT devices on shared networks with broad access has become indefensible in 2026, given lateral movement patterns documented in current threat intelligence. Organizations that lack the technical authority to implement micro-segmentation directly must establish governance structures that assign decision rights, define risk acceptance processes, and enforce policy exceptions with documented time limits. This is a governance problem as much as a technical one. Organizations navigating this without stable security leadership typically need someone who can translate architecture decisions into board-ready policy—the role a fractional CISO fills when permanent leadership isn't yet in place.
Pillar 3: Firmware Integrity and Patch Management
Organizations need a software bill of materials (SBOM) for IoT devices to know exactly what components are in their firmware and assess exposure when new vulnerabilities are disclosed. SBOM adoption remains immature: 48% of organizations produce SBOMs to some extent, and 46% consume them, but 43% expect to face an SBOM requirement in the next 24 months.
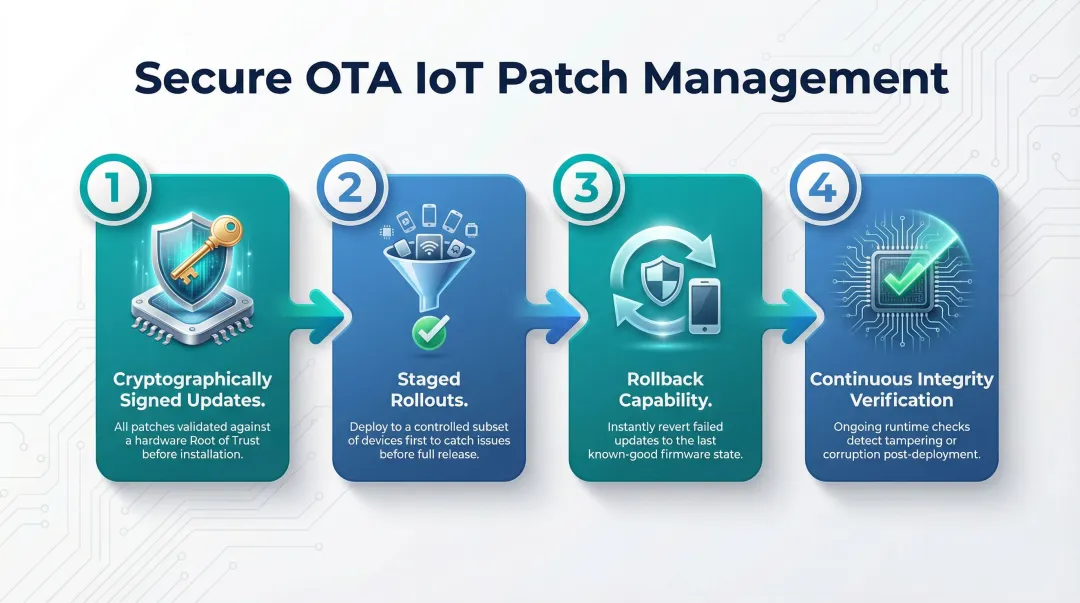
Good OTA patch management requires:
- Cryptographically signed updates anchored in a Root of Trust for Update (RTU), as mandated by NIST SP 800-193
- Staged rollouts to detect issues before full deployment
- Rollback capability if updates fail or introduce instability
- Continuous integrity verification to detect tampering
Pillar 4: AI-Driven Behavioral Monitoring and Threat Detection
Signature-based detection fails in IoT environments because devices communicate in predictable patterns that traditional tools cannot profile reliably. AI and machine learning enable behavioral profiling—flagging devices that suddenly initiate unexpected outbound connections or push anomalous data volumes.
IoT behavioral monitoring must feed into the enterprise SIEM/SOAR stack, not operate as an isolated tool. Threat detection is only useful if it triggers an actionable response within defined escalation thresholds.
Pillar 5: IoT-Specific Incident Response Planning
Generic cyber incident response plans break down for IoT. Isolating a compromised endpoint in IT is straightforward; isolating a compromised industrial controller or building automation device can halt physical operations entirely. IoT incident response must account for:
- Safety implications and operational continuity requirements before any isolation decision
- Vendor involvement and third-party remediation timelines that IT teams cannot control
- Physical access requirements for device isolation or firmware reimaging
Boards and leadership teams should have clarity on when an IoT-originated incident escalates to executive or board notification—this connects technical response to governance. Organizations building this structure for the first time often lack the translation layer between technical response protocols and what the board needs to hear—and act on—during an active incident.
