](https://file-host.link/website/tysonmartin-zzqimp/assets/blog-images/29afb18d-4c01-41e9-81aa-ff23317c7e49/1777284841054690_602a3efe373845f58fdb3de61948319f/360.webp)
Introduction
Today's CISOs operate under mounting pressures that compound faster than internal teams can address. 53% of CISOs experienced or witnessed burnout in the past 12 months, while breach costs hit a record $4.88 million average globally. Meanwhile, regulatory mandates like SEC disclosure rules and NIS2 bring direct personal liability to security leadership.
That personal exposure makes internal blind spots a real liability. Bandwidth limits, organizational politics, and the gap between technical risk and board-defensible decisions don't disappear with experience — they compound it.
Cybersecurity advisory services aren't replacements for CISO leadership. They bring outside perspective, board-level credibility, and decision-ready framing to exactly the moments where internal teams are most stretched: major transitions, high-stakes incidents, and the quarterly reporting cycle that now carries legal weight.
TL;DR
- Advisory services provide an independent risk perspective, stronger board communication, and faster decisions during high-stakes situations
- Advisors bridge the gap between technical teams and executives—translating risk into business language boards can act on
- Without advisory support, organizations react to incidents instead of governing through them—and the cost difference is significant
- The most value comes when advisory is an ongoing governance practice, not a one-time audit or emergency call
- For CISOs in regulated industries, mid-transition, or under board scrutiny, advisory support is a governance priority—not a luxury
What Are Cybersecurity Advisory Services?
Cybersecurity advisory services are senior-level expertise that works alongside the CISO to sharpen governance, improve board reporting, and strengthen decision-making—without replacing the internal security function. Unlike technical consulting that delivers project-specific work, advisory engagements provide strategic oversight that persists across quarters and leadership changes.
Typical application areas include:
- Board and executive reporting frameworks that translate technical metrics into business impact
- Governance structure design with clear decision rights and escalation thresholds
- Risk prioritization that connects security investments to measurable business outcomes
- Incident preparedness reviews that validate response capability before crises occur
- M&A and transition support that protects deal value and leadership continuity
- Regulatory alignment roadmaps for frameworks like SEC disclosure rules, NIS2, HIPAA, and PCI DSS

The goal is straightforward: better decisions, cleaner escalation, and a security posture the board can inspect and act on. That requires an ongoing advisory relationship, not a one-time report.
Key Advantages of Cybersecurity Advisory Services
The advantages below focus on operational and governance outcomes that CISOs, boards, and executive teams directly experience. Each connects to metrics organizations track: risk reduction, board confidence, cost of response, regulatory standing, and leadership continuity.
An Independent View That Exposes What Internal Teams Miss
One of the most consistent limitations of internal security programs is the absence of outside perspective. CISOs embedded in day-to-day operations often normalize risk that an external advisor would immediately flag.
Advisors bring cross-industry experience—across enterprise environments, regulated sectors, and high-stakes incidents—that no single organization can replicate internally. This lets them benchmark your posture against what "good" actually looks like elsewhere.
Independent advisors identify governance gaps, misaligned priorities, and reporting blind spots before they become incidents or audit findings—reducing reactive firefighting. The Verizon 2025 Data Breach Investigations Report found that only 54% of vulnerabilities are fully remediated, with a median patch time of 32 days. Many breaches originate from known but unmitigated risks that internal teams have already documented but failed to prioritize.
When a CISO can validate their risk posture against an independent view, executive and board decisions become more defensible. Organizations with severe security staffing shortages averaged $5.74 million per breach compared to $3.98 million for adequately staffed peers—a $1.76 million difference. That gap closes faster with an experienced external advisor than with a hiring cycle that takes months to complete.
KPIs impacted:
- Risk exposure score
- Number of unmitigated known vulnerabilities
- Time-to-escalation on critical issues
- Reduction in reactive incident spend
When this advantage matters most:
Independent perspective delivers highest value during organizational growth, technology modernization, M&A activity, or when a new CISO is establishing credibility with the board.
Board-Ready Communication That Drives Governance, Not Just Reporting
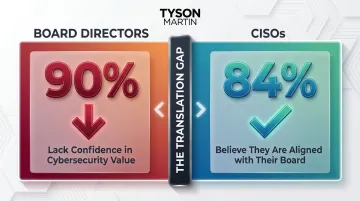
Most boards want to understand cyber risk in terms of business impact—revenue, regulatory exposure, operational continuity—not technical metrics. Yet 90% of non-executive directors lack confidence in cybersecurity value, while 84% of CISOs believe they're aligned with their board. This perception gap signals a translation failure that advisory services are designed to close.
How advisory services create this advantage:
Advisors help design stable dashboards that show trend not trivia, develop plain-English risk briefings that communicate what changed and why it matters, and clarify decision rights so boards govern rather than micromanage.
When boards receive clear, consistent, and contextualized security reporting, they fulfill their oversight role confidently—reducing regulatory scrutiny and protecting the CISO from personal liability when incidents occur. With SEC disclosure rules requiring 4-business-day material incident disclosure and NIS2 allowing temporary suspension of management for non-compliance, defensible communication with the board is no longer optional.
KPIs impacted:
- Board confidence in security reporting
- Frequency of security escalations requiring board intervention
- Time spent preparing board materials
- Audit committee satisfaction
When this advantage matters most:
Board communication support is most critical for CISOs in regulated industries, publicly traded companies, organizations undergoing governance reform, or those that have recently experienced an incident requiring board-level response.
Faster, More Defensible Response During High-Stakes Transitions
Organizations in transition—new leadership, M&A, a cyber incident, or digital transformation—face compressed timelines where governance gaps become crises and poor decisions carry lasting consequences. Experienced advisors bring structured frameworks and pattern recognition from similar situations, enabling CISOs to move quickly without improvising under pressure.