Regulatory Obligations Shaping Enterprise IoT Strategy in 2026
Three regulatory developments create legal and financial exposure for organizations without mature IoT governance:
EU Cyber Resilience Act (CRA)
The CRA mandates security-by-design for connected products sold in the EU. Key milestones:
- Entry into force: December 10, 2024
- Reporting obligations apply: September 11, 2026 (manufacturers must notify actively exploited vulnerabilities to CSIRT and ENISA)
- Full application: December 11, 2027
Penalty structure: Non-compliance with essential cybersecurity requirements carries fines up to €15,000,000 or 2.5% of total worldwide annual turnover, whichever is higher. At that scale, IoT governance is a board-level financial obligation, not an IT compliance task.
NIST Cybersecurity Framework 2.0
On the US side, NIST CSF 2.0 raises the governance bar for domestic enterprises. Three changes matter most for IoT programs:
- Introduces a dedicated "Govern" function covering cybersecurity risk management strategy, policy, and expectations
- Elevates Cybersecurity Supply Chain Risk Management (C-SCRM) to its own category within that function
- Requires organizations to identify, establish, manage, and monitor supply chain risk processes — not just document them
Executive Order 14028 and OMB M-26-05
Where NIST CSF 2.0 sets the framework, federal procurement rules determine what vendors must actually deliver. In February 2026, OMB Memorandum M-26-05 rescinded the static "Common Form" secure software attestation requirement, directing federal agencies to adopt tailored, risk-based approaches to software and hardware security. The shift moves from compliance checklists to measurable security outcomes, with three specific deliverables now expected:
- Software Bill of Materials (SBOMs) for hardware and software components
- Vulnerability disclosure commitments from device manufacturers
- Supply chain transparency documentation as a baseline contract requirement
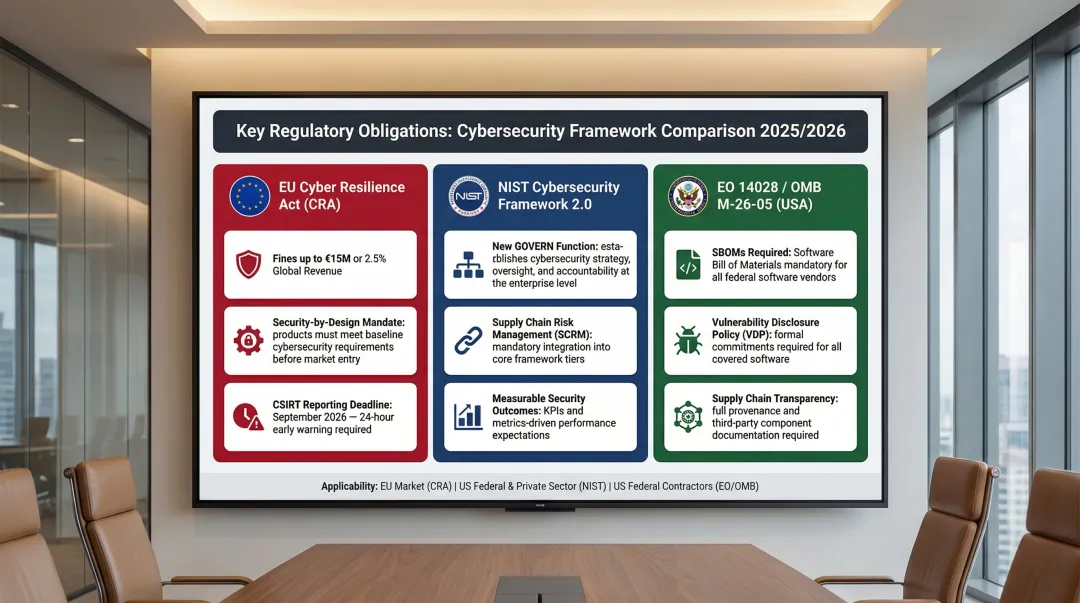
Procurement implication: Compliance obligations flow upstream to vendors and device manufacturers. Enterprise procurement teams need security attestations, SBOMs, and vulnerability disclosure commitments as baseline contract requirements—not optional additions.
How Boards and Executives Should Govern IoT Risk
The Decision Rights Problem
In most enterprises, IoT security ownership is ambiguous—IT says it belongs to OT, OT says it belongs to IT, and the CISO lacks authority over devices installed by facilities or business units. Boards need to demand clarity on three things:
- Who owns IoT risk?
- Who has authority to enforce controls?
- What is the escalation path when something goes wrong?
Without clear decision rights, IoT security remains a technical aspiration, not a governed capability.
Board-Level IoT Risk Reporting
Board reporting should not include device-level technical trivia. It should provide trend indicators that show direction:
- Percentage of inventory with active vendor support
- Mean time to patch critical vulnerabilities
- Number of unresolved high/critical CVEs
- Anomalous behavioral detections in the quarter
Stable metrics that show whether risk is increasing or decreasing over time enable boards to make informed decisions about funding, risk acceptance, and vendor accountability.
The 90-Day Governance Accelerator
Organizations lacking a mature IoT security posture can move meaningfully in 90 days if they start with three things:
- A complete device inventory covering IT, OT, and building systems
- Documented decision rights assigning ownership and escalation paths
- A prioritized remediation plan with named owners and measurable outcomes
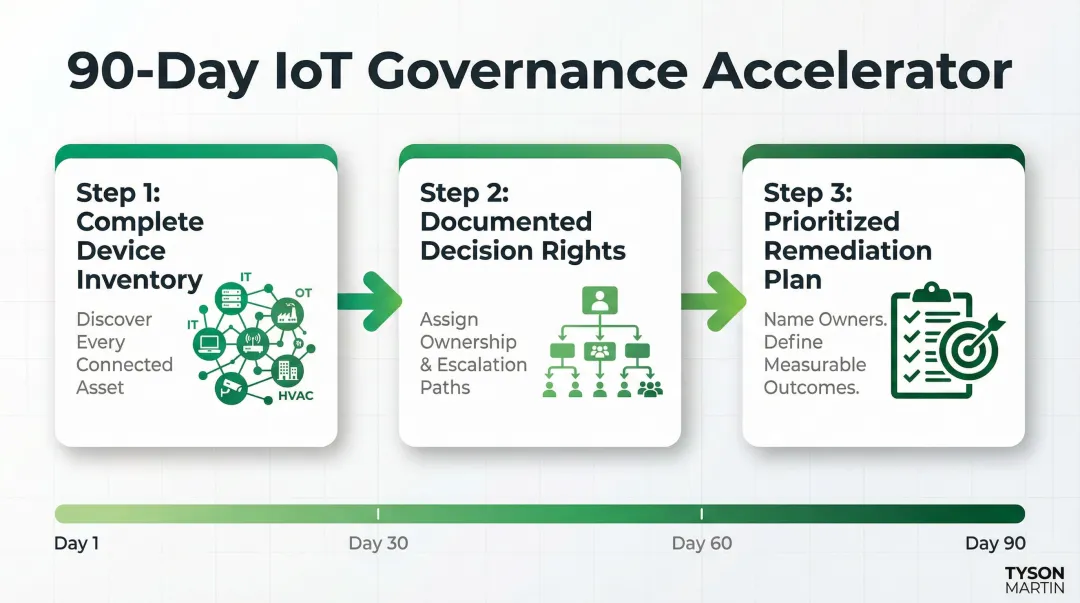
Organizations without a dedicated CISO often find a fractional arrangement the fastest way to build this structure without waiting on a full-time hire.
The Board's Role in Supplier Accountability
Boards should ask whether IoT vendor contracts include:
- Security SLAs with defined response times for vulnerability disclosure and patching
- Patch commitments specifying support duration and update cadence
- Liability provisions for security failures or breached devices
- SBOM delivery requirements
Many contracts do not. Closing that gap is a board-level responsibility, not something to delegate down to procurement.
Frequently Asked Questions
What is an enterprise security strategy?
An enterprise security strategy is a coordinated set of policies, controls, and governance frameworks that protect an organization's assets, data, and operations. In 2026, any credible strategy treats IoT as a distinct risk domain — with its own visibility tools, access controls, and incident response playbooks.
What is the enterprise software security framework?
The most common frameworks for enterprise IoT security are NIST CSF 2.0, ISO 27001, and IEC 62443 for operational technology (OT) environments. Each provides structured controls that help organizations map regulatory obligations and risk priorities against a consistent, measurable baseline.
What are the 5 security objectives?
The NIST Cybersecurity Framework defines five core functions: Identify, Protect, Detect, Respond, and Recover. For IoT environments, the two most commonly underdeveloped are Identify — most enterprises lack a complete device inventory — and Detect, where behavioral monitoring of IoT traffic is still rare.
What are the three pillars of the CIA triad?
The CIA triad defines Confidentiality, Integrity, and Availability as the three pillars of information security. For IoT environments, Availability is often the most critical pillar because devices control physical systems or operational processes where downtime creates safety risks or business disruption.
What are the 3 Cs of enterprise security?
The three Cs are Confidentiality, Control, and Compliance. For IoT security in 2026, Control over unmanaged devices and Compliance with emerging regulations are the sharpest gaps — the EU Cyber Resilience Act and NIST CSF 2.0 are now creating enforceable standards where none existed before.