How advisory services create this advantage:
Advisors establish decision rights, escalation thresholds, and 90-day execution plans with measurable outcomes. Having an advisor engaged before a crisis means the response structure is already in place—the organization doesn't start building governance when it's already under stress.
Organizations with extensive use of security AI and automation had average breach costs of $3.84 million versus $5.72 million for those without—a $1.88 million saving. Mature governance structures reduce both breach likelihood and response cost. Advisory support during leadership transitions or M&A also protects institutional security knowledge, ensuring the incoming leader inherits a stable, inspectable program.
The average CISO tenure is just 18–26 months, compared to approximately 4.9 years for other C-suite roles—meaning advisory continuity carries institutional memory that leadership turnover erodes. In M&A scenarios, Yahoo's breach disclosure led to a $350 million acquisition price reduction, demonstrating how advisory due diligence directly protects deal value.
KPIs impacted:
- Mean time to contain incidents
- Cost per incident
- Leadership transition stability metrics
- Time to establish functional governance post-M&A
When this advantage matters most:
This advantage is highest during CISO turnover, active M&A due diligence, post-breach recovery, or large-scale digital or cloud transformation programs.
What Happens When Advisory Support Is Absent
CISOs without external advisory input often operate in a governance silo, building programs based on internal assumptions rather than validated external benchmarks. This leads to inconsistent risk prioritization and reactive firefighting.
Without a structured communication layer, boards receive noise rather than signal: they either over-intervene on tactical issues or under-invest in genuine risk reduction. Both create long-term liability.
Gaps that go unaddressed in routine operations become critical vulnerabilities during incidents, audits, or leadership transitions — exactly the moments when advisory support is most costly to lack. The data confirms the pattern:
- Security system complexity was the top factor increasing breach costs in 2024, adding $261,358 above the global average
- Organizations with shadow data (unmanaged data sources) faced breach costs 16.2% above average
- Third-party involvement in breaches doubled from 15% to 30% in just one year
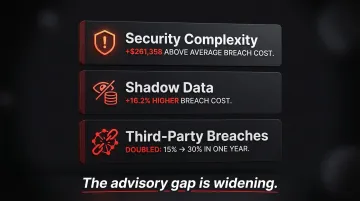
Meanwhile, 35% of small organizations now report their cyber resilience is insufficient — a sevenfold increase since 2022. The advisory gap is widening, not narrowing.
How to Get the Most Value from Cybersecurity Advisory Services
Advisory services deliver the most value when the advisor has both deep technical credibility and executive communication experience—the ability to operate at the board level and in the security weeds without losing either audience. When evaluating candidates, prioritize verified enterprise backgrounds over certification lists. Credentials matter; direct experience leading security programs at scale matters more.
Outcomes also need a regular review cadence — not just a report that sits in a folder. The most effective advisory relationships maintain a live governance rhythm with:
- Stable metrics that show trend, not just point-in-time snapshots
- Clear owners for each priority area
- Escalation thresholds that hold when an actual incident hits
A fractional or board-level advisor provides this kind of oversight without the cost of a permanent hire. Tyson Martin works with boards and executive teams in this capacity — drawing on security leadership experience at AWS and Fortune 100 retailers, active roles at NACD and the World Economic Forum's Centre for Cybersecurity, and a structured engagement model built around 90-day plans, stable dashboards, and clear decision rights.
Conclusion
Cybersecurity advisory services give CISOs an independent view, give boards the reporting they need to govern effectively, and give organizations the structure to respond when it matters. The advantages build over time: advisory relationships embedded in governance rhythms produce cleaner escalation paths, more defensible decisions, and a security posture the entire organization can inspect and trust.
Advisory services should be treated as an ongoing leadership practice—not a one-time engagement triggered only by crisis—because organizations that build this infrastructure before an incident can make decisions under pressure that hold up to scrutiny afterward.
Frequently Asked Questions
What is a cyber security advisory?
Cybersecurity advisory is senior-level expert guidance—distinct from technical consulting—that helps organizations improve governance, risk communication, and decision-making around cybersecurity. Advisors provide ongoing strategic oversight rather than project-specific deliverables.
What are the 5 C's of cybersecurity?
The 5 C's—Change, Compliance, Cost, Continuity, and Coverage—are a practitioner heuristic for evaluating whether a cybersecurity program adapts to change, meets regulatory requirements, fits budget realities, supports business continuity, and covers the full organizational attack surface.
How is a cybersecurity advisor different from a cybersecurity consultant?
An advisor provides ongoing strategic and governance-level guidance (often fractional or board-level) with long-term executive accountability. A consultant typically delivers tactical, project-specific work without ongoing governance responsibility or executive-level decision rights.
When should a CISO seek external cybersecurity advisory support?
Key triggers include leadership transitions, M&A activity, post-incident recovery, board scrutiny, regulatory changes, or when internal reporting isn't resonating with executive leadership. Advisory support is also valuable when establishing a new CISO function or entering an audit committee review cycle.
What is the role of a cybersecurity advisor at the board level?
A cybersecurity advisor translates technical risk into business language, helps boards fulfill their oversight duties, and ensures cybersecurity is treated as a governance priority rather than an IT function. They provide independent risk assessment, validate management reporting, and help boards make defensible decisions.
Can a cybersecurity advisor help with regulatory compliance?
Yes. Advisors map current controls against applicable frameworks (HIPAA, PCI DSS, SEC disclosure rules, NIS2), identify gaps, and build prioritized roadmaps that reduce legal and financial exposure while navigating regulatory fragmentation across jurisdictions